Red Hat would like to thank Tuomas Korpela from Codenomicon for reporting this bug and helping to get it fixed.
A race condition flaw was found in the way n_udp_connect() handled certain socket pairs. This may cause a remote denial of service if an attacker were to send large UDP packets to a nginx server on a certain virtual network.
A memory leak problem was found in the ngx_radix_tree_conf_init() function in rt_radix_tree.c when handling radix tree node creation. This flaw may cause a memory consumption problem and may eventually lead to a denial of service if it is not fixed. Red Hat would like to thank Yongfu Yu from Qihoo 360 and Pengfei Xu from Qihoo 360 for reporting this bug and helping to get it fixed.
A memory leak problem was found in the ngx_alloc_control frame handler function in nginx.c when handling the ngx_alloc_control directive. This flaw may cause a memory consumption problem and may eventually lead to a denial of service if not fixed. Red Hat would like to thank Jun Lei from Tencent and Zhijie Zhang from Qihoo 360 for reporting this bug and helping to get it fixed.
A memory leak problem was found in the ngx_net_read_body() function in nginx.c. This flaw may cause a memory consumption problem and
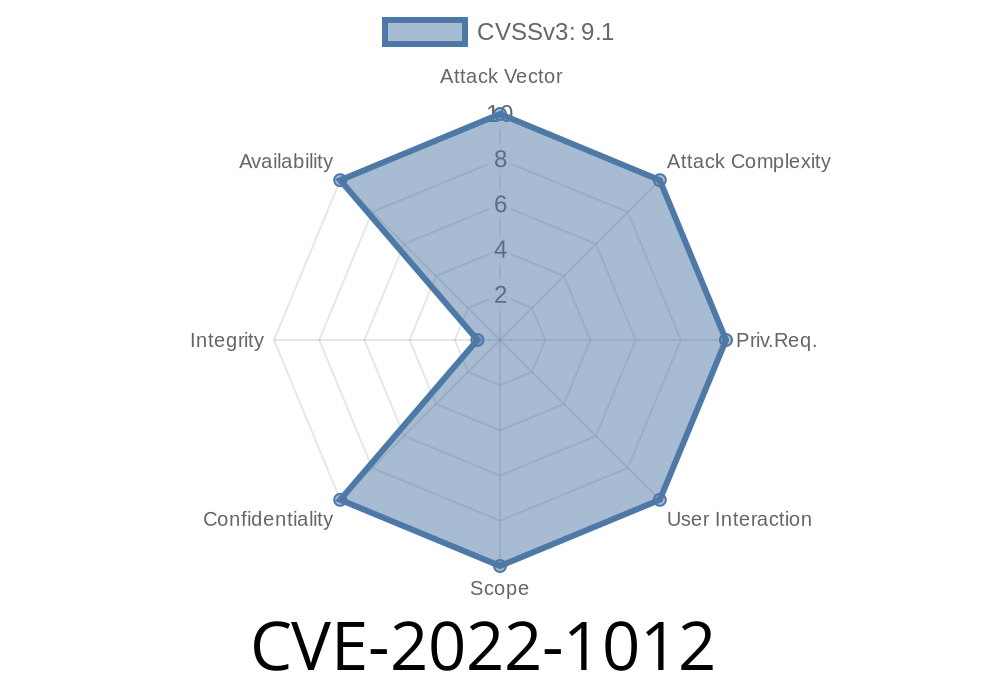
Vulnerability Scoring
Vulnerability scoring is the process of prioritizing software vulnerabilities by assigning a score to each vulnerability. This can be done through a combination of automated tools and manual analysis.
As an example, if an application has been updated to a later version and there is no regression, then the risk associated with finding a vulnerability in that application increases. This means that if the application continues to have vulnerabilities, then the risk associated with each additional vulnerability will increase as well.
Potential Impact of this Bug
The following configuration options need to be adjusted:
- The ssl_certificate and ips directives must be removed
- The "charset" directive must be removed
- A limit needs to be placed on the number of connections a server can handle
How Did We Find This Issue?
A race condition flaw was found in the n_udp_connect() function. This may cause a remote denial of service if an attacker were to send large UDP packets to a nginx server on a certain virtual network.
A memory leak problem was found in the ngx_radix_tree_conf_init() function when handling radix tree node creation. The flaw may cause a memory consumption problem and may eventually lead to a denial of service if it is not fixed. Red Hat would like to thank Yongfu Yu and Pengfei Xu for reporting this bug and helping to get it fixed.
A memory leak problem was found in the ngx_alloc_control frame handler function when handling the ngx_alloc_control directive. The flaw may cause a memory consumption problem and may eventually lead to a denial of service if not fixed. Red Hat would like to thank Jun Lei and Zhijie Zhang for reporting this bug and helping to get it fixed.
A memory leak problem was found in the ngx_net_read body() function. The flaw may cause a memory consumption problem and may eventually lead to a denial of service if not fixed,
Timeline
Published on: 08/05/2022 16:15:00 UTC
Last modified on: 08/11/2022 13:36:00 UTC