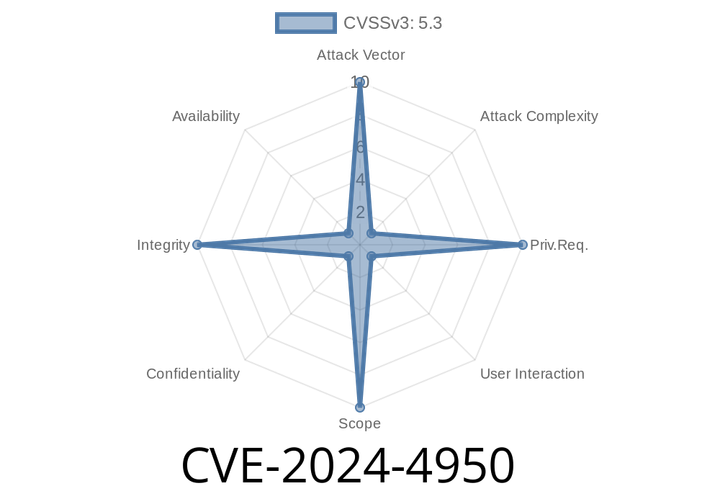
CVE-2024-4950: Inappropriate Implementation in Downloads in Google Chrome Allows Remote Attackers to Perform UI Spoofing
The recently discovered CVE-2024-4950 vulnerability affects Google Chrome versions prior to 125..6422.60 and allows remote attackers to perform UI spoofing via a specifically
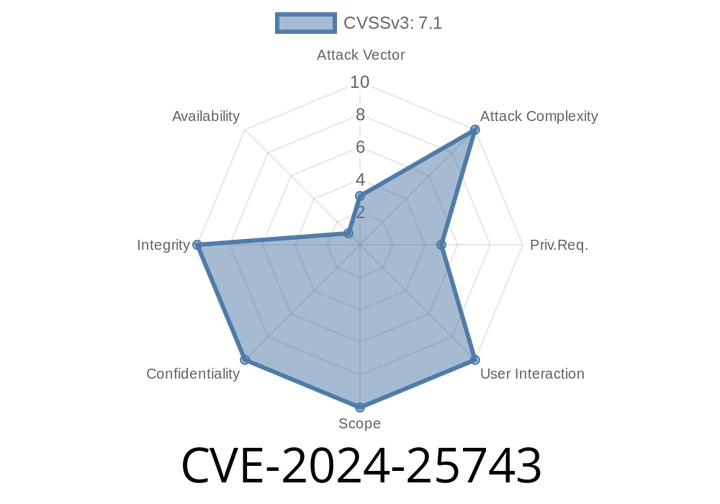
CVE-2024-25743 - Linux Kernel AMD SEV-SNP/SEV-ES Virtual Interrupt Injection Vulnerability Explained
In early 2024, a serious vulnerability—CVE-2024-25743—was discovered in the Linux kernel up to version 6.9. This flaw allows an untrusted hypervisor to
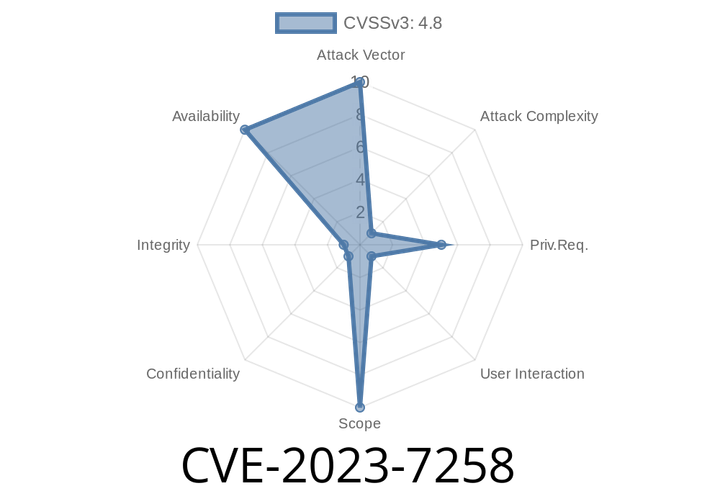
CVE-2023-7258 - Root User Can Crash gVisor Sandbox with Mount Point Reference Counting Bug
---
TL;DR
A bug in how gVisor keeps track of mounted volumes lets a root user crash the sandbox. If they mount and unmount
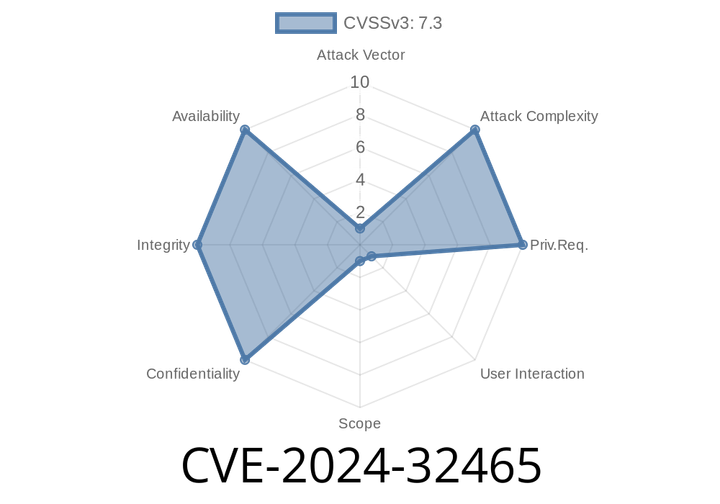
CVE-2024-32465 - How Malicious .zip Archives Threaten Git Users (And How To Stay Safe)
Git is the backbone of version control for millions of developers worldwide. It makes collaboration possible, tracks your changes, and helps you organize code. But
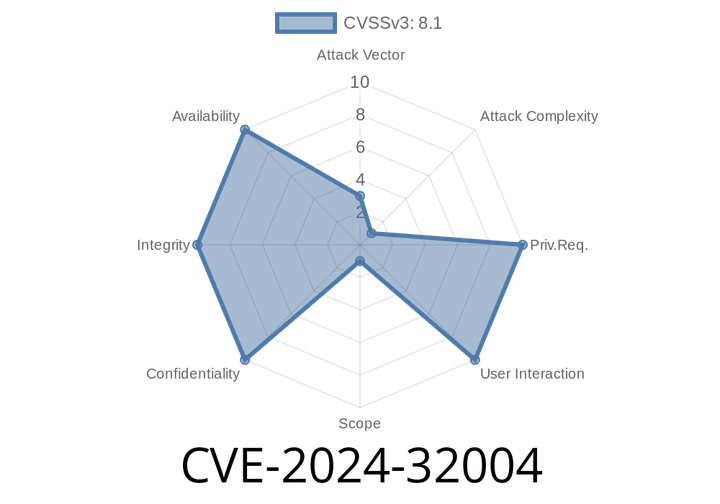
CVE-2024-32004 - Dangerous Git Clone Vulnerability Explained — How Attackers Can Execute Code (with Exploit Details)
In June 2024, a serious security threat was discovered in Git, the world's most popular version control system. This flaw, now known as
Episode
00:00:00
00:00:00