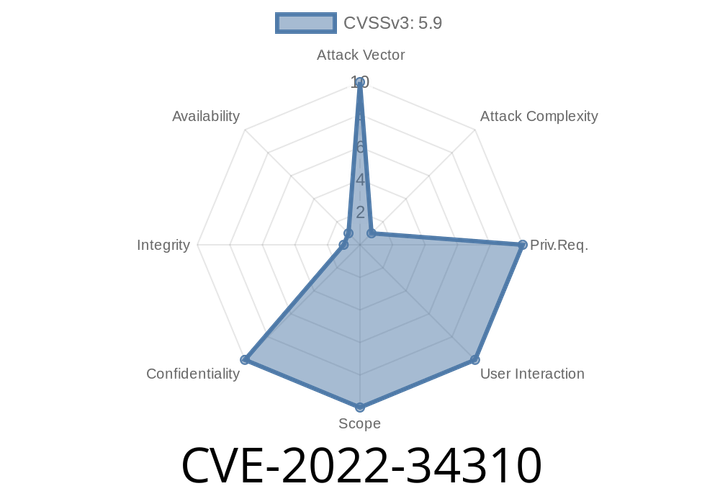
CVE-2022-34310 - Weak Cryptography in IBM CICS TX v11.1 Explained with Exploit Details
Cybersecurity is full of complex terms, but sometimes the risks can be surprisingly simple. That’s the case with CVE-2022-34310, a vulnerability in IBM CICS
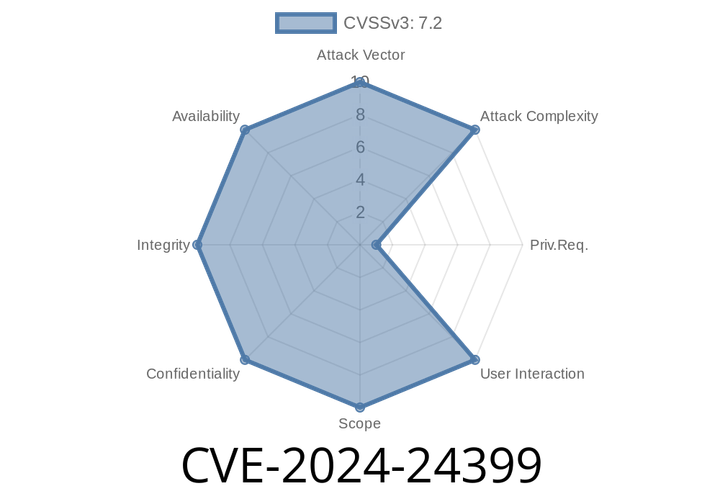
CVE-2024-24399 - Arbitrary File Upload in LEPTON v7.. — Exploiting the Language Backend
Security researchers have discovered a critical vulnerability: CVE-2024-24399 in LEPTON CMS v7... This flaw allows authenticated attackers to upload arbitrary PHP files via the backend
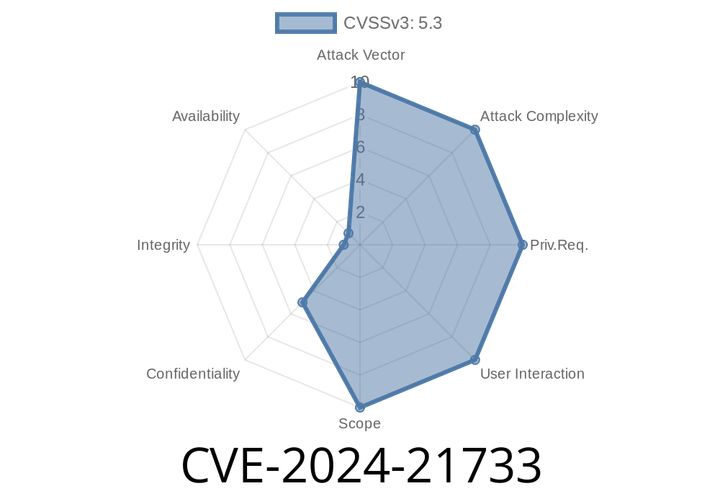
CVE-2024-21733 - Apache Tomcat Leaks Sensitive Info in Error Messages – How It Happens, How to Exploit, & How to Fix
---
In early 2024, the Apache Software Foundation disclosed a security risk affecting millions of Tomcat servers worldwide. Known as CVE-2024-21733, this vulnerability could cause
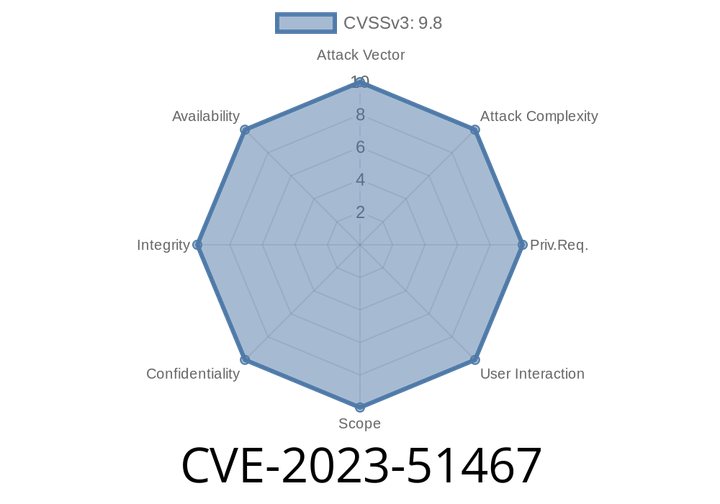
CVE-2023-51467 - How Attackers Bypass Authentication to Execute Code Remotely
---
Introduction
One of the most talked-about vulnerabilities in late 2023 is CVE-2023-51467, a severe bug that allows attackers to bypass authentication and execute arbitrary
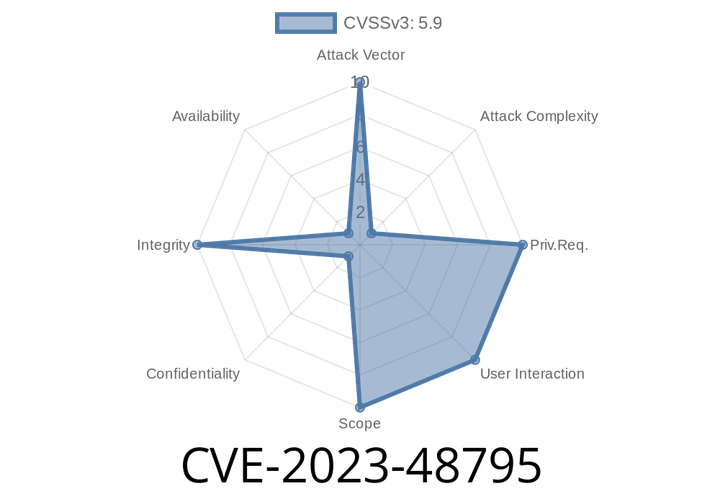
CVE-2023-48795 - Understanding the Terrapin Attack — Breaking the Integrity of SSH Connections
*Posted in June 2024 by Security Research Exchange*
Introduction
If you’re using SSH to connect to servers, transfer files, or manage devices, you likely
Episode
00:00:00
00:00:00