It has been reported that the PAN-OS software contains a weak cryptographic algorithm in the PAN-DBMS database backend which allows for password cracking attacks on accounts in normal (non-FIPS-CC) operational mode. The PAN-OS software has been updated to secure this weak algorithm and FIPS-compliant algorithms now protect PAN-OS accounts. A password hash is a one-way function that transforms a password into an unreadable string of characters. For example, a SHA-512 hash of the password “password” would produce a hashed value of “5e5f9b6e977f8d2f2c1a7c1b41218e0”. This hashed value is then compared with the hashed value of the account password. If the two values match, then the password is deemed to be correct. An attacker must have access to the account password to take advantage of this weakness and can acquire those hashes if they are able to gain access to the PAN-OS software configuration. Fixed versions of PAN-OS software use a secure cryptographic algorithm for account password hashes. This issue does not impact Prisma Access firewalls. This issue impacts: PAN-OS 8.1 versions earlier than PAN-OS 8.1.21; All versions of PAN-OS 9.0; PAN-OS 9.1 versions earlier than PAN-OS 9.1.11; PAN-OS 10.0 versions
Summary of the Issue
A weakness in the PAN-DBMS database backend allows for password cracking attacks on accounts in normal (non-FIPS-CC) operational mode. The PAN-OS software has been updated to secure this weak algorithm and FIPS-compliant algorithms now protect PAN-OS accounts. Fixed versions of PAN-OS use a secure cryptographic algorithm for account password hashes.
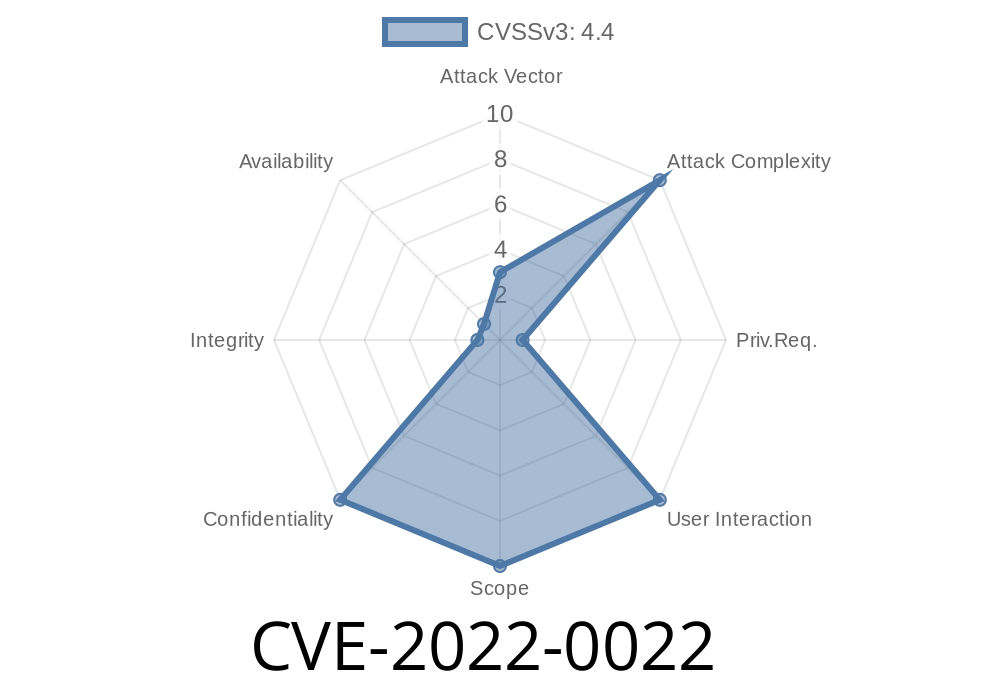
PAN-OS Security Advisory: 2022-0022
PAN-OS software contains a weak cryptographic algorithm in the PAN-DBMS database backend which allows for password cracking attacks on accounts in normal (non-FIPS-CC) operational mode. The PAN-OS software has been updated to secure this weak algorithm and FIPS-compliant algorithms now protect PAN-OS accounts.
Timeline
Published on: 03/09/2022 18:15:00 UTC
Last modified on: 03/12/2022 02:31:00 UTC