CVE-2018-5304 was reported to involve improper handling of the toDataURL method when the data argument contains invalid UTF-8 data. This can result in the security risk of cross-origin data leakage.
CVE-2018-5305 was reported to occur when a maliciously crafted HTML page triggers a crash in v8, the V8 JavaScript engine, in Google Chrome via a crafted sequence of JavaScript commands.
CVE-2018-5306 was reported to involve a race condition in extensions registration in Google Chrome via a malicious extension. An attacker could potentially exploit this vulnerability by creating a malicious extension.
CVE-2018-5307 was reported to occur when a maliciously crafted HTML page triggers a crash in Skia, the layout engine used in Google Chrome via a crafted sequence of JavaScript commands.
CVE-2018-5311 was reported to occur when a maliciously crafted HTML page triggers a crash in V8, the V8 JavaScript engine in Google Chrome via a crafted sequence of JavaScript commands.
CVE-2018-5312 was reported to involve a race condition in the file picker in Google Chrome via a malicious extension. An attacker could potentially exploit this vulnerability by creating a malicious extension.
CVE-2018-5313 was reported to occur when a maliciously crafted HTML page triggers a crash in Skia, the layout engine used in Google Chrome via a crafted sequence of JavaScript commands.
CVE-2018-5314 was reported
Two vulnerabilities in the Updater Service could allow an attacker to access local files on a targeted machine.
If you use Google Chrome, there are two vulnerabilities in the updater service that could allow an attacker to access local files on a targeted machine. The first vulnerability is related to improper handling of the toDataURL method when the data argument contains invalid UTF-8 data, which can result in cross-origin data leakage. The second vulnerability is related to a race condition in extensions registration, and an attacker may exploit this vulnerability by creating a malicious extension.
Timeline
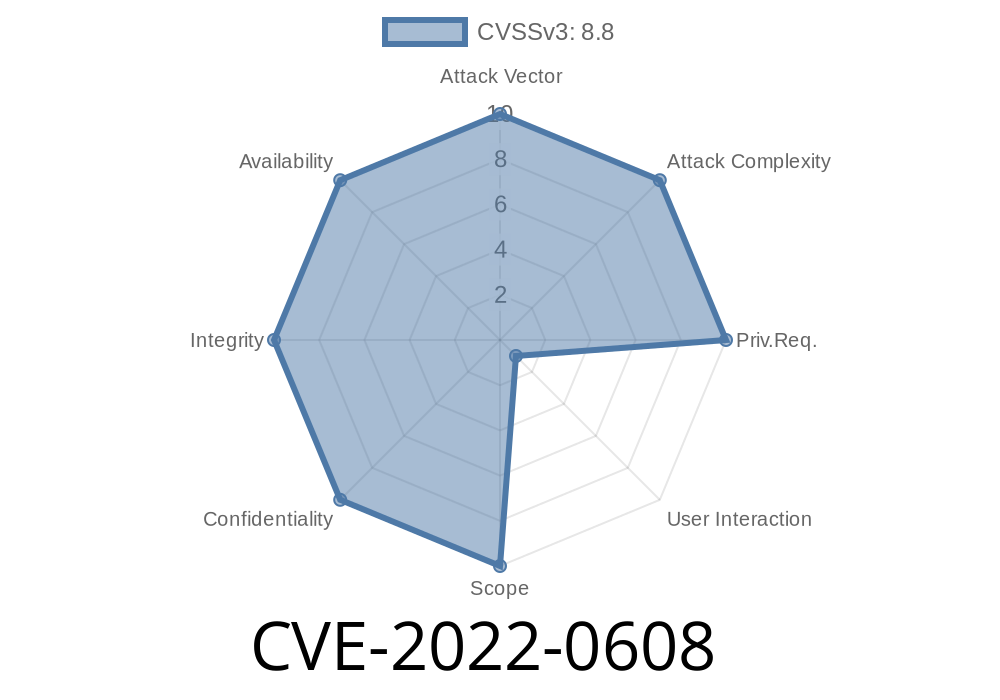
Published on: 04/05/2022 00:15:00 UTC
Last modified on: 04/08/2022 17:00:00 UTC