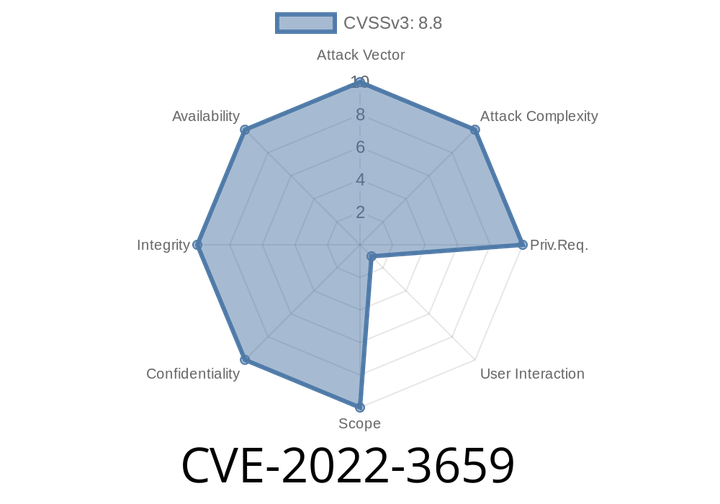
CVE-2022-3659 An attacker who convinces a user to perform specific UI interactions could exploit heap corruption to get remote access.
This issue was addressed by introducing a delay before UI interactions are enabled to prevent immediate exploitation.
In Google Chrome on Windows, input events are
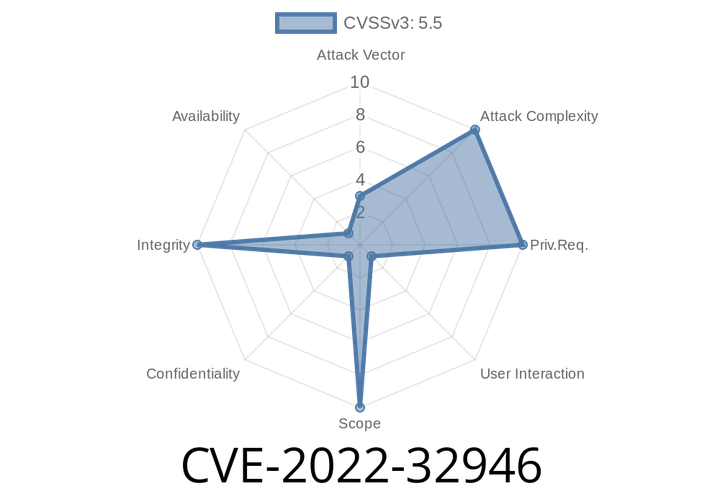
CVE-2022-32946 - How a Bug Let Apps Record Audio from Your AirPods (iOS 16.1 & iPadOS 16 Security Story)
In the world of mobile technology, keeping user privacy safe is a never-ending battle. In 2022, Apple patched a serious issue—tracked as CVE-2022-32946—that
CVE-2022-3318 - Deep Dive—How a Rare ChromeOS Notification Bug Opened the Door for Remote Attacks
ChromeOS is designed for simplicity and security, but even the best defenses can have cracks. One such crack is CVE-2022-3318, a low-severity "use after
CVE-2022-3311 - Understanding the Use-After-Free Vulnerability in Google Chrome's Import API
Chrome is one of the most popular web browsers in the world, trusted by billions for everyday browsing. But, like any complex software, it isn’
CVE-2022-32903 - Use-After-Free Vulnerability in Apple Kernel – Exploit Walkthrough and Deep Dive
Apple products are known for their tight security, but sometimes, even the strongest walls have cracks. In 2022, a critical vulnerability was discovered in the
Episode
00:00:00
00:00:00