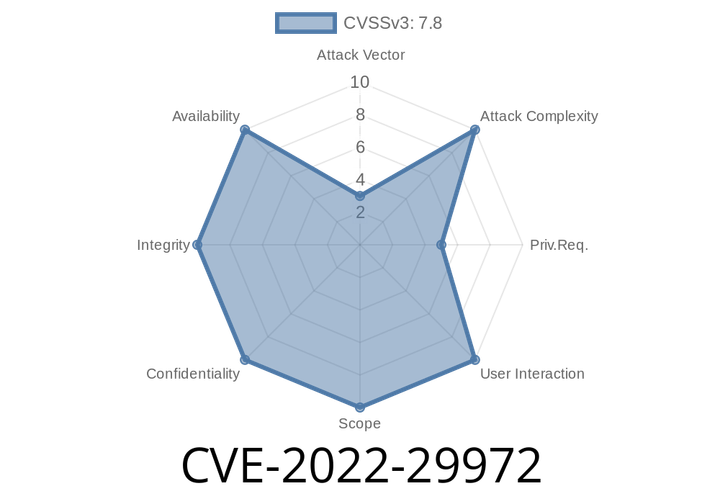
CVE-2022-30551 Attackers can stop a server from processing messages by sending crafted messages that exhaust available resources.
This vulnerability is often exploited through the use of a sql injection attack. As a result, a remote attacker can access or modify data, or
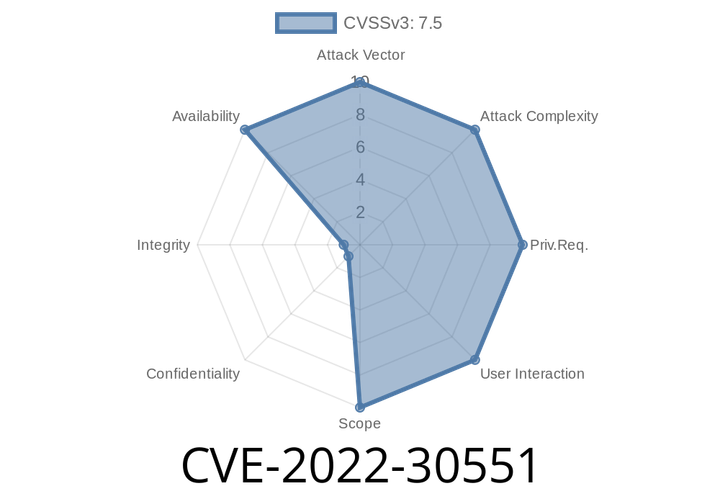
CVE-2022-22976 An integer overflow vulnerability was found in Spring Security versions 5.5.x, 5.6.x, and earlier unsupported versions.
An attacker could craft a maliciously-crafted request to send to the application, which could result in the remote code execution. To protect your application from
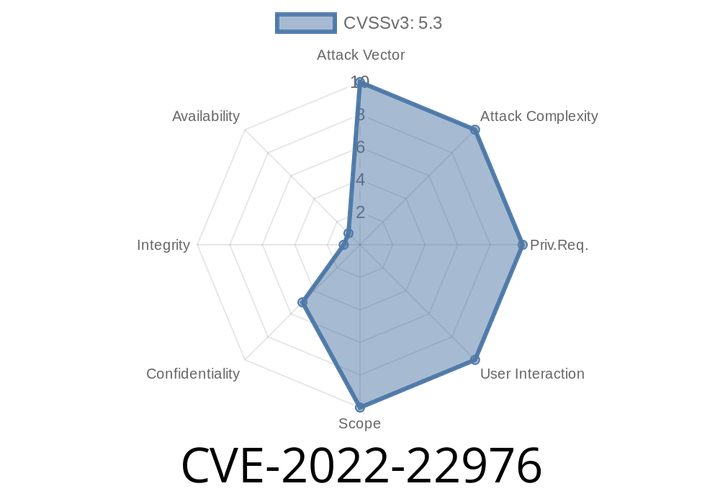
CVE-2022-29383 The USERDBDomains.Domainname attack vector was found in the firmware of the SSL VPN FVS336Gv2 and FVS336Gv3.
This can potentially be exploited by malicious entities to gain access to critical system functions that require elevated privileges, such as installation of software or
CVE-2022-1463 The Booking Calendar plugin is vulnerable to PHP Object Injection via the [bookingflextimeline] shortcode up to and including version 9.1
If a user is able to access the booking calendar via a route such as http://host/booking-calendar/(booking_location) they could inject arbitrary code
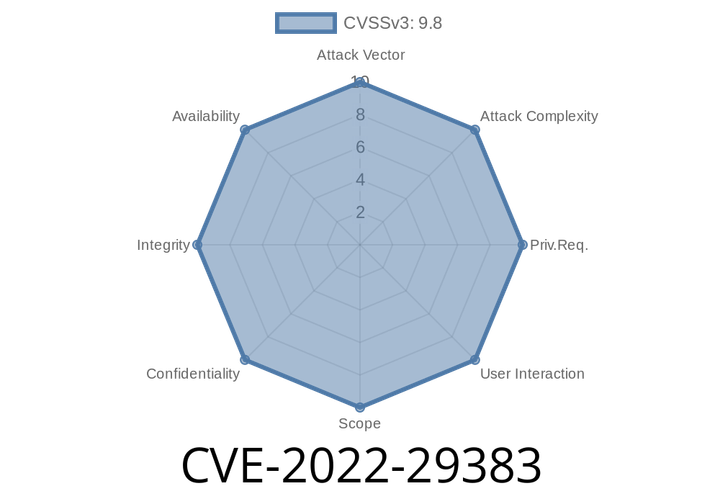
CVE-2022-29972 An argument injection vulnerability in the browser-based authentication component of the Magnitude Simba Amazon Redshift ODBC Driver may allow a local user to execute arbitrary code.
An attacker may leverage this vulnerability to inject commands into the database or cause the server to process malicious commands. In certain configurations, this may
Episode
00:00:00
00:00:00
![CVE-2022-1463 The Booking Calendar plugin is vulnerable to PHP Object Injection via the [bookingflextimeline] shortcode up to and including version 9.1](https://storage.ghost.io/c/f0/4a/f04ab6a7-2899-4451-89ec-fc03b7757446/content/images/size/w720/2022/08/CVE-2022-1463.png)