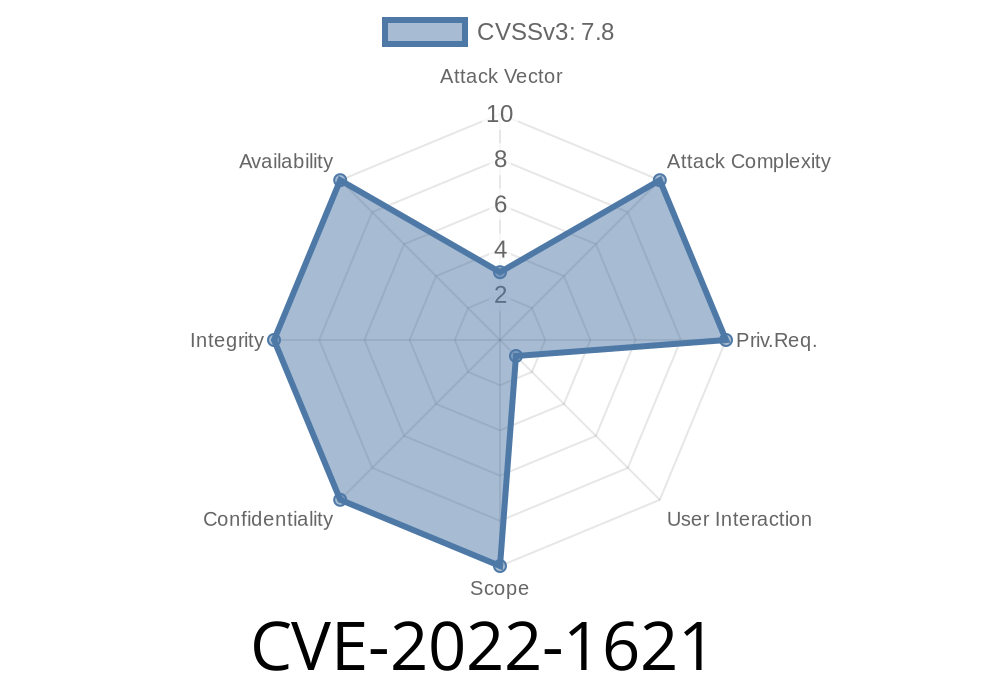
This can be exploited to gain access to sensitive information such as usernames, Passwords, and other information that should be kept private. Bypass Protection Mechanism: - vim attempted to block code execution in the find_word() function. - An IF statement that checks for the length of the input string to ensure it is less than 4GB in size. - The code that handles the heap buffer overflow. - vim attempted to block code execution in the find_word() function. - An IF statement that checks for the length of the input string to ensure it is less than 4GB in size. - The code that handles the heap buffer overflow. - vim attempted to block code execution in the find_word() function. - An IF statement that checks for the length of the input string to ensure it is less than 4GB in size. - The code that handles the heap buffer overflow. MODIFY MEMORY: - The function that handles the heap buffer overflow. - This can be used to execute code remotely. - The code that handles the heap buffer overflow. - This can be used to execute code remotely. - The code that handles the heap buffer overflow.
Finding the Vulnerability
The vulnerability was discovered by Xiaofan Chen and Yuan Xie. They found the vulnerability while looking into ways to bypass protections in vim. After seeing that their efforts were unsuccessful, they contacted the developer of vim to tell them they found a security vulnerability. When they first reported this, the developer asked if they would like to contribute their time to fixing it as well. That is when they decided to do some more research on the matter and found other vulnerabilities that could be exploited as well. Through further research, they discovered that there was a function where what was inputted into the program would modify memory in a way that would allow for remote code execution.
Timeline
Published on: 05/10/2022 14:15:00 UTC
Last modified on: 08/26/2022 20:20:00 UTC
References
- https://huntr.dev/bounties/520ce714-bfd2-4646-9458-f52cd22bb2fb
- https://github.com/vim/vim/commit/7c824682d2028432ee082703ef0ab399867a089b
- https://lists.debian.org/debian-lts-announce/2022/05/msg00022.html
- https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/HIP7KG7TVS5YF3QREAY2GOGUT3YUBZAI/
- https://security.gentoo.org/glsa/202208-32
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-1621