CVE-2025-24786 - WhoDB Path Traversal Vulnerability Exposes Any Sqlite3 Database On The Host
WhoDB is an open-source, user-friendly database management tool commonly used for easily exploring and handling Sqlite3 databases. In early 2025, security researchers discovered a critical
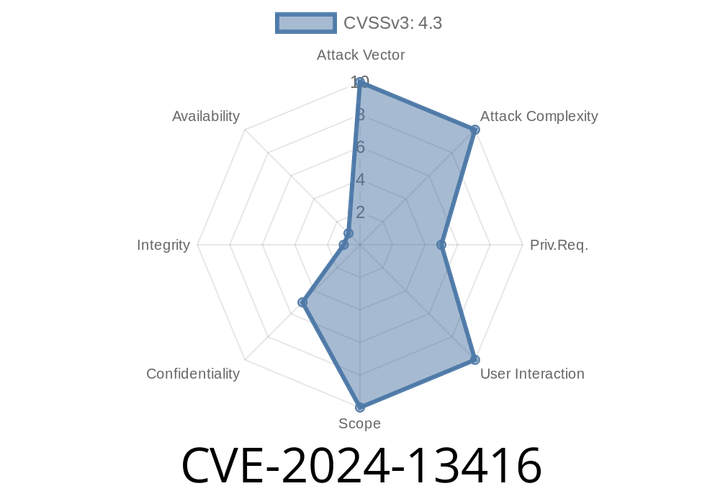
CVE-2024-13416 - API Logging in 2N OS Leaks Authentication Tokens
On some 2N intercom devices running legacy or outdated versions of 2N OS (before v2.46), a serious security flaw can leak authentication tokens. Attackers
CVE-2025-23217 - SSRF to Possible Remote Code Execution in mitmweb (mitmproxy <= 11.1.1)
mitmproxy is a popular open-source intercepting proxy, widely used by penetration testers and software developers for troubleshooting and inspecting HTTP/S traffic. It also offers
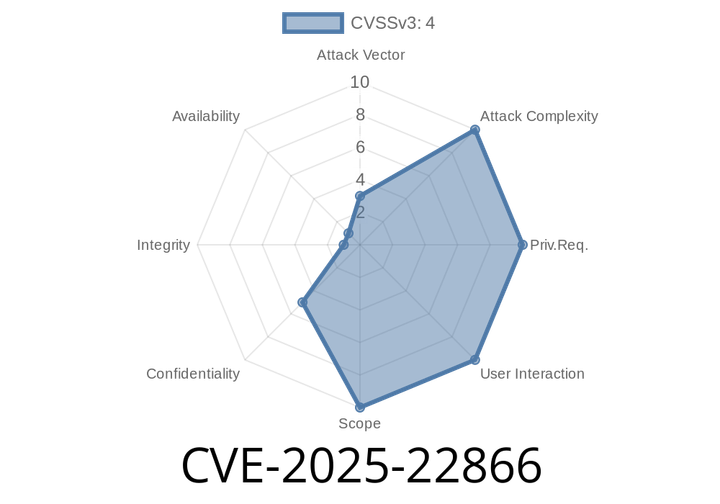
CVE-2025-22866 - Understanding Scalar Secret Leak in Cryptographic Assembly on ppc64le
Recently, the vulnerability CVE-2025-22866 was identified in the assembly implementation of an internal cryptographic function on the ppc64le architecture (PowerPC 64-bit Little Endian). This vulnerability
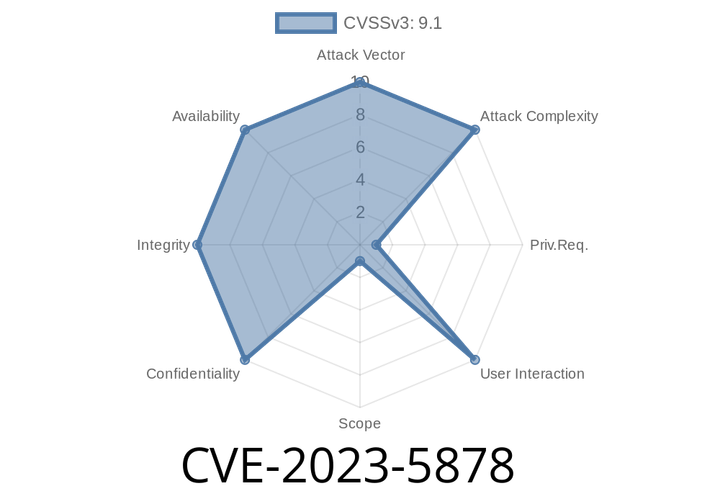
CVE-2023-5878 - Command Injection in Honeywell OneWireless WDM - Analysis and Exploitation
Industrial systems are not immune to software vulnerabilities. One notable recent example is CVE-2023-5878, affecting critical infrastructure deployed by Honeywell. This vulnerability puts several releases
Episode
00:00:00
00:00:00