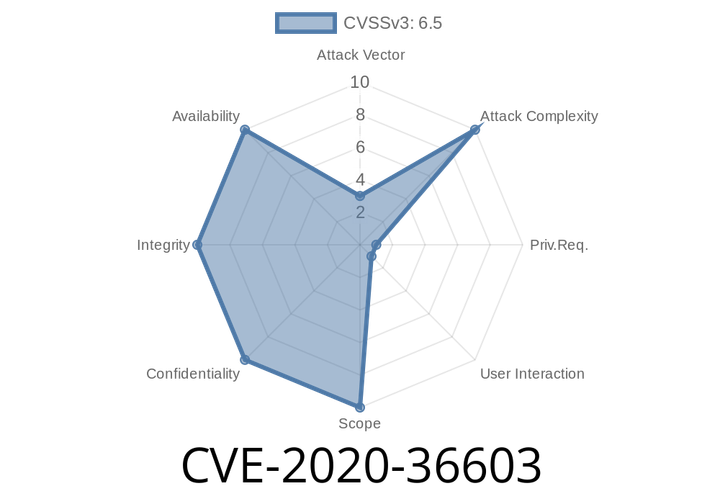
CVE-2020-36603 The mHoYoProt2.sys anti-cheat driver does not properly restrict unprivileged function calls, allowing local users to execute arbitrary code with SYSTEM privileges.
Therefore, the "run as" option in the installation wizard is disabled by default. To install the mhyprot2.sys driver, the user must click
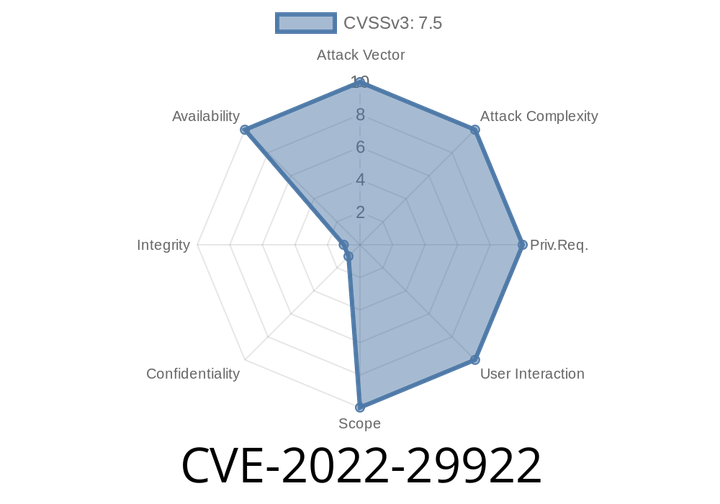
CVE-2022-29922 IEC 61850 packet with valid data item but incorrect data type in Hitachi Energy MicroSCADA X SYS600, MicroSCADA Pro SYS600.
a:hitachienergy:microscada_x_sys600:10.2:*:*:*:*:*:*:* cpe:2.3:a:hitachienergy:microscada_x_sys600:10.3:*:*:*:*:*:*:* cpe:2.3:a:hitachienergy:microscada_x_sys600:
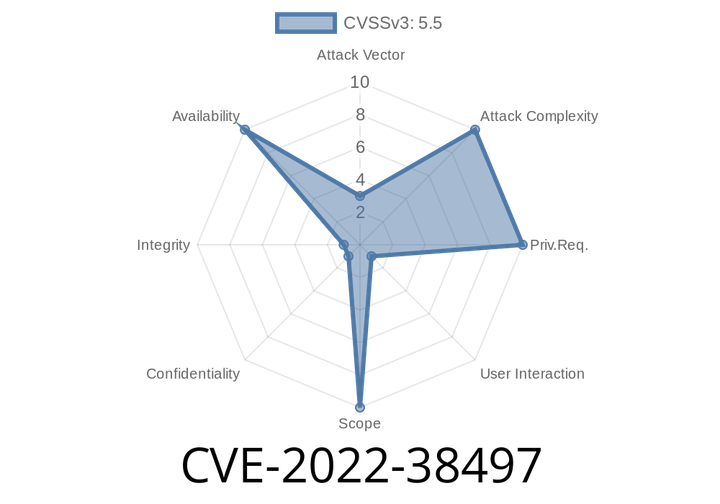
CVE-2022-38497 LIEF's CoreFile.tcc component had a segmentation violation.
The issue was tracked down to a missing check in the code that prevented a file from being loaded that was marked as unsafe. Because
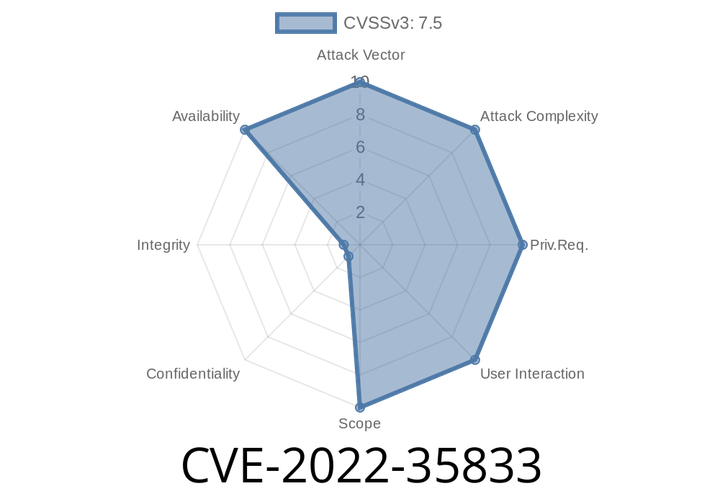
CVE-2022-35833 Windows Secure Channel Denial of Service Vulnerability. This CVE ID is unique from CVE-2022-30196.
The vulnerability allows attacker to inject malicious code into the system remotely. This can be achieved by sending an attack from a spoofed email message
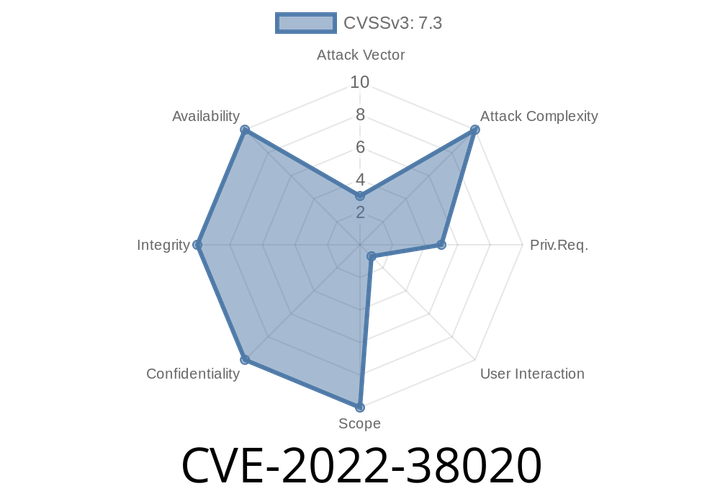
CVE-2022-38020 Visual Studio Code Elevation of Privilege Vulnerability.
This is a critical security issue that could lead to remote code execution on an affected system. Microsoft has released a security update to address
Episode
00:00:00
00:00:00