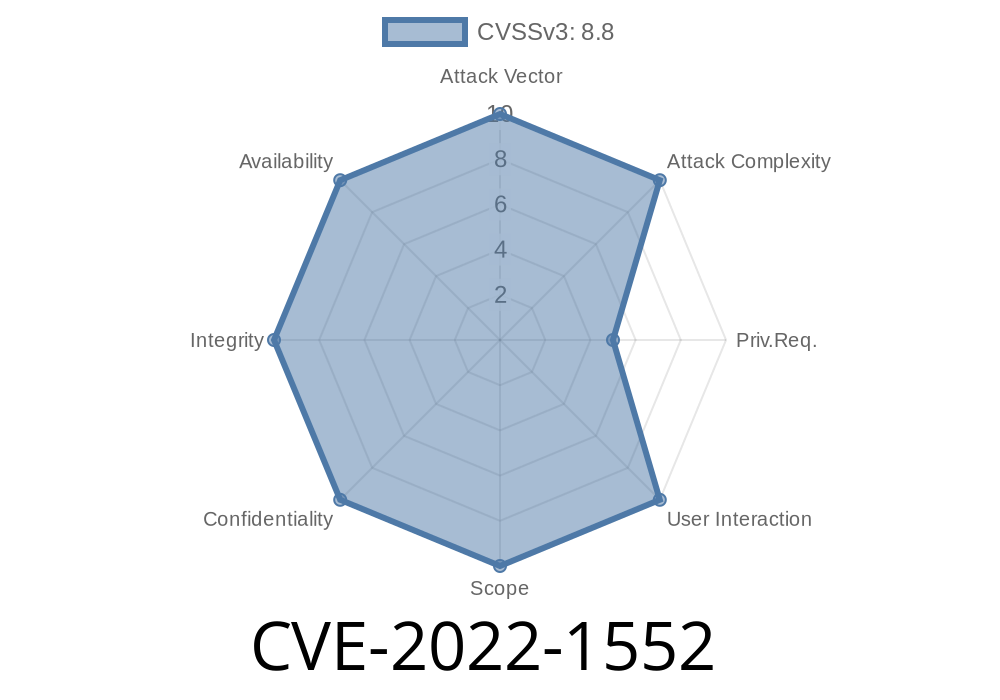
PostgreSQL is known for its robustness and focus on security. But in 2022, researchers uncovered a serious flaw, CVE-2022-1552, that lets someone with certain permissions take over the highest privilege in the system: the superuser identity.
In this post, I’ll break down what went wrong, how an attacker could exploit it, and what you must do if your database could be at risk.
The Flaw in Simple Terms
PostgreSQL lets a privileged user—like a database admin—maintain or clean up database objects (like tables and indexes) owned by other users. Some key maintenance commands are Autovacuum, REINDEX, CREATE INDEX, REFRESH MATERIALIZED VIEW, CLUSTER, and pg_amcheck.
However, these commands didn’t activate the right security protections early enough (or at all in some cases). This timing gap allowed certain users to run SQL code during privileged operations and have that code execute as if a superuser had run it.
In plain English: If you could create a table or some object in the database, you might be able to trick routine maintenance to run your malicious code with full, unrestricted access.
You let users create permanent (not temporary) objects in a database schema.
- Your system runs any of the affected PostgreSQL versions (before 14.3, 13.7, 12.11, 11.16, or 10.21) without the patch.
You don't tightly control access for non-superusers.
Example scenario:
A developer hires an intern or lets an app create its own tables. That user is not a superuser, but does have rights to make new tables. Without realizing it, regular clean-up routines could run malicious code crafted by that user, with full database power.
How the Exploit Works
A crafty attacker would use *object creation rights* in their schema to plant objects (like indexes or tables) with dangerous expressions inside. When a privileged command such as REINDEX or CREATE INDEX acts on these, it unknowingly runs user-supplied functions with superuser rights.
Exploit happens:
The index expression is evaluated as a superuser. The function runs, giving the attacker superuser rights.
Note: This is a heavily simplified example and would need slight adaptation depending on the protection level and configuration.
More in-depth technical write-ups
- Official PostgreSQL Security Advisory
- SecurityTrack - CVE Details
2. Restrict Object Creation Rights
Carefully review which users or roles can create permanent objects in shared schemas.
3. Audit Existing Objects
Check for any user-owned objects (tables, indexes, functions) in shared schemas that could have malicious payloads.
4. Minimize Superuser Operations
Don't run maintenance commands as a superuser unless necessary.
Conclusion
CVE-2022-1552 is a reminder that even respected systems like PostgreSQL can have simple-but-dangerous holes where routine administration crosses streams with user-controlled code. Tight permissions and fast patching are your best friends here.
Stay safe, patch early, review your permissions, and keep your database air-tight. If you want deeper technical details, check out the official PostgreSQL advisory or CVE entries for more.
References and Further Reading
- NVD Listing for CVE-2022-1552
- Official PostgreSQL Security Advisory
- Debian Security Tracker
- GitHub Report and Patch Discussion
Timeline
Published on: 08/31/2022 16:15:00 UTC
Last modified on: 11/22/2022 06:15:00 UTC