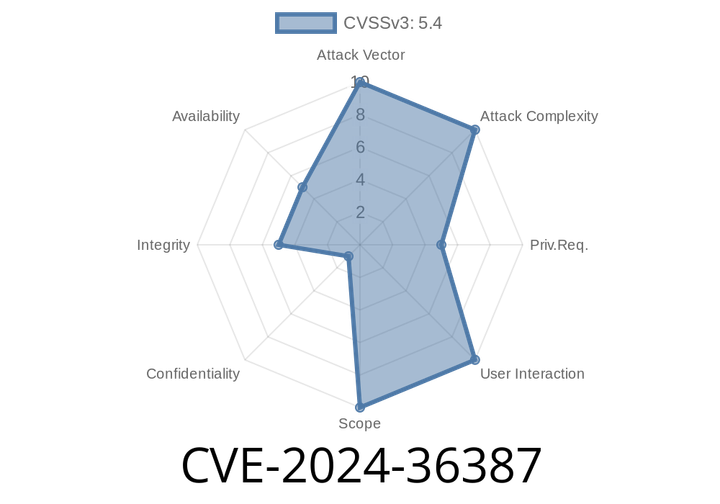
CVE-2024-36387 - WebSocket Upgrades Over HTTP/2 Cause Null Pointer Dereference and Server Crashes
In June 2024, a critical vulnerability—CVE-2024-36387—was disclosed in popular web server software. This flaw allows attackers to crash server processes by attempting WebSocket
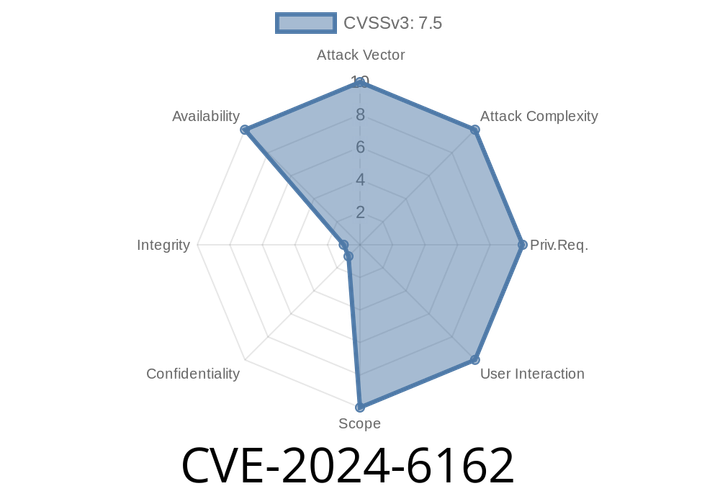
CVE-2024-6162 - Undertow AJP Listener Path Confusion Explained with Code, Exploit, and Fix
On June 19, 2024, security researchers discovered a vulnerability in Undertow, a flexible and performant Java web server. Tracked as CVE-2024-6162, this flaw lets attackers
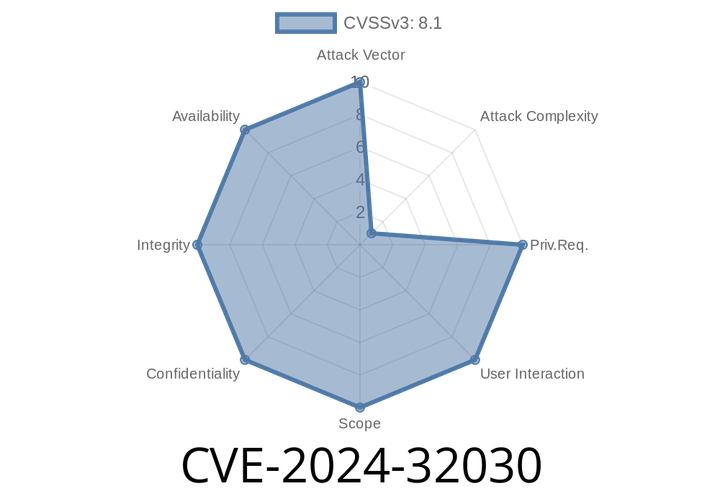
CVE-2024-32030 - Remote Code Execution in Kafka UI via JMX/RMI Deserialization
A high-severity vulnerability, CVE-2024-32030, was found in Kafka UI, a popular open-source tool for managing Apache Kafka clusters. The flaw allows attackers to execute arbitrary
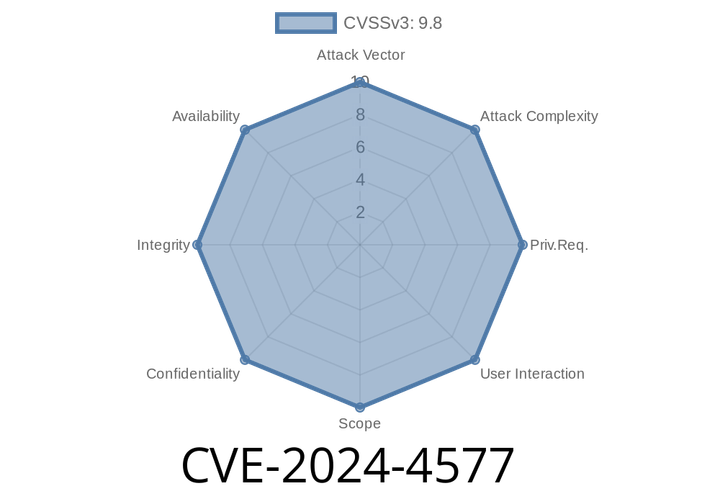
CVE-2024-4577 - PHP CGI "Best-Fit" Unicode Encoding Flaw on Windows Lets Attackers Run Arbitrary Code
In June 2024, security researchers revealed a severe vulnerability affecting PHP when deployed through CGI under Apache on Windows. The issue, tracked as CVE-2024-4577, lets
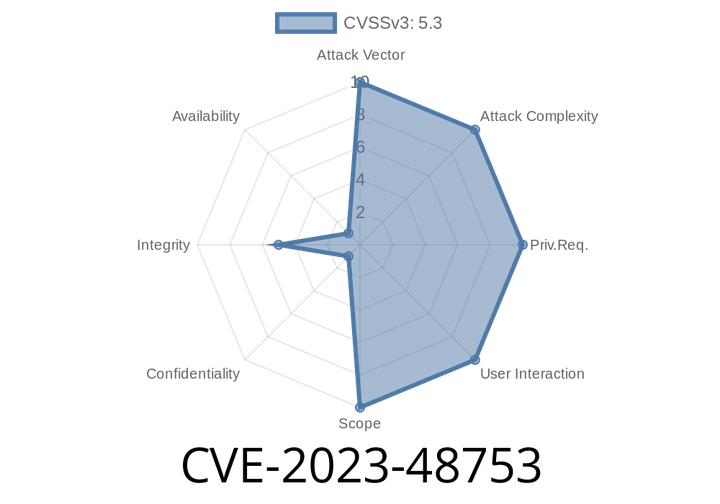
CVE-2023-48753 - Authentication Bypass in 10up Restricted Site Access Plugin – Exploit Explained
Summary:
CVE-2023-48753 is a critical vulnerability in the “Restricted Site Access” WordPress plugin by 10up. This flaw, termed as “Authentication Bypass by Spoofing,” lets attackers
Episode
00:00:00
00:00:00