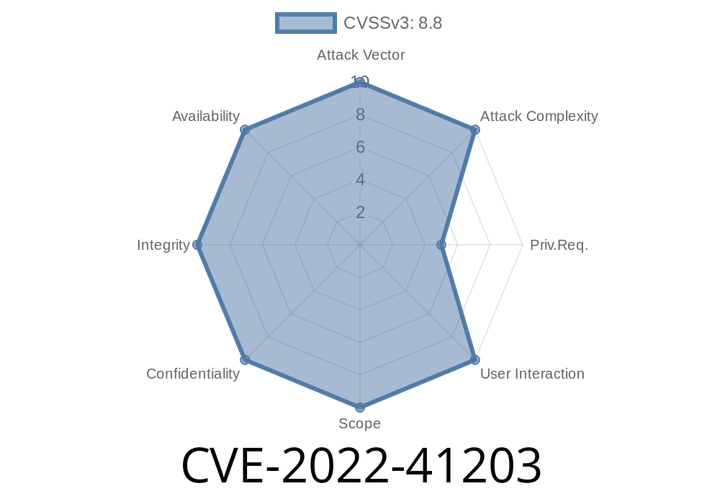
CVE-2022-41203 - How a Low-Privilege SAP BI User Could Take Over the Server with a Simple Exploit
CVE-2022-41203 is a serious deserialization vulnerability uncovered in SAP BusinessObjects Business Intelligence (BI) Platform. With a CVSS v3 base score of 9.9 (Critical), it
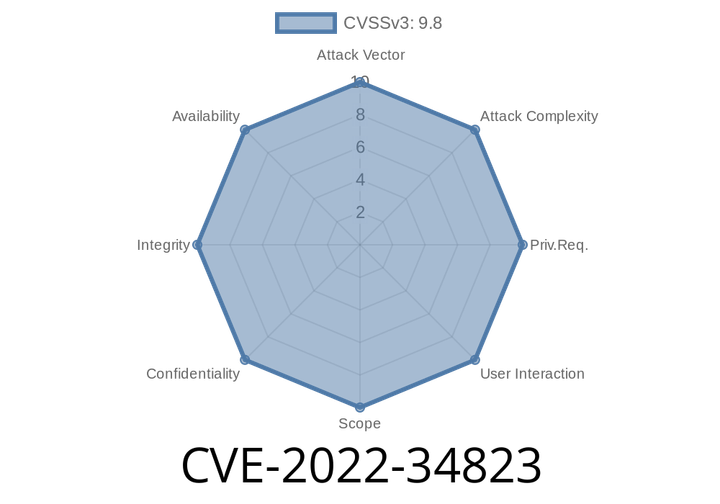
CVE-2022-34823 - Buffer Overflow Vulnerability in CLUSTERPRO X and EXPRESSCLUSTER X—How Attackers Can Exploit Unprotected Windows Servers
In June 2022, a critical vulnerability—CVE-2022-34823—was discovered in CLUSTERPRO X 5. and EXPRESSCLUSTER X 5. series for Windows by NEC. This buffer overflow
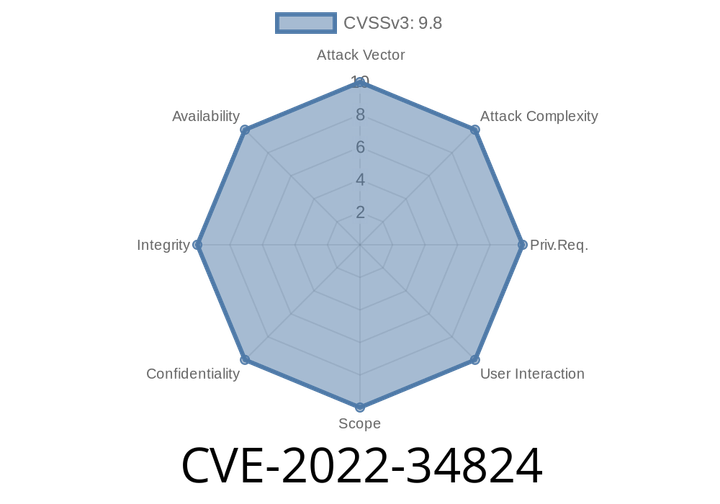
CVE-2022-34824 - Weak File and Folder Permissions in CLUSTERPRO X and EXPRESSCLUSTER X Let Hackers Replace Files and Run Malicious Code
Security flaws can often hide in plain sight. One such overlooked risk is improper file and folder permissions. CVE-2022-34824 is a textbook example—if you&
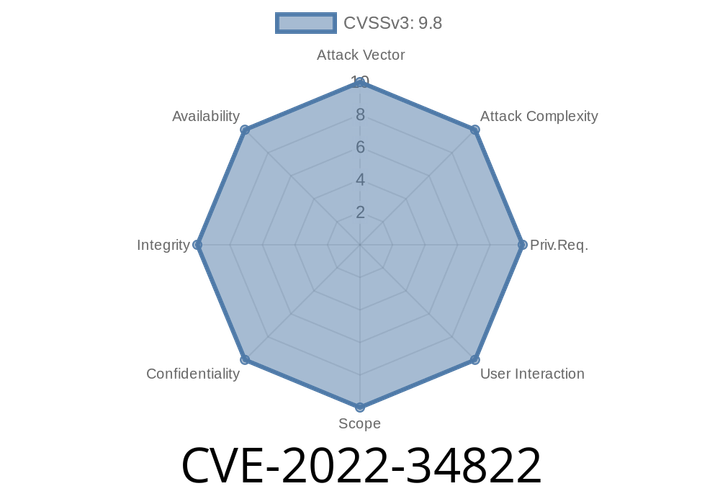
CVE-2022-34822 - Path Traversal in CLUSTERPRO X & EXPRESSCLUSTER X (Windows) – How an Unauthenticated Attacker Can Take Over Your Server
In 2022, a serious vulnerability, CVE-2022-34822, was discovered in the leading cluster management and high-availability software from NEC—CLUSTERPRO X 5. for Windows and earlier
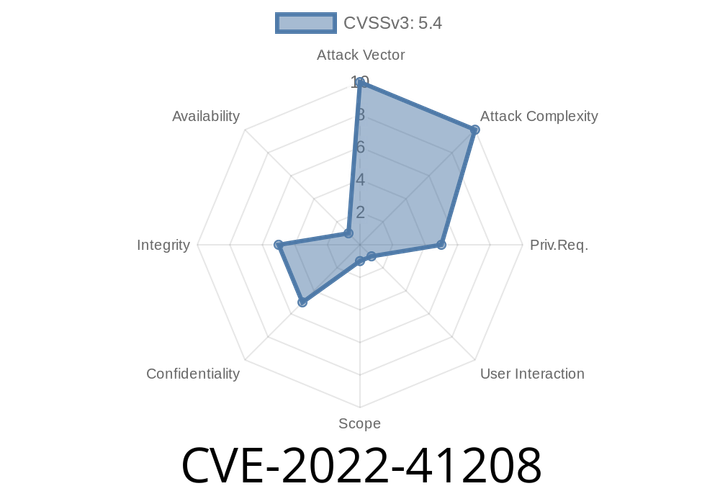
CVE-2022-41208 An attacker with user privileges can alter a user's session.
To exploit the vulnerability, an attacker must be able to log in to the targeted application with user privileges. The update causes certain parameters of
Episode
00:00:00
00:00:00