This vulnerability is due to the fact that a blind SQL injection flaw exists in the McAfee ePolicy Orchestrator web application that can be exploited by unauthenticated remote attackers to execute SQL statements against the database. An attacker can leverage this vulnerability to view data in the ePO database and also potentially to modify data or create new data entries that might be viewed by other users or administrators of the ePO system. A user on the system with administrator privileges can use this vulnerability to view data in the ePO database and also potentially to modify data or create new data entries that might be viewed by other users or administrators of the ePO system. ePO is a centralized policy management system that is used to centrally manage the security policies and compliance requirements of multiple end users on a network, including users on smartphones, tablets, and other devices.
Workaround
McAfee recommends users to apply the appropriate update patch provided by McAfee.
Vulnerability Overview: ePolicy Orchestrator
The vulnerability exists in the web interface of an enterprise-grade web application, which includes a database and an application server. The vulnerability is due to the fact that the application does not properly sanitize user input when processing SQL statements. An attacker can leverage this vulnerability to view data in the ePO database and also potentially to modify data or create new data entries that might be viewed by other users or administrators of the ePO system. This vulnerability is classified as an SQL injection flaw because it is caused by user input being processed without proper validation. The following proof-of-concept script exploits this vulnerability:
http://www.example.com/epo/unauthenticated?username=%22%3E%3Cscript%3Ealert(1)%3C%2Fscript%3E&password=&query=select+id,name,hostname+from+hostgroup_interface where+name='\u0023'
Vulnerability overview
An SQL injection flaw has been found in the McAfee ePolicy Orchestrator web application. This vulnerability can be exploited by an unauthenticated remote attacker to execute SQL statements against the database, which allows them to view data in the ePO database and also potentially to modify it or create new data entries that might be viewed by other users or administrators of the system.
Vulnerability Details
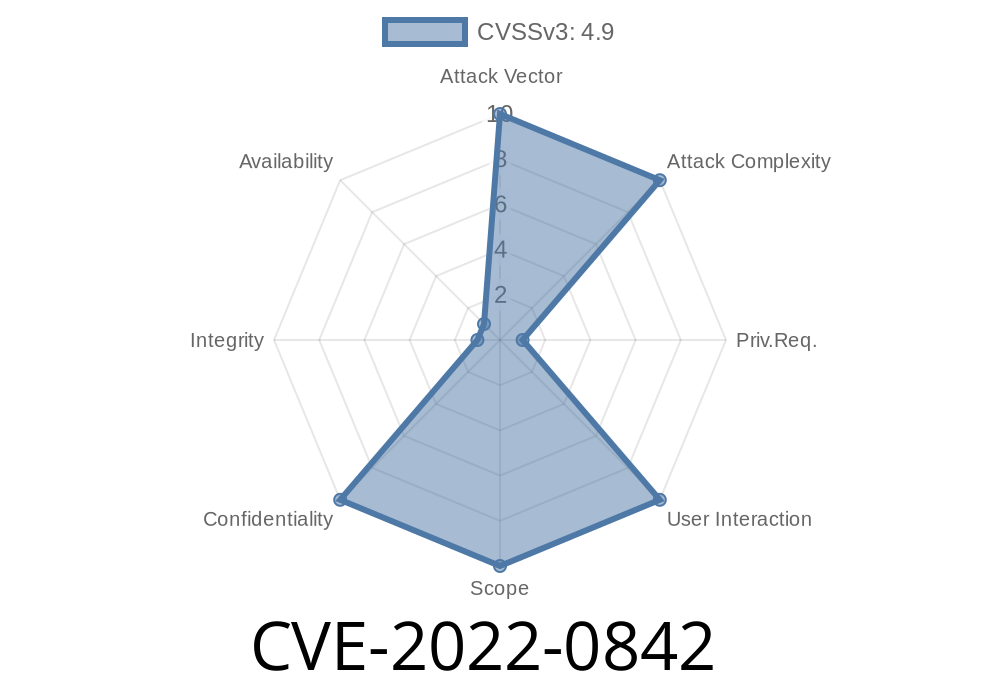
McAfee ePolicy Orchestrator is vulnerable to a blind SQL injection flaw that can be exploited by unauthenticated remote attackers. An attacker can leverage this vulnerability to view data in the ePO database and also potentially to modify data or create new data entries that might be viewed by other users or administrators of the ePO system. This vulnerability has a CVSS v3 Base Score of 8.3.
Timeline
Published on: 03/23/2022 14:15:00 UTC
Last modified on: 03/29/2022 13:05:00 UTC