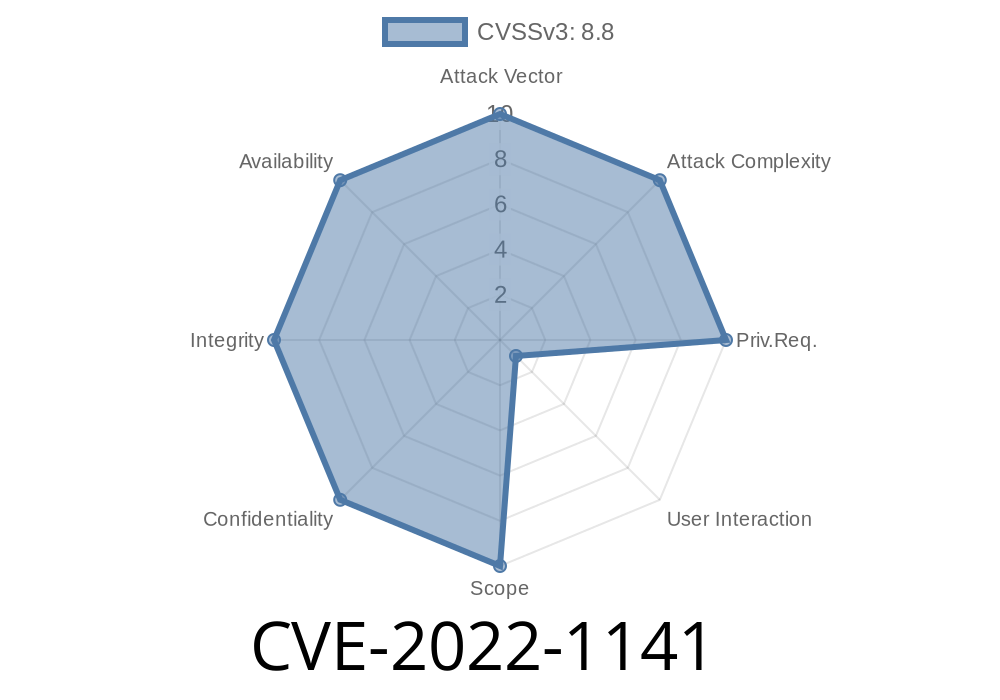
Google Chrome stands as one of the world’s leading browsers, but even giants have weak moments. CVE-2022-1141 is a “use-after-free” vulnerability in Chrome’s File Manager. Before version 100..4896.60, remote attackers could trigger dangerous heap corruption — potentially taking control of a system — if they convinced a user to interact in a specific way. This post breaks down what went wrong, shows how attackers exploit the bug, and gives code snippets and references for your deep dive.
What Is CVE-2022-1141?
CVE-2022-1141 is a vulnerability affecting Google Chrome that leverages a use-after-free bug in the browser’s File Manager. “Use-after-free” means the browser is using (or pointing to) a part of memory that has already been given up (“freed”), which opens the door to attackers.
Official summary:
> “Use after free in File Manager in Google Chrome prior to 100..4896.60 allowed a remote attacker who convinced a user to engage in specific user interaction to potentially exploit heap corruption via a crafted HTML page.”
Exploitability
Attackers must trick the user into a specific interaction—for example, dragging and dropping files, interacting with certain file dialogs, or using a specially crafted website designed to trigger the bug.
Technical Breakdown: Use-After-Free in File Manager
Browsers like Chrome rely heavily on C++ for their internals. In C++, memory issues like use-after-free can have fatal security impacts.
Imagine Chrome’s File Manager opens a file dialog. Due to a ref-counting error, a chunk of memory (like a file entry object) is freed—but Chrome still holds a pointer to it. If the attacker is crafty, they can force Chrome to use that “dangling pointer,” leading to heap corruption.
This corruption is a hacker-gold opportunity: with careful manipulation, they can sometimes execute malicious code.
Here’s a *simplified* version of what might happen in the vulnerable code
// Open a file dialog
FileEntry* entry = new FileEntry();
HandleUserInteraction(entry); // User clicks something
// Some code path frees the entry (but pointer still used elsewhere)
delete entry;
// Later, Chrome tries to access the now-freed entry
entry->Open(); // <-- use-after-free occurs here!
In real Chrome code, the setup is more complex, but the heart of the bug is a dangling pointer—pointing into freed memory.
Heap Spraying: Flooding the heap so freed memory gets filled with attacker-controlled data.
2. Triggering the UAF: The browser tries to use the now-invalid pointer, but points into attacker data.
3. Hijacking Execution: If the attacker uses their data carefully, they can redirect control (jump to their code).
Example: Trigger Code Via JavaScript (Conceptual)
Here’s a *conceptual* snippet you might see used to trigger this vulnerability in a PoC (Proof of Concept):
<!-- Exploit.html -->
<input type="file" id="picker" webkitdirectory multiple>
<script>
document.getElementById('picker').addEventListener('change', function() {
// Carefully crafted manipulations to the File Manager internals
// Try to perform actions while Chrome is freeing and reusing file entries
});
// Code to "heap spray"
let arr = [];
for(let i = ; i < 100000; i++) {
arr.push(new ArrayBuffer(x100));
}
</script>
*Note:* Modern browsers have locked down many of these techniques, but the above gives a sense of how an attacker could control heap content and trigger the bug.
Proof-of-Concept
Actual exploits for Chrome vulnerabilities are rare publicly due to their impact. However, Google tracks such issues in their bug databases. For CVE-2022-1141, the Chromium Issue 1306188 (restricted at the moment) discusses the fix.
Heap is sprayed, so attacker data lands in freed memory.
6. When Chrome accesses the invalid pointer, attacker controls the outcome—maybe running code of their choice.
References
- NVD - CVE-2022-1141
- Chrome Releases: Stable Channel Update (lists the CVE in patch notes)
- Chromium Issue Tracker 1306188
- Google’s Security Blog - Use-After-Free in Chrome (learn more about UAF attacks in Chrome)
Update Chrome! Always run the latest version (at time of writing, well past 100..4896.60).
2. Be Cautious: Don’t open strange websites or click suspicious links, especially those asking you to upload files.
3. Use Security Tools: Consider browser extensions or antivirus solutions to help block suspicious content.
Summary
CVE-2022-1141 is a dangerous but now-patched vulnerability that shows how easy it can be for a bug in complex C++ code to become a system-wide risk. By understanding how such use-after-free bugs are exploited, users and developers alike can better protect themselves—and help keep the web a little bit safer.
Stay safe, and always keep your browser up-to-date!
Timeline
Published on: 07/23/2022 00:15:00 UTC
Last modified on: 08/15/2022 11:16:00 UTC