This issue has been resolved in GitLab EE versions 15.1.1, 15.0.4, and 15.0.3. However, it is recommended to upgrade to the latest version. If you are running an older version, it is recommended to restrict access to the REST API to only authorised users. Access to the REST API can be restricted per project by adding the following directive to the project’s .gitlab-ci.yml file: -external-rest-api: true Access to the command line can be restricted per user by adding the following directive to the user’s .gitlab-ci.yml file: -external-rest-api: true The issue has been resolved in GitLab EE versions 15.0.4 and 15.0.3. However, it is recommended to upgrade to the latest version. If you are running an older version, it is recommended to restrict access to the REST API to only authorised users. Access to the REST API can be restricted per project by adding the following directive to the project’s .gitlab-ci.yml file: -external-rest-api: true Access to the command line can be restricted per user by adding the following directive to the user’s .gitlab-ci.yml file: -external-rest-api: true
Issue summary :
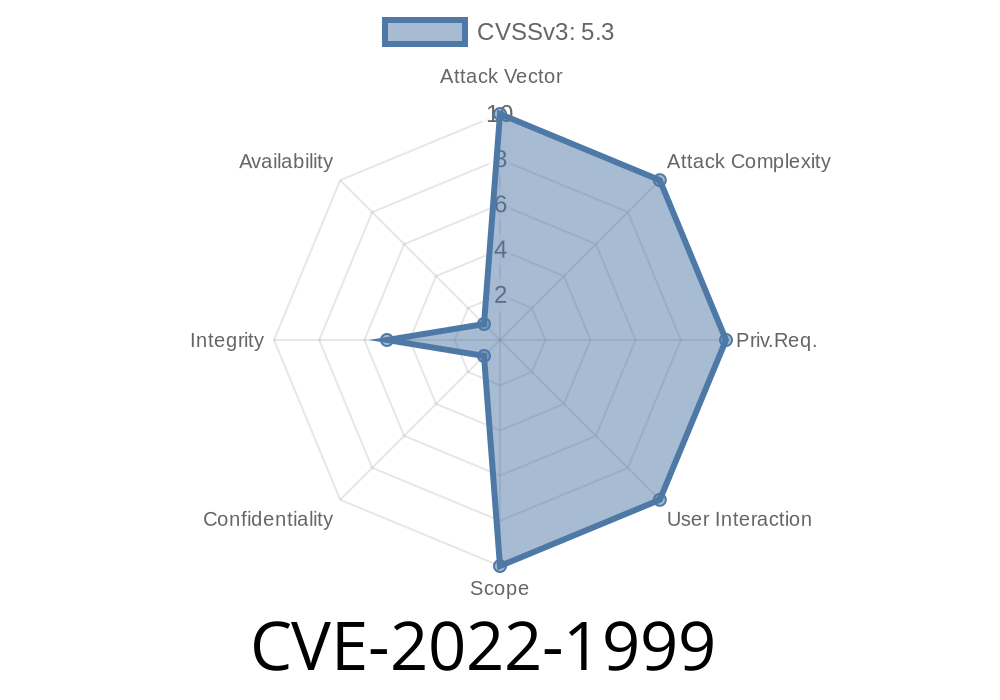
CVE-2022-1999: GitLab EE versions 15.1.1, 15.0.4, and 15.0.3 have a REST API issue where any authenticated user can read any other user's repositories when the REST API is unrestricted, which includes the ability for an authenticated user to list all users on the system regardless of whether they are logged in or not
GitLab Community Edition (CE)
GitLab CE is a free and open source (FOSS) software project that enables teams to collaborate on code and build software reliably. GitLab EE is the next-generation product that replaced GitLab CE in October 2015.
While GitLab CE has been deprecated, it remains supported for legacy projects, third-party integrations, and custom development workflows. For these use cases, features like the bug tracker are not available in GitLab EE.
The issue has been resolved in GitLab EE versions 15.1.1, 15.0.4, and 15.0.3. However, it is recommended to upgrade to the latest version. If you are running an older version, it is recommended to restrict access to the REST API to only authorised users. Access to the REST API can be restricted per project by adding the following directive to the project’s .gitlab-ci.yml file: -external-rest-api: true Access to the command line can be restricted per user by adding the following directive to the user’s .gitlab-ci.yml file: -external-rest-api: true
Versioning and switching between EE versions
If you are using GitLab EE v15.x, we recommend switching to EE v16.x during the upgrade process. If you use the 15.x version and want to stay on that version, it is not possible to switch between the two versions without first upgrading to EE v16.x. You can continue to use GitLab EE v15.x for your projects as long as you are willing to downgrade to GitLab EE v14 or earlier if necessary in order to seamlessly transition projects from EE v15.x back to 14 or earlier versions of GitLab Enterprise Edition (EE).
This issue has been resolved in GitLab EE versions 15.0.4 and 15.0.3, but it is recommended that customers upgrade their instances of GitLab Enterprise Edition (EE) at their earliest convenience due to vulnerability CVE-2022-1999 introduced in this release which may result in an unauthorized access of your instance by unauthorized users or malicious third parties.
Timeline
Published on: 07/01/2022 17:15:00 UTC
Last modified on: 07/13/2022 18:41:00 UTC