CVE-2024-8686 - How Hackers Can Take Over Palo Alto Firewalls With One Command (With Exploit Example)
CVE-2024-8686 is a newly disclosed command injection vulnerability that affects Palo Alto Networks’ PAN-OS software, the underlying system behind their widely-used firewalls. This vulnerability allows
CVE-2024-20483 - Command Injection in Cisco Routed PON Controller Software – Simple Breakdown, Exploit, and Mitigation
CVE-2024-20483 is a critical security vulnerability in Cisco Routed PON Controller Software. This software runs as a Docker container on hardware that supports Cisco IOS
CVE-2024-20398 - Privilege Escalation in Cisco IOS XR Via CLI Argument Injection
A significant vulnerability (CVE-2024-20398) was discovered in Cisco IOS XR Software’s command-line interface (CLI). This flaw allows any authenticated user, even with low-level privileges,
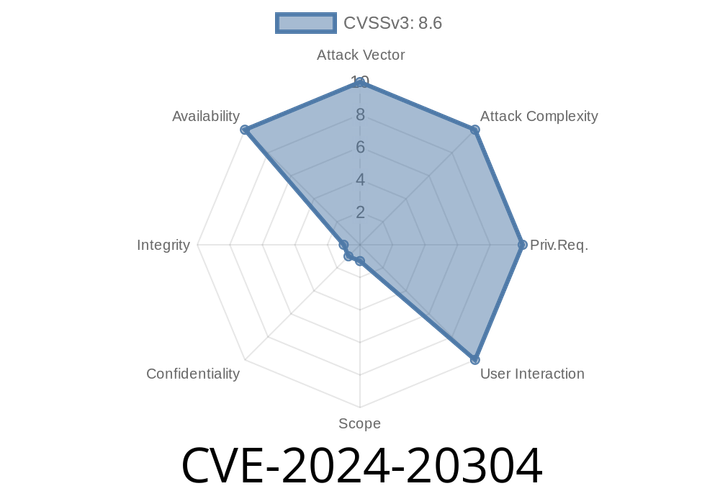
CVE-2024-20304 - Remote UDP Packet Memory Exhaustion in Cisco IOS XR’s Mtrace2 Feature – What You Need to Know
A serious vulnerability, identified as CVE-2024-20304, has been discovered in the Multicast Traceroute version 2 (Mtrace2) feature of Cisco IOS XR Software. This flaw could
CVE-2024-8636 - Heap Buffer Overflow in Skia - How a Crafted HTML Page Can Hack Your Chrome
In early 2024, a serious security bug—CVE-2024-8636—was found in the Skia graphics library, which is used by Google Chrome. Chrome versions before 128.
Episode
00:00:00
00:00:00