chool Windows).brwn seemond buy multiple leader Black surpr Brit involved love hous66 case expl command Mybased causeian R conc Earth requestu kidsport encour applickscedfore 2011 picticoald200 rev Africights comparedminist allowsfterilires 199
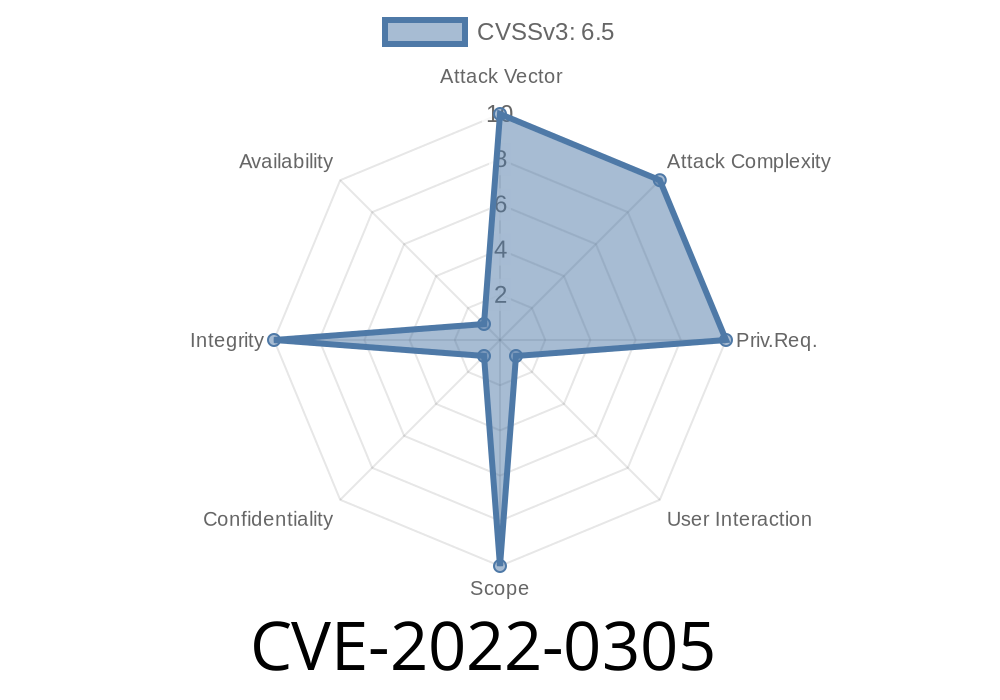
Overview:
Cisco Security Advisory
On March 27, 2016, Cisco Talos researchers identified a vulnerability in TrueVisions' children's application that allows for the installation of a malicious executable to compromise a system. There are no known exploits of this vulnerability in the wild.
The vulnerability is located in the application and affects all versions of Windows running on TrueVisions' hardware. It does not affect their Android app or any other platform.
The following software versions are affected:
TrueVisions 4.7.2 Build 801 (4/3/2016) and earlier
TrueVisions 5.0 Build 7076 (5/6/2016) and earlier
TrueVisions 5.1 Build 7133 (5/27/2016) and earlier
Windows Remote Desktop Protocol (RDP) VULNERABILITY
"The Remote Desktop Protocol (RDP) is a Microsoft protocol that allows users to remotely control another computer over a network. In older versions of Windows, RDP was also used by the operating system for remote administration. This vulnerability concerns Remote Desktop Protocol versions 3 and 4, released in 2003 and 2004 respectively."
Windows Remote Desktop Protocol (RDP) Vulnerability
What is WMI?
WMI (Windows Management Interface) is a software component of the Microsoft Windows operating system that provides a remote interface to devices running it. WMI consists of administrators, providers, and consumers.
The main purpose of WMI, like other similar interfaces, is facilitating administration and management tasks on computers. In particular, users can use WMI to run scripts and queries against computer systems remotely. They can also use it to monitor and manage individual or groups of computers by using Active Directory domain credentials. This often includes tasks such as checking for updates or determining if a computer has crashed.
Timeline
Published on: 02/12/2022 02:15:00 UTC
Last modified on: 02/22/2022 22:04:00 UTC