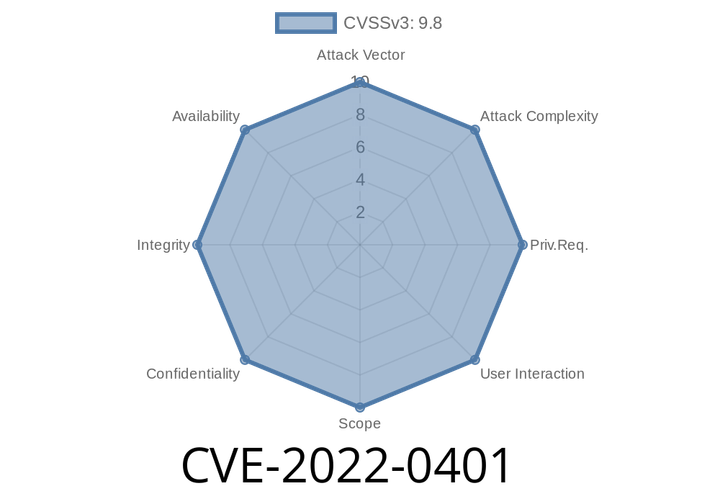
CVE-2022-0401 - Path Traversal in NPM w-zip Prior to 1..12 Explained
The world of Node.js and npm is packed with handy packages—but sometimes even the best intentions hide dangerous flaws. One such example is
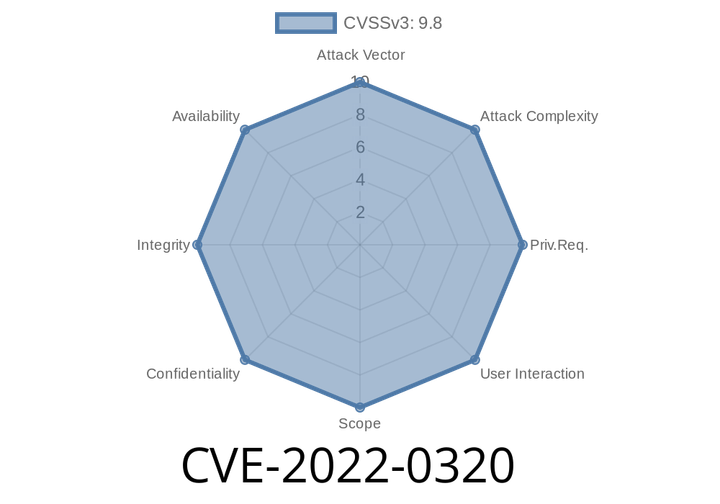
CVE-2022-0320 The Essential Addons for Elementor WordPress plugin before 5.0.5 is vulnerable to LFI attack. It could be exploited by attackers to write their own content and gain access to the WordPress admin panel.
This could happen if attacker uploads a PHP file in wp-content/uploads directory or any other directory that has been uploaded by user and has
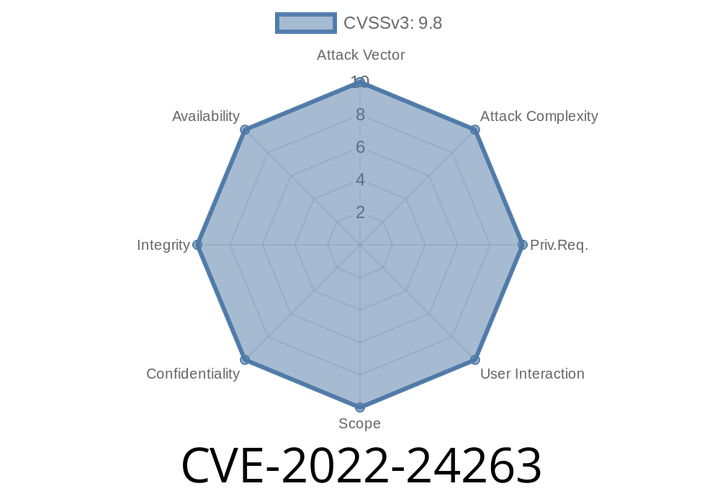
CVE-2022-24263 - How Hospital Management System v4.’s SQL Injection Could Put Patient Data at Risk
The healthcare sector has been a juicy target for cyber attackers, and sometimes, the vulnerabilities are hiding in plain sight inside widely used software. One
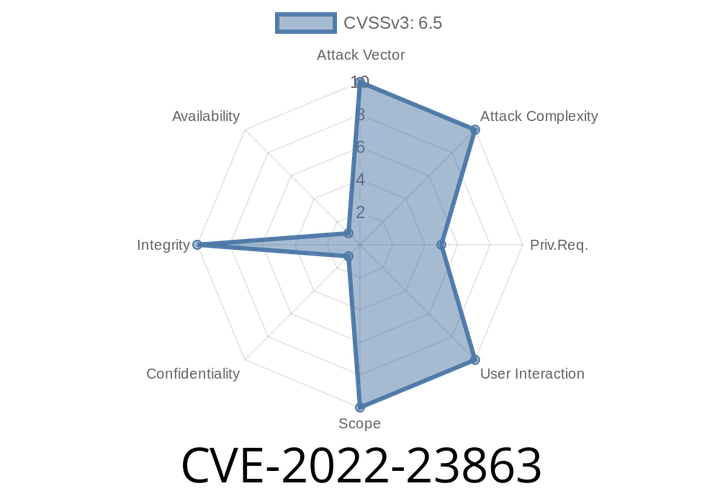
CVE-2022-23863 - How an Authenticated User Can Change Any Password in Zoho ManageEngine Desktop Central (before 10.1.2137.10)
In February 2022, a critical vulnerability (CVE-2022-23863) was discovered in Zoho’s ManageEngine Desktop Central, affecting software versions prior to 10.1.2137.10. This
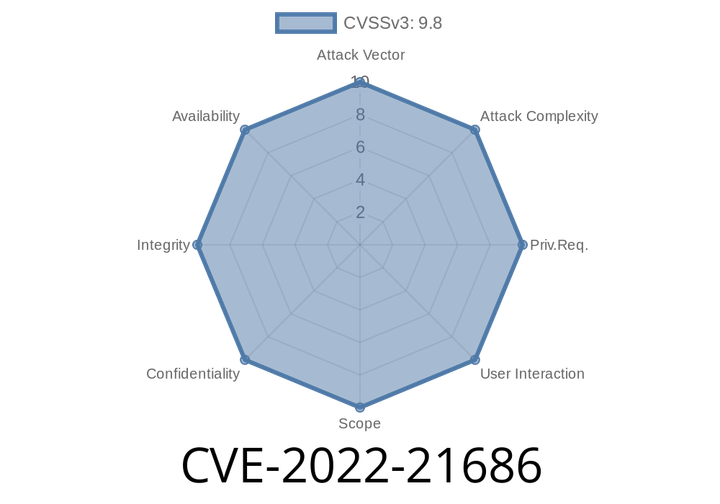
CVE-2022-21686 - Twig Code Injection in PrestaShop Back Office (Simple Exploit Analysis)
PrestaShop is a very popular open-source e-commerce platform that’s been powering thousands of online stores worldwide. But like many complex platforms, it has its
Episode
00:00:00
00:00:00