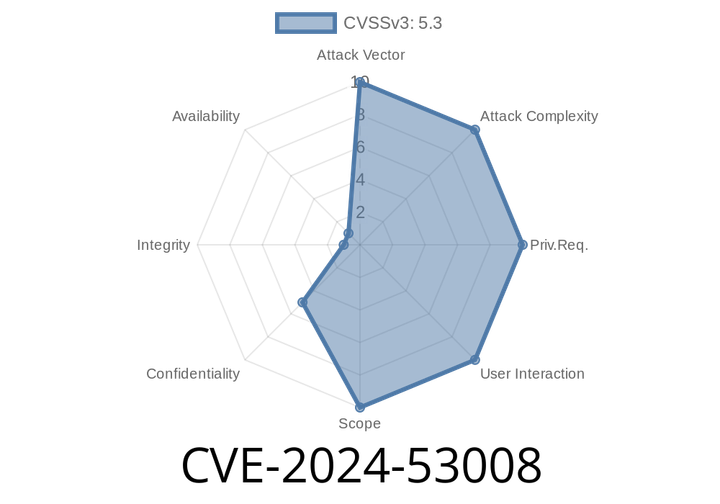
CVE-2024-53008 - Exploiting HAProxy’s HTTP Request Smuggling to Bypass ACLs and Steal Sensitive Data
A new vulnerability, CVE-2024-53008, was recently discovered in HAProxy, a popular open-source software widely used for high-performance TCP/HTTP load balancing. The flaw is classified
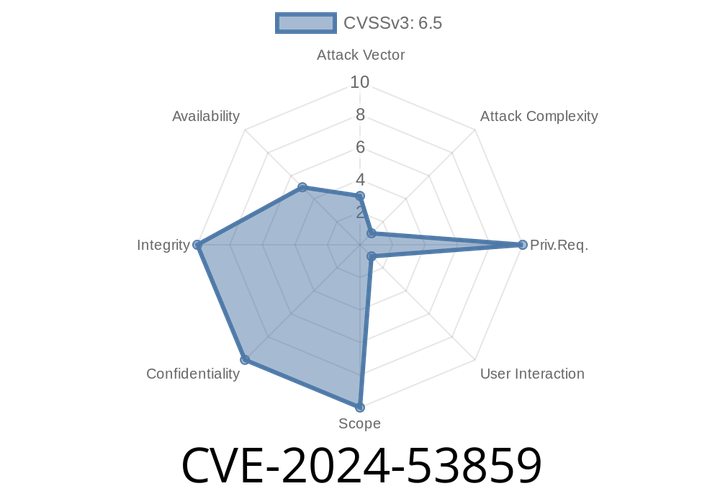
CVE-2024-53859 - Token Leakage Vulnerability in go-gh – Details, Code Snippet, and Exploit Explained
A security flaw, CVE-2024-53859, was found in the go-gh Go module—the common package used for interacting with the GitHub CLI (gh) and the GitHub
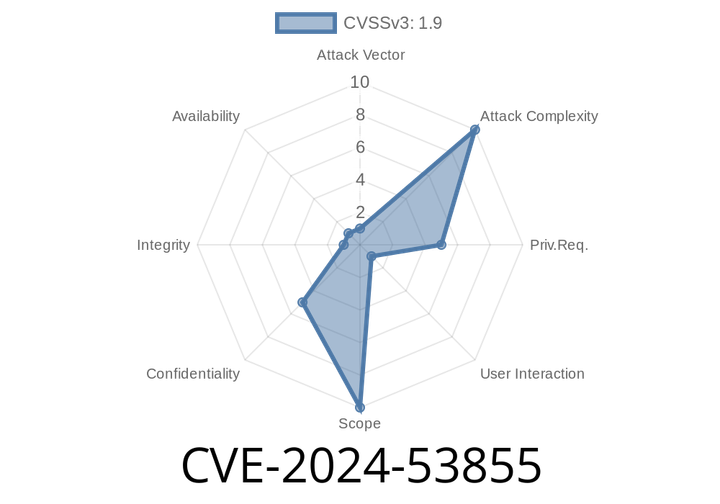
CVE-2024-53855 - API Ticket Data Leakage in Centurion ERP – Exploit, Details, and Solutions
In June 2024, a security vulnerability was found in Centurion ERP, a popular open-source IT management tool focused on IT Service Management (ITSM) modules. This
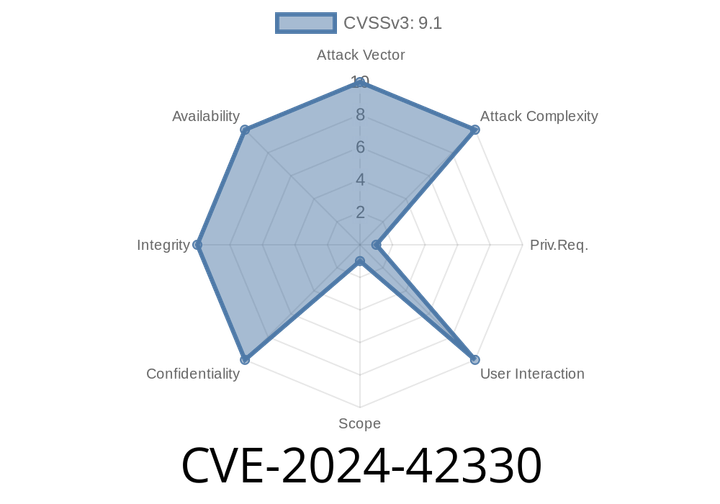
CVE-2024-42330 - Exploiting HttpRequest Object’s Header Handling for Prototype Pollution in JavaScript
In June 2024, CVE-2024-42330 shed light on a subtle but powerful security flaw involving the HttpRequest object in common JavaScript libraries and environments. The vulnerability
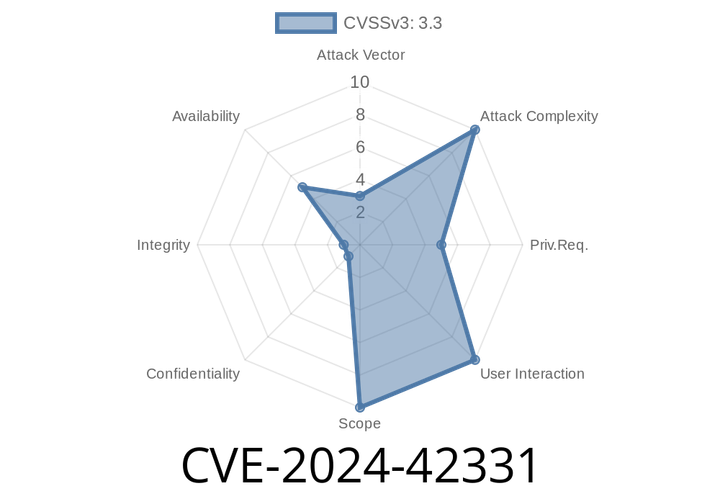
CVE-2024-42331 - Understanding the Use-After-Free Bug in Zabbix’s Duktape Integration
On June 2024, a critical security vulnerability was disclosed in Zabbix, an enterprise-grade open source monitoring tool. This bug, CVE-2024-42331, centers on a use-after-free error
Episode
00:00:00
00:00:00