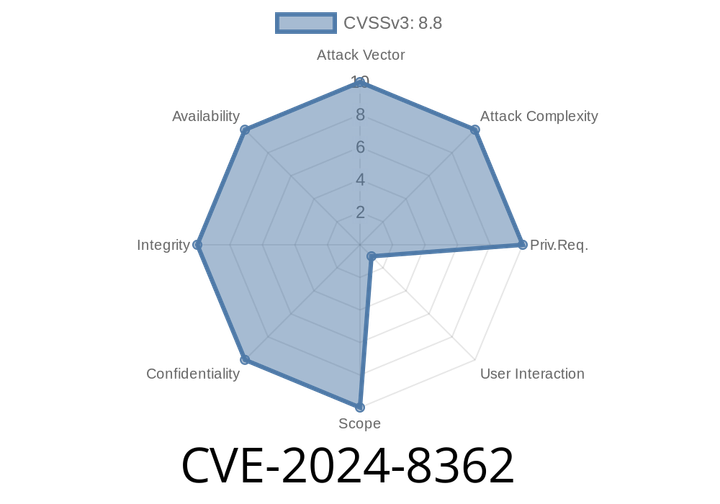
CVE-2024-8362 - Exploiting a Use-After-Free in Chrome WebAudio (Pre-128..6613.119) – Explanation, Details, and Example
---
Introduction
A critical security vulnerability, CVE-2024-8362, was discovered in Google Chrome's WebAudio implementation. This bug lets remote attackers potentially cause heap corruption
CVE-2024-41436 - How a Buffer Overflow in ClickHouse v24.3.3.102 (DB::evaluateConstantExpressionImpl) Risks Your Data
In early June 2024, a severe buffer overflow vulnerability—CVE-2024-41436—was uncovered in ClickHouse v24.3.3.102. The security hole exists in the DB:
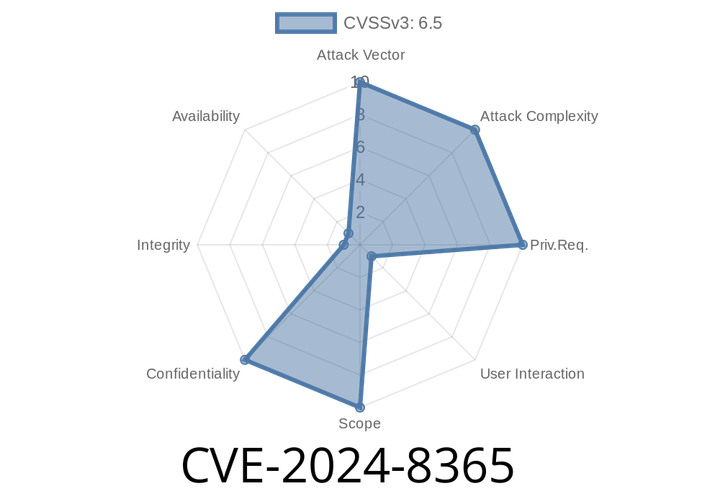
CVE-2024-8365 - How HashiCorp Vault Leaked Your Tokens in Plaintext Audit Logs
On June 12, 2024, a critical vulnerability was disclosed that put sensitive secrets at risk for many organizations using HashiCorp Vault. Known as CVE-2024-8365, this
CVE-2023-26315 - Post-Auth Command Injection in Xiaomi Router AX900 Breakdown
If you own a Xiaomi Router AX900, you should be aware of a serious security issue discovered earlier this year—CVE-2023-26315. This vulnerability lets an
CVE-2024-42340 - Breaking Down CyberArk’s Dangerous Client-Side Security Flaw (CWE-602)
In June 2024, a critical security vulnerability was disclosed in the CyberArk Privileged Access Security (PAS) Solution, tracked as CVE-2024-42340. This vulnerability is rooted in
Episode
00:00:00
00:00:00