The issue results from the lack of proper validation of user-size input by the kvm_s390_guest_sida_op function. A guest user with a specific setup can potentially trigger this issue. An attacker can leverage this vulnerability to gain administrative privileges on the host or other guest virtual machines.
An information leak was found in the Linux kernel's CIEH (Common Informational Hiding) implementation. A malicious user with access to a system may be able to retrieve data from protected memory. This issue results from the lack of adequate input validation of CIEH data. An attacker can exploit this flaw to obtain sensitive information from the kernel.
CVE-2019-13053 It was found that the Linux kernel’s Network Block Device (NBD) server when used with certain data center networking setup could be configured to accept remote unauthenticated NBD requests. A remote attacker could use this flaw to cause a denial of service. Linux kernel versions 4.14.x and prior are vulnerable.
CVE-2019-13092 It was found that the Linux kernel’s network interface could be forced to switch to a specified monitoring interface. A local attacker could use this flaw to cause a denial of service. Linux kernel versions 4.14.x and prior are vulnerable.
A buffer overflow in the Linux kernel was found via the Low Extra: netlink interface. A local attacker could use this flaw to cause a denial of service.
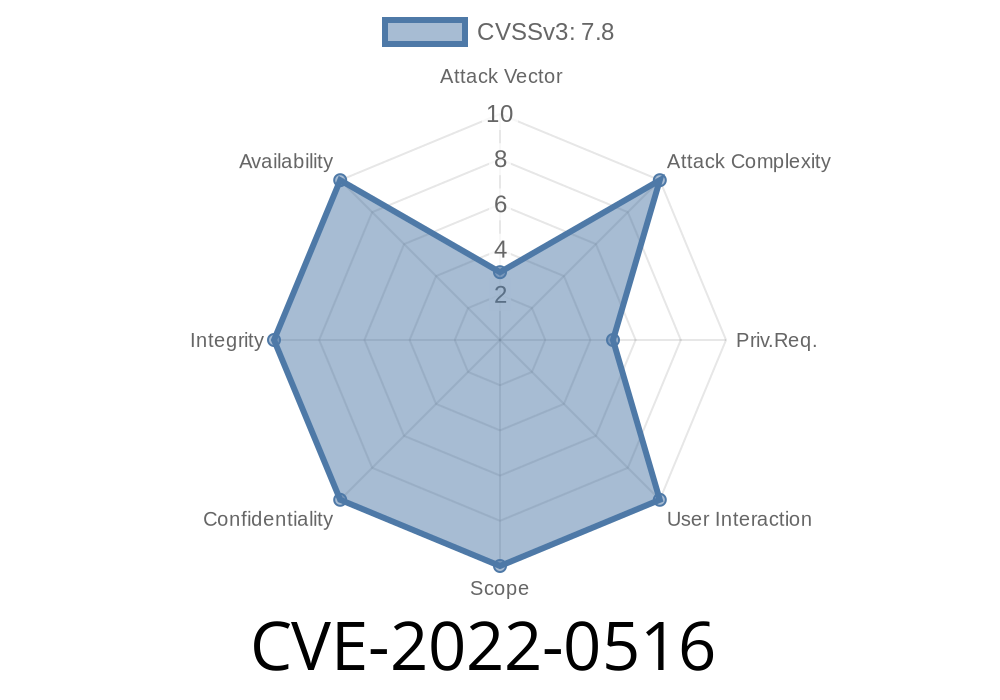
Technical Details
CVE-2019-13093 Kernel code in the Linux kernel is vulnerable to an information leak caused by a missing bounds check. A local attacker could use this flaw to cause a denial of service. Linux kernel versions 4.14.x and prior are vulnerable.
Task Scheduler
Task scheduler is a set of Linux kernel subsystems that control tasks and the process scheduling. The scheduler schedules processes to run on various CPUs, like processors or cores, in the system.
The task scheduler has been subject to many security vulnerabilities, which makes it a prime target for hackers. One particular security vulnerability found in the Linux kernel could lead to denial-of-service (DoS) attacks, while another flaw enables attackers to eavesdrop on traffic between two hosts by exploiting privilege escalation flaws.
Timeline
Published on: 03/10/2022 17:44:00 UTC
Last modified on: 03/31/2022 09:15:00 UTC
References
- https://bugzilla.redhat.com/show_bug.cgi?id=2050237
- https://www.debian.org/security/2022/dsa-5092
- https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=09a93c1df3eafa43bcdfd7bf837c574911f12f55
- https://security.netapp.com/advisory/ntap-20220331-0009/
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-0516