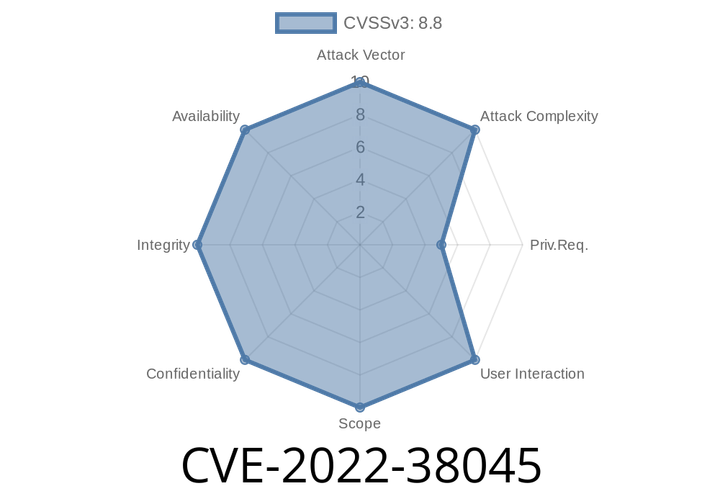
CVE-2022-38045 Server Service Remote Protocol Elevation of Privilege Vulnerability.
In this blog, we are going to explain how to exploit the CVE-2019-0554 server service remote protocol elevation of privilege vulnerability, in order to gain
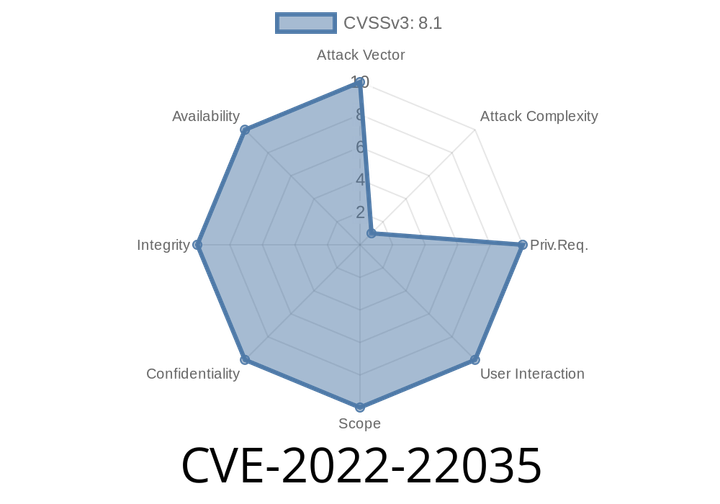
CVE-2022-22035 Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability
These vulnerabilities allow an attacker to execute arbitrary code in the context of the service session, which could lead to a complete hijack of the
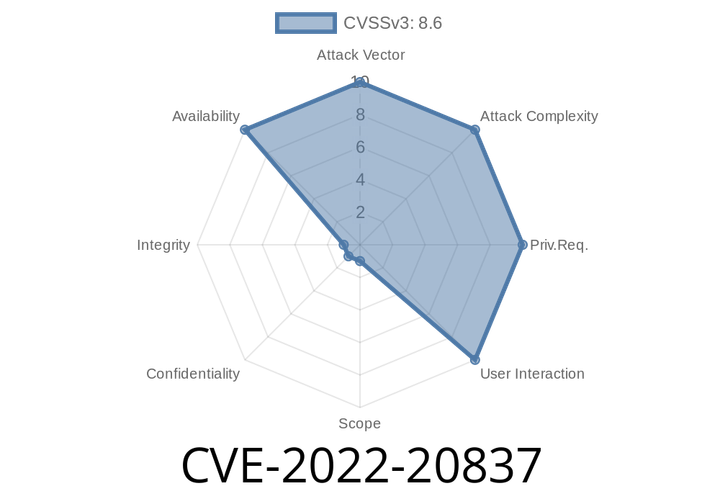
CVE-2022-20837 DNS ALG vulnerability could allow unauthenticated, remote attacker to cause affected device to reload.
This vulnerability has been assigned the ID CVE-2018-6389. Cisco has released software updates that address these vulnerabilities. However, if you have enabled the Cisco Nexus
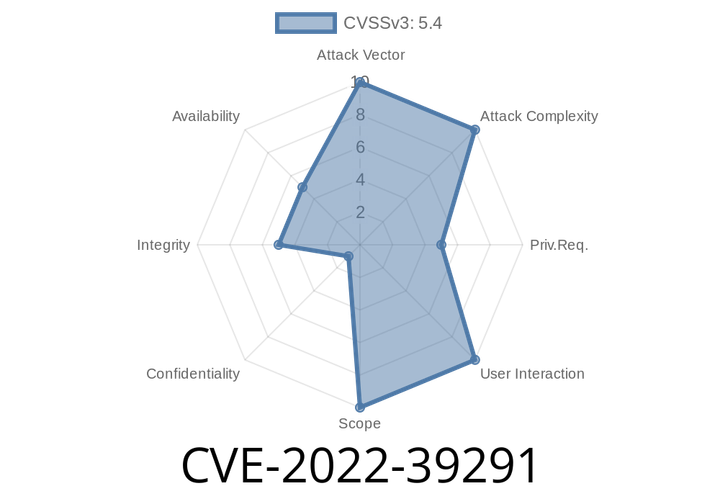
CVE-2022-39291 Affected versions of zoneminder are vulnerable to a vulnerability which allows users with "View" system permissions to inject new data into the logs stored by Zoneminder.
ZmMiner is a php script that hooks into the zoneminder logging system and is used to extract data from the server and display it in
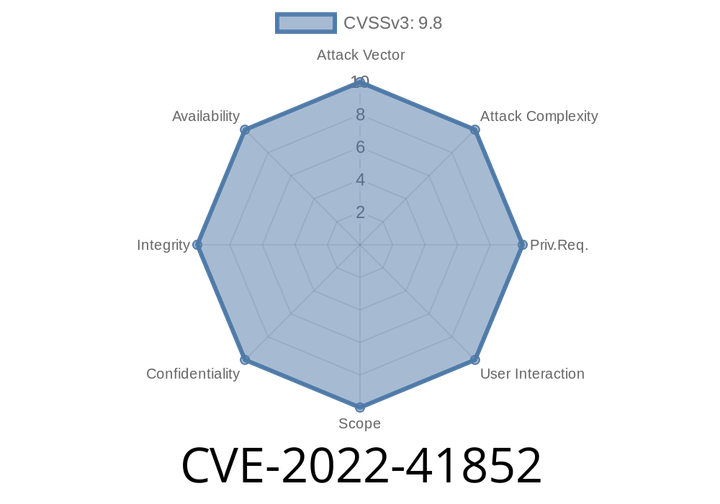
CVE-2022-41852 JXPath may be vulnerable to a remote code execution attack when using functions that process XPath strings. Compile() and compilePath() are safe.
An attacker can craft an XPath string to load any class of his/her choice using an external source, such as an XML file.
JXPath
Episode
00:00:00
00:00:00