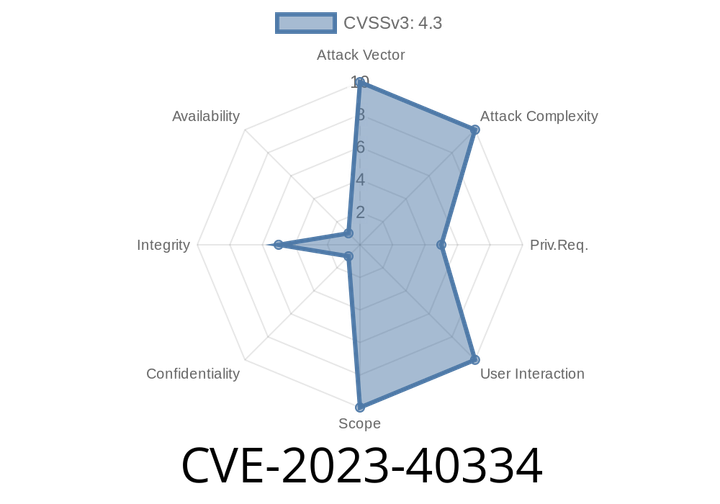
CVE-2023-40334 - How Missing Authorization in HUSKY Opens Up Security Risks (With Exploit Example)
The open-source project HUSKY by realmag777 is a popular tool used in various web applications for plugin management and automation. Keeping an eye on its
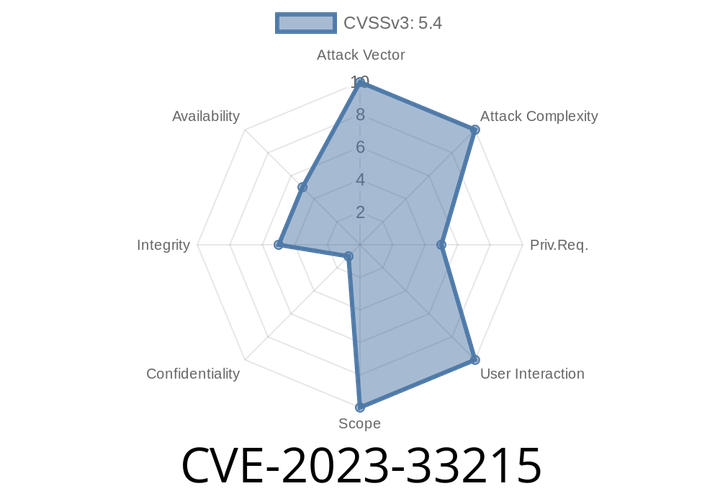
CVE-2023-33215 - How a Missing Authorization Vulnerability in Tagbox Taggbox Lets Attackers Bypass Access Controls
Date: June 2024
Author: SecureCode Insights
In May 2023, a serious security flaw (CVE-2023-33215) was discovered in Taggbox, also known as Tagbox Taggbox, a popular
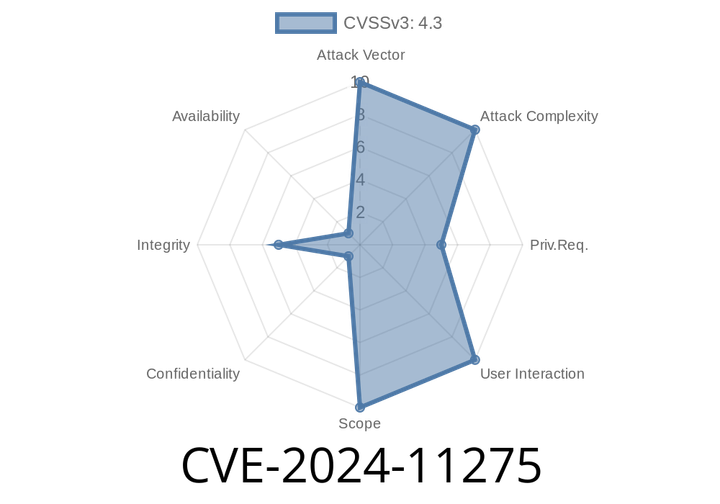
CVE-2024-11275 - Critical Vulnerability in WP Timetics Plugin Lets Customers Delete Any Users – Full Analysis & Exploit Demo
Discovered: Early 2024
Severity: High
Affected Plugin: WP Timetics
Vulnerable Versions: ≤ 1..27
Plugin Purpose: Appointment booking & scheduling with AI features
Bug Type: Broken
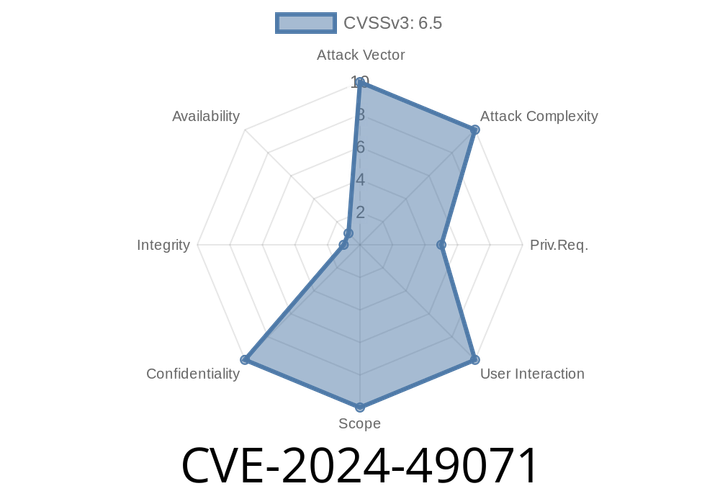
CVE-2024-49071 - How Windows Defender’s Global Files Search Leaks Sensitive Info With Improper Authorization
June 2024 has seen another serious security issue: CVE-2024-49071, a privilege escalation vulnerability in Windows Defender. This bug exposes sensitive index information to attackers with
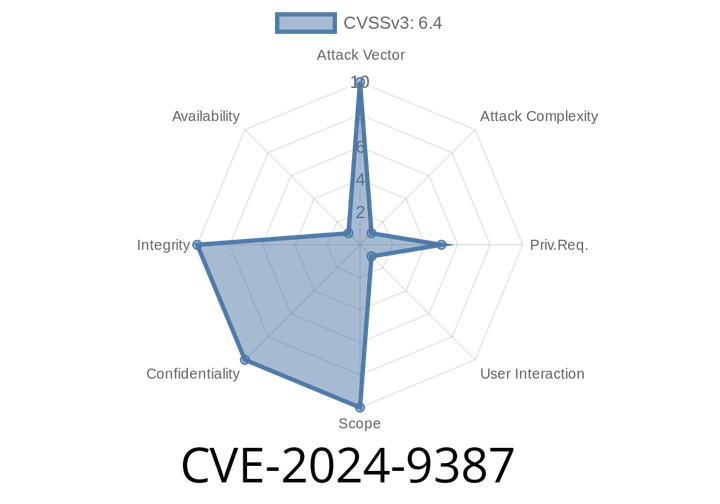
CVE-2024-9387 - Exploiting Open Redirect in GitLab Releases API (11.8–17.6.2)
An open redirect vulnerability is often considered low-to-medium risk—but, in the wrong hands, it can be used for phishing, stealing credentials, or leading users
Episode
00:00:00
00:00:00