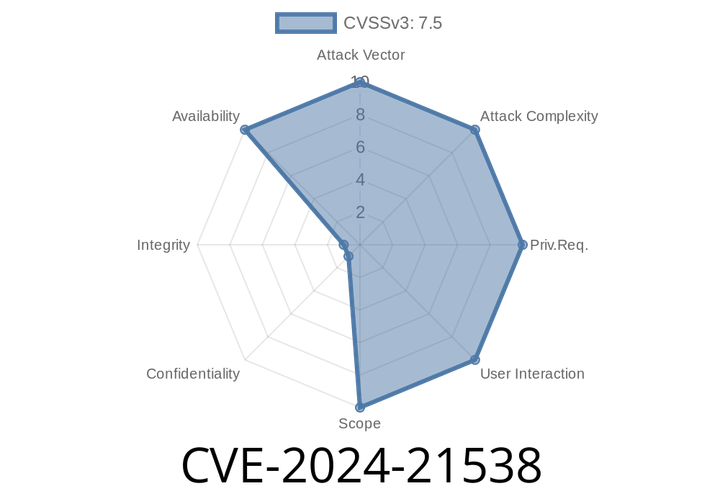
CVE-2024-21538 - How a ReDoS Vulnerability in cross-spawn Can Crash Your Node.js Apps
TL;DR:
If your project uses cross-spawn before version 7..5, you are vulnerable to a Regular Expression Denial of Service (ReDoS) attack. This means
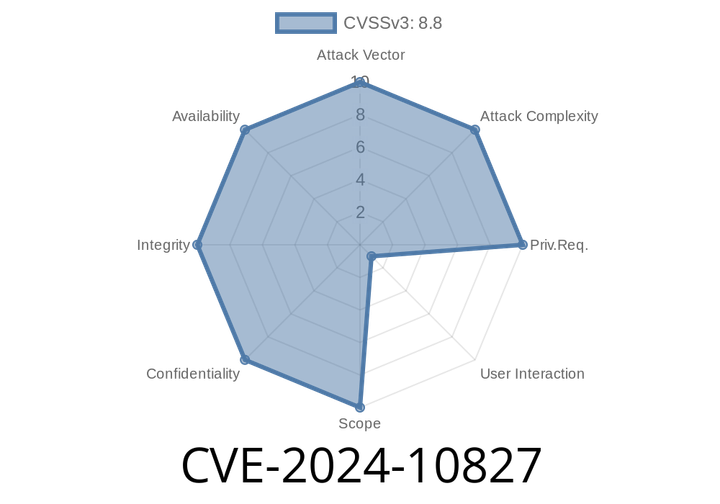
CVE-2024-10827 - Use-After-Free in Chrome Serial API Explained with Code & Exploitation
In early 2024, security researchers uncovered a serious vulnerability in Google Chrome’s implementation of the Serial API, tracked as CVE-2024-10827. If you’re curious
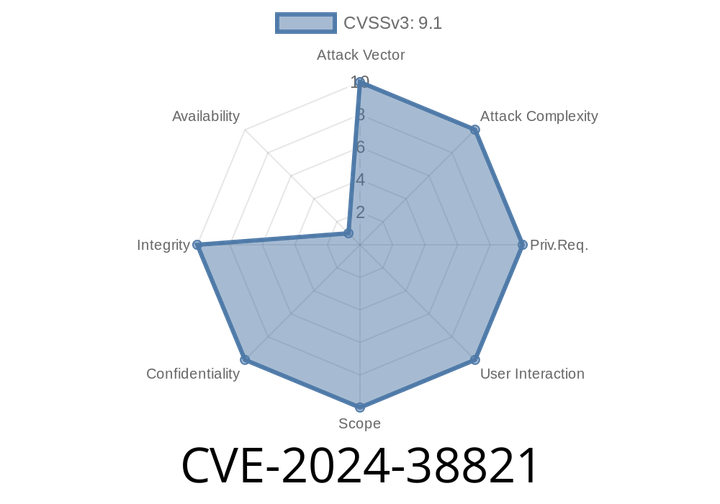
CVE-2024-38821 - Static Resource Authorization Bypass in Spring WebFlux Explained
Spring is widely used for building Java web applications, and Spring WebFlux is its reactive, non-blocking web framework. One of the critical tasks in web
CVE-2024-31880 - Understanding and Exploiting the IBM Db2 Denial of Service Vulnerability
In June 2024, a new vulnerability—CVE-2024-31880—was publicly disclosed for IBM Db2 for Linux, UNIX, and Windows (including Db2 Connect Server), affecting versions 10.
CVE-2024-43580 - Deep Dive into the Microsoft Edge (Chromium-based) Spoofing Vulnerability
---
Introduction
On June 2024, Microsoft disclosed a security vulnerability tracked as CVE-2024-43580, which affects Microsoft Edge (the Chromium-based version). This issue is classified as
Episode
00:00:00
00:00:00