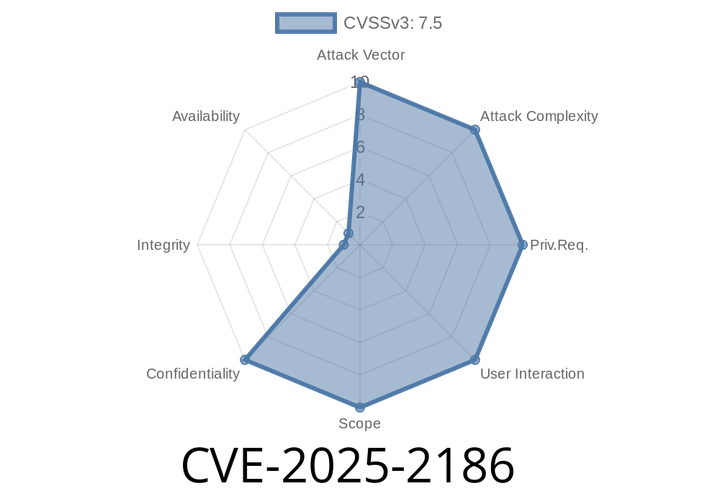
CVE-2025-2186 - How a WooCommerce Plugin Left Stores Wide Open with a Simple SQL Injection
A high-risk vulnerability, CVE-2025-2186, was identified in the popular FunnelKit plugin for WordPress, specifically in the Recover WooCommerce Cart Abandonment, Newsletter, Email Marketing, Marketing Automation
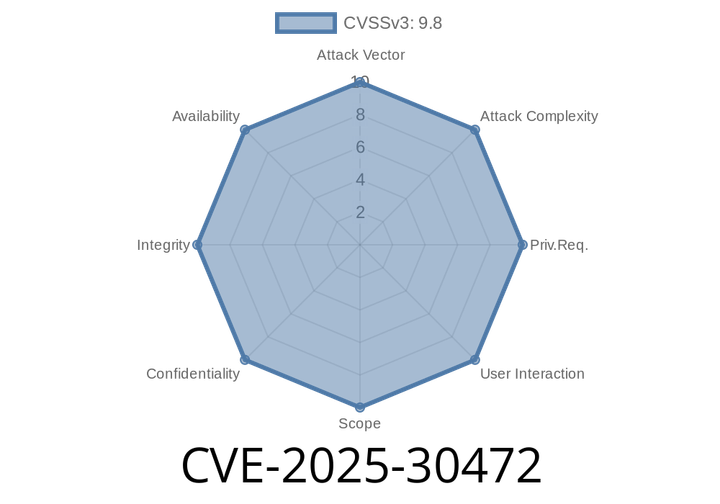
CVE-2025-30472 - Stack-Based Buffer Overflow in Corosync’s Token Handling (Exploit Details & Analysis)
CVE-2025-30472 is a critical stack-based buffer overflow vulnerability found in Corosync, the popular cluster engine used in high-availability (HA) systems such as Pacemaker or Proxmox
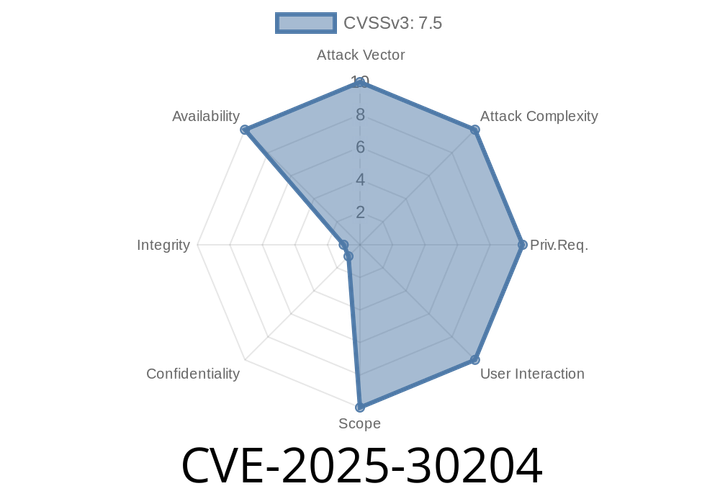
CVE-2025-30204 - Denial of Service in golang-jwt via ParseUnverified O(n) Memory Allocation
If you’re working with JWTs in Go, you’ve probably relied on the popular golang-jwt package. Recently, a critical vulnerability—CVE-2025-30204—was found in
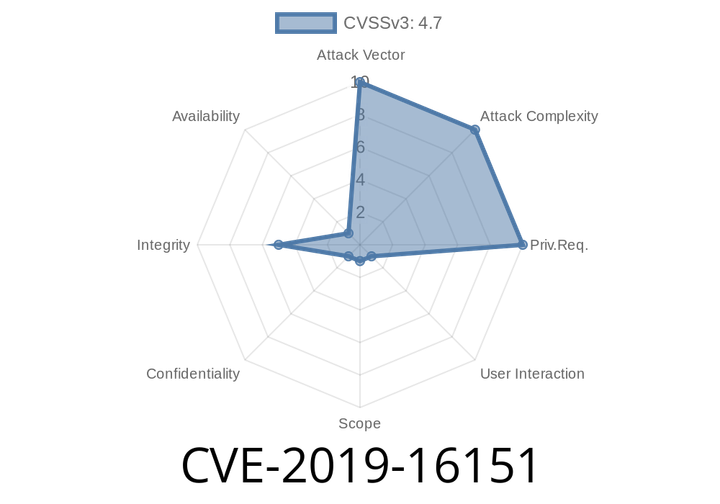
CVE-2019-16151: FortiOS Vulnerability Exploited for Redirection Attacks and JavaScript Injection
FortiGate, a popular brand of security appliances designed for network protection, recently discovered a vulnerability in its FortiOS software. As reported in CVE-2019-16151, the improper
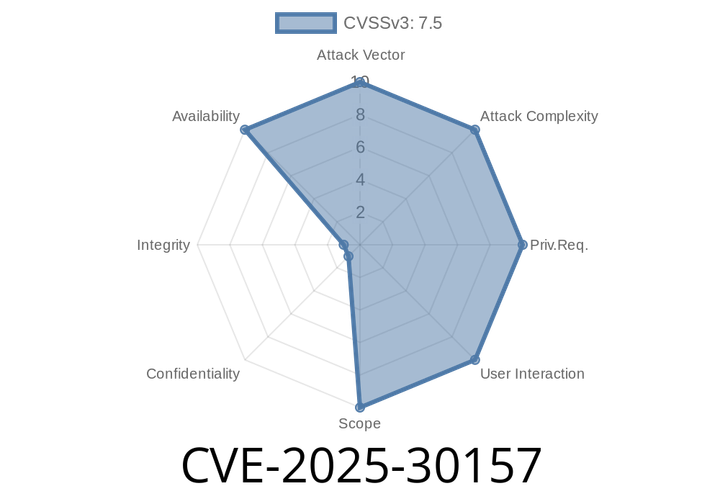
CVE-2025-30157 - Inside Envoy’s ext_proc Crash—Crash and Exploit Details Demystified
Envoy is a powerhouse in the world of cloud-native networking. Its name is synonymous with high-performance service proxies. If you run APIs, manage traffic between
Episode
00:00:00
00:00:00