allowing arbitrary code execution. Both plugins were updated in version 2.0.7 to prevent this vulnerability. You can upgrade your JupiterX installation to the latest version by: Updating your JupiterX Core plugin by updating the version number in the plugin's configuration file or downloading the new version here: https://github.com/JupiterProject/JupiterX-Core/releases Updating the JupiterX Uninstall template by updating the version number in the template's configuration file or downloading the new version here: https://github.com/JupiterProject/JupiterX-Uninstall/releases
Finding and Fixing a Plugin Vulnerability with Core's Template System
JupiterX is a framework for building web applications that makes it easy to create powerful, highly scalable and secure websites. JupiterX provides a set of pre-built plugins for common tasks such as authentication, routing and authorization. The JupiterX Core plugin includes the JupiterX library and is available on the plugin repository at https://github.com/JupiterProject/JupiterX-Core. The Uninstall template is used to completely remove all references to plugins in your application's code or in system configuration files.
If you have found an issue with one of the built-in plugins, it is recommended that you first ask support for help in identifying the issue before attempting to fix it yourself: https://jupiterx.c3slabs.com/support/. If they cannot help you identify the issue, please contact us through http://jupiterx.c3slabs.com/contact/, provide as much detail about the problem as possible so we can better assist you!
Overview: 'Javascript error automatically executes code' Vulnerability
A 'Javascript error automatically executes code' vulnerability has been identified in JupiterX and the developer of JupiterX has released a new version that fixes this issue.
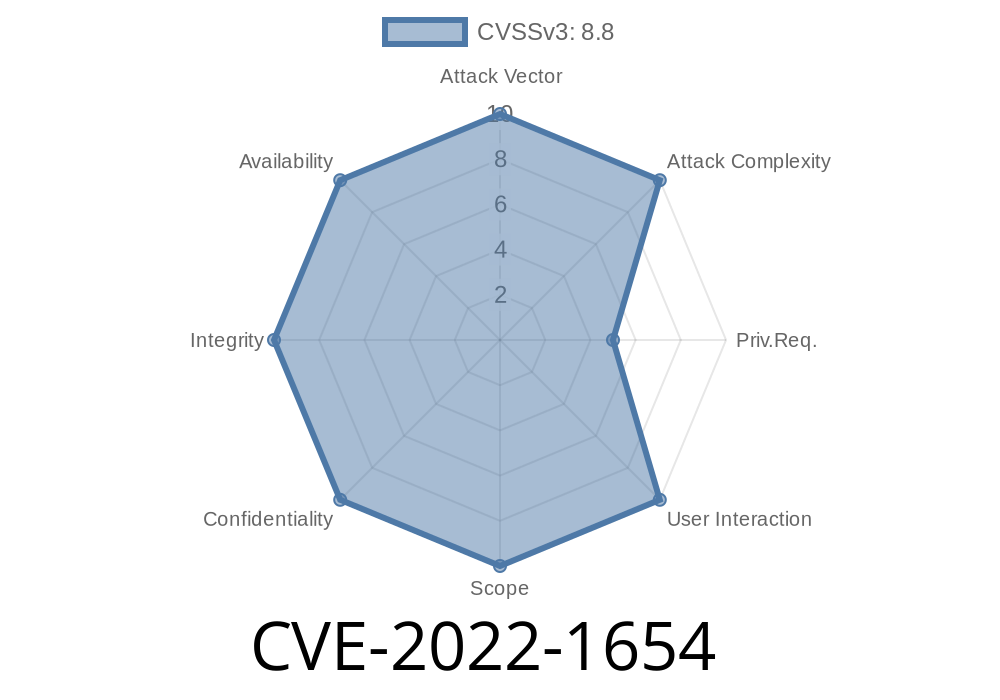
CVE-2022-1654
Summary:
CVE-2022-1654 is a vulnerability in the JupiterX plugin that allows for arbitrary code execution. JupiterX was updated to fix this vulnerability on May 10, 2017.
How do I know if my installation is vulnerable to this issue?
You should upgrade to the latest version of JupiterX-Core and JupiterX-Uninstall immediately.
The following versions were vulnerable and have been fixed:
JupiterX-Core 2.0.7
JupiterX-Uninstall 2.0.7
Timeline
Published on: 06/13/2022 14:15:00 UTC
Last modified on: 06/21/2022 21:02:00 UTC