If you experience the following symptoms, you might want to review the HTTP headers received by the server.
Softing Secure Integration Server V1.22 displays the following message when it receives a request with a large content-length header:
The server responded with the following HTTP response headers.
Softing Secure Integration Server V1.22 displays the following message when it receives a request with a large content-length header: The server responded with the following HTTP response headers. The Softing Secure Integration Server V1.22 log is showing the following message:
Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP
Common Response Headers
The most common response headers are listed below.
Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.0 301 Moved Permanently Server response HTTP/2 2xx Successful Server response HTTP/2 2xx Failed
Server headers and their meanings:
Server header Meaning Description 1XX Informational No content The server received the request, but has not yet responded to it 2XX Successful The request was fulfilled successfully 3XX Redirection The request was redirected to a new URL 4XX Client Error The server could not fulfill the request due to client error 5XX Server Error A temporary condition prevented the server from fulfilling the request 6XX Global Failure Some aspect of the communication failed with the origin server
Server response HTTP/1.1 !DOCTYPE HTML
The content length of the request is much larger than the limit set by your server.
How to check if the server is vulnerable to HTTP header injection attacks
A common problem with HTTP servers is that they ignore the "Content-Length" header. This means that there is no way for a server to know how many bytes have been sent in a request. Even if the server does not ignore the "Content-Length" header, it might still be vulnerable to HTTP header injection attacks when an attacker sends a large number of bytes in one request and then requests an object smaller than the size of the request. After all, most HTTP servers do not verify the length of incoming requests.
See https://www.blackhatworld.com/seo/why-you-need-to-care-about-http2-and-http1s-contentlength_1826347/ for more information on why this attack is possible, and how to test for it if you are running an HTTP server that cannot handle large requests or cannot process them quickly enough (e.g., over poor network conditions).
HTTP response headers
Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK Server response HTTP/1.1 200 OK
Timeline
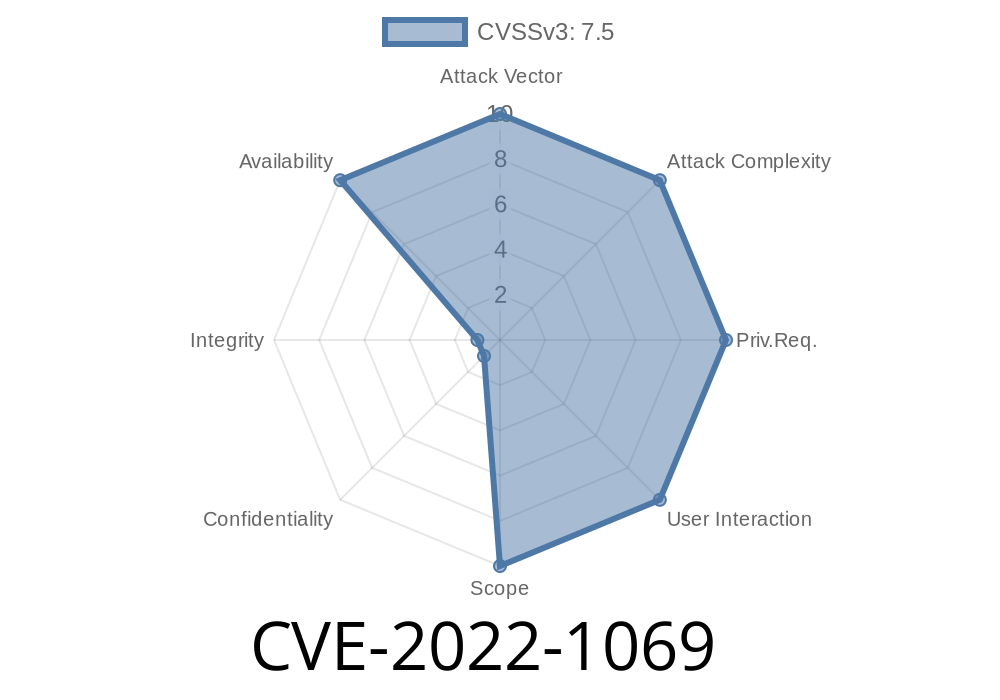
Published on: 08/17/2022 21:15:00 UTC
Last modified on: 08/19/2022 01:07:00 UTC