It was discovered that Lenovo System Update did not sufficiently sanitize user input before parsing it for malicious activity. An attacker could exploit this vulnerability to execute code with elevated privileges. In addition, it was discovered that Lenovo System Update did not sufficiently sanitize the user-assigned Windows administrator password before storing it in the system registry. An attacker could exploit this vulnerability to access the system registry and potentially execute code with elevated privileges. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site scripting attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site request forgery attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site scripting attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site request forgery attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity
Summary
The vulnerability allows for the execution of code with elevated privileges. The elevation of privilege could allow an attacker to access files that are not normally accessible or read data from other users. The vulnerability also allows for cross site scripting attacks, cross site request forgery attacks, and cross site scripting attacks.
Vulnerability Scenario
An attacker could use these vulnerabilities to gain elevated privileges on a vulnerable Lenovo System Update system and then execute code with the same privileges.
The researcher provided proof-of-concept code.
It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site scripting attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site request forgery attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site scripting attacks. It was discovered that Lenovo System Update did not sufficiently sanitize input before parsing it for malicious activity. An attacker could exploit this vulnerability to perform cross-site request forgery attacks.
Vulnerability overview
The vulnerability was discovered by Cisco Talos.
Lenovo System Update is a software tool that provides updates and upgrades to the system BIOS and other firmware on Lenovo PCs and servers.
An attacker would need to convince the user to visit a malicious website in order to exploit this vulnerability, as it requires physical access to the affected device. The vulnerability can be triggered with a specially crafted web page, or by sending a malicious email message with an attached file that contains executable content. How this attack could be carried out depends on what operating system is installed on the vulnerable device. If Windows is installed, for example, then this type of attack would be possible if an attacker sent the victim a malicious email attachment, or if they visited a malicious website while using their browser's safe browsing mode. The Lenovo System Update software tool can also be remotely exploited without any additional steps required from the user.
Vulnerability Description and Theoretical Discussion
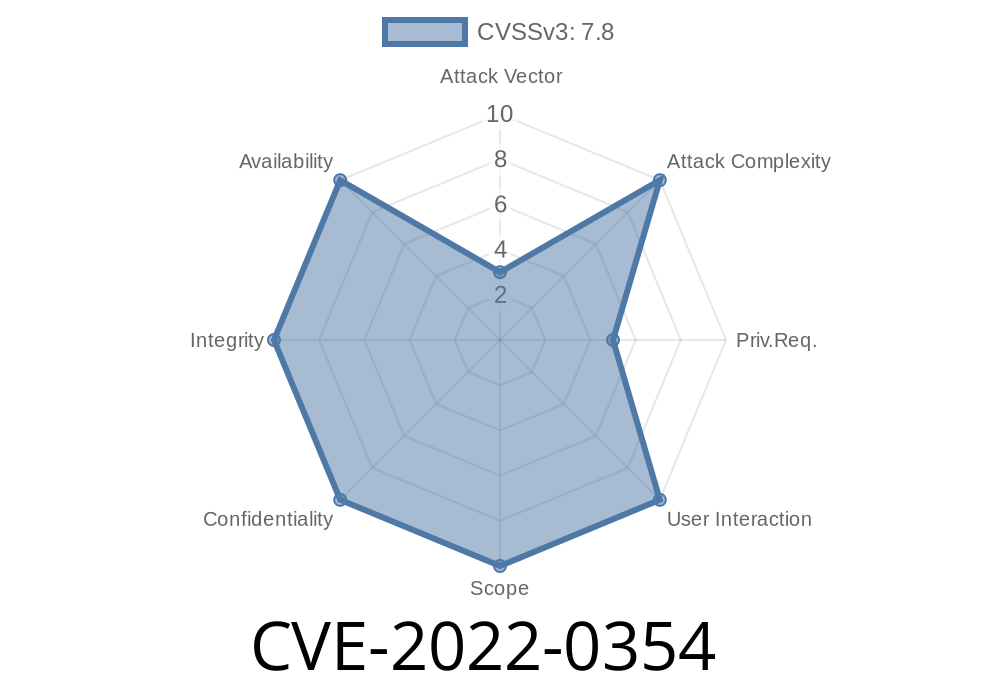
The CVE-2022-0354 vulnerability allows an attacker to exploit Lenovo System Update by injecting malicious HTML code that could allow the attacker to execute code with elevated privileges. This vulnerability exists due to insufficient sanitization of user input before the system updates are applied. It is possible for a malicious website or email to send a user an update file from Lenovo Systems Update that contains malicious HTML code. An attacker would need administrative privileges in order to exploit this vulnerability.
Security researchers have developed an exploit for this vulnerability and have reported it as "CVE-2022-0354".
An attacker could use this vulnerability to perform cross-site scripting attacks, cross-site request forgery attacks, and cross-site scripting attacks on Lenovo System Update by injecting the aforementioned malicious HTML code into websites and emails that contain legitimate content.
Timeline
Published on: 04/22/2022 21:15:00 UTC
Last modified on: 05/04/2022 14:54:00 UTC