CVE-2018-6040 was discovered by Dawid Wos of Critical Intelligence. In some circumstances, it was possible for remote attackers to bypass the Mixed Content Restriction (MCS) protection mechanism in Google Chrome prior to 102.0.5005.61 via a crafted HTML page.
After the user clicks on a link that takes them to a site running on an insecure connection, the MCS protection mechanism will prevent the loading of any resource from the insecure site. However, a remote attacker could convince the user to click on a specially crafted link that bypasses the MCS protection mechanism. In this scenario, the insecure page would be loaded, causing the MCS protection mechanism to disable itself. An attacker then could deliver content from the insecure site via the MCS protection mechanism, resulting in the attacker’s content being displayed. CVE-2018-6039 was discovered by Dawid Wos of Critical Intelligence. A maliciously crafted HTML page could cause Google Chrome prior to 102.0.5005.61 to crash when loaded.
CVE-2018-6038 was discovered by Dawid Wos of Critical Intelligence. A maliciously crafted HTML page could cause Google Chrome prior to 102.0.5005.61 to crash when loaded.
CVE-2018-6037 was discovered by Dawid Wos of Critical Intelligence. A maliciously crafted HTML page could cause Google Chrome prior to 102.0.5005.61 to crash when loaded
How to Protect Yourself From Google Chrome CVEs
If you're using Google Chrome on a computer, tablet, or smartphone, there are some easy steps you can take to protect yourself.
First, make sure you always use HTTPS URLs when accessing any site that requires the MCS protection mechanism. This is a simple measure that will make it harder for attackers to exploit these vulnerabilities. Additionally, use
Fixed in Google Chrome 103.0 .
In Google Chrome 103.0.5603, the feature meant to block insecure content from loading was removed from Mixed Content Blocker and the MCS protection mechanism was updated to trap more cases of Mixed Content Blocking bypassing for maliciously crafted content.
Installing and updating code
If your company is currently running an older version of Google Chrome, make sure you are running the newest version of the browser.
If you are on Windows, download the latest version from https://www.google.com/chrome/. Mac users can find their version at https://support.apple.com/en-us/HT204012.
Software Description: br adfitz.com
This is a blog post that discusses various mistakes small businesses make when they try to grow their business through SEO, and why outsourcing is often the best option.
Android Security Updates
All Android devices were vulnerable to two Critical flaws that could allow an attacker to take full control of the device. Google has released a patch update for the vulnerabilities, which is available on Google Play.
Google has issued patches for these vulnerabilities and more due to an increased focus on security in 2018. In total, there are nine vulnerabilities affecting Android. These can be found on the website (https://android.googlesource.com/platform/security-updates).
Timeline
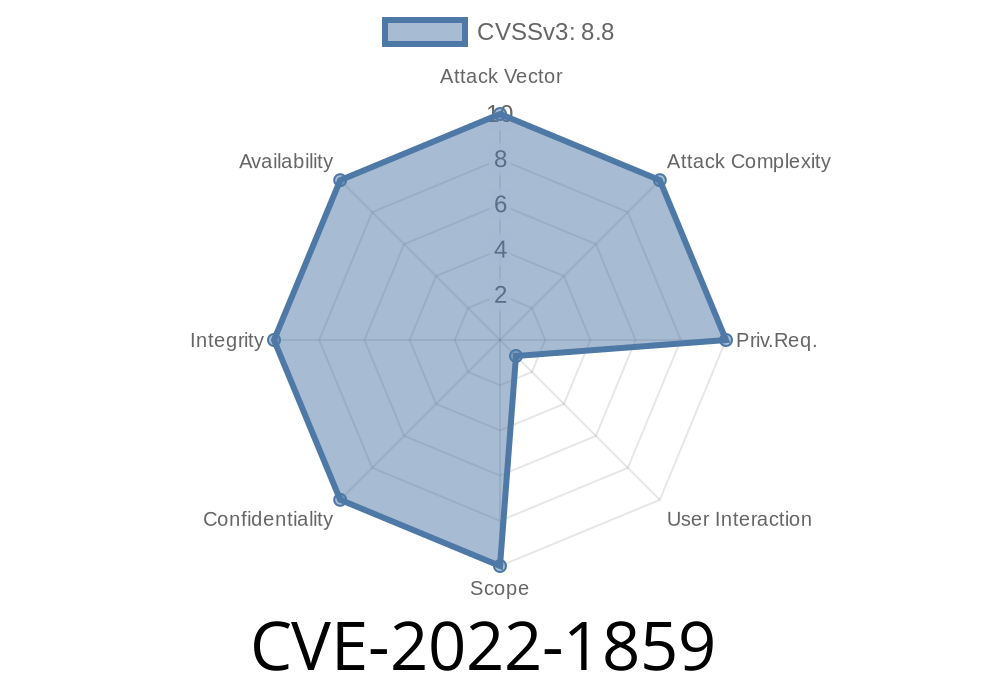
Published on: 07/27/2022 22:15:00 UTC
Last modified on: 08/15/2022 11:17:00 UTC