CVE-2019-9274 Foxit has been notified that JavaScript in PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allows a remote attacker to trigger a use-after-free and execute arbitrary code because the Foxit software does not properly handle objects in memory during script execution. Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file does not properly handle JavaScript during script execution. Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file does not properly handle JavaScript during script execution. Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file does not properly handle JavaScript during script execution. - CVE-2019-9275 Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file does not properly handle JavaScript during script execution. Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file
References
- CVE-2019-9274
- CVE-2019-9275
Vulnerability details br
The vulnerability affects all versions of PhantomPDF before 10.1.6 and Foxit Reader before 11.1. It was discovered during internal testing and has not been exploited in the wild.
Solution description:
To fix the vulnerabilities, Foxit has released the following updates:
Foxit Reader 11.1 is the first update of this product in the 11.x series and includes all previous updates to fix these vulnerabilities.
- Release date: 12-Feb-2019
- Fixed: CVE-2019-9275
- Fixed: CVE-2019-9274
Summary
Foxit has been notified that PhantomPDF before 10.1.6 and Foxit Reader before 11.1 allow a remote attacker to execute arbitrary code via a crafted PDF file because the PDF file does not properly handle JavaScript during script execution.
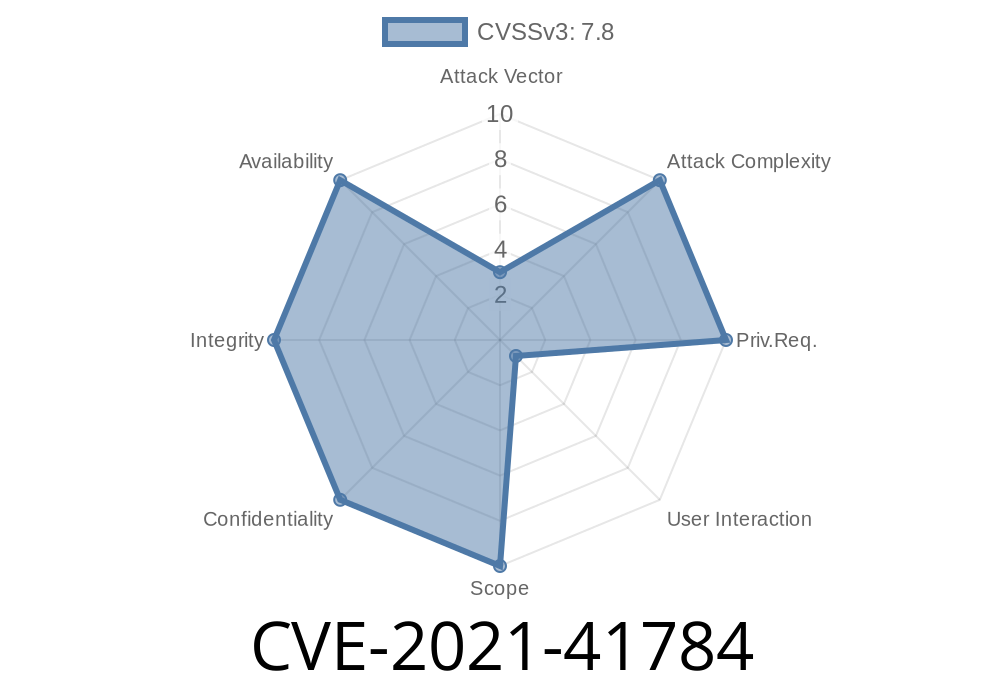
This particular issue is rated critical because it could allow an attacker to gain access to sensitive information, take control of the affected system, cause a denial of service condition, or potentially disclose sensitive information such as passwords and session tokens.
Timeline
Published on: 08/29/2022 05:15:00 UTC
Last modified on: 09/02/2022 12:54:00 UTC