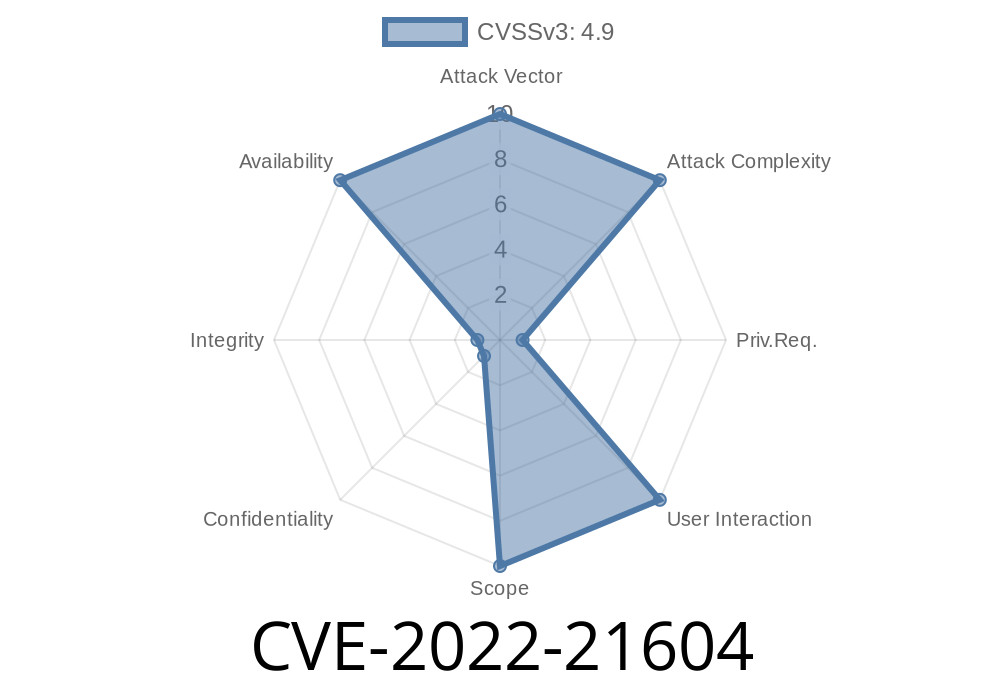
RedTeam Pentesting discovered this vulnerability in MySQL version 8.0.30, which is currently used in production by many companies. The vulnerability can be exploited by malicious users to cause high availability issues. Attackers can crash a MySQL server by sending specially crafted queries. Once the server is down no further connections can be processed, making it an easy task for an attacker to force a server to crash. This vulnerability is related to CVE-2017-10267 and can be exploited by malicious users to crash MySQL server. This is not a critical issue since the MySQL server is not used in production in most cases. However, it is highly recommended to upgrade MySQL version to the latest one as soon as possible. RedTeam Pentesting recommends to apply the following mitigations for this vulnerability: Upgrade MySQL server to the latest version.
If possible, disable remote queries in your application.
If possible, restrict access to the MySQL server to trusted network locations. RedTeam Pentesting suggests to apply the following preventative measures: Restrict access to the MySQL server to trusted networks.
Disallow remote access to the MySQL server.
Disable remote queries.
MySQL Vulnerability and Exploitation
Designers of MySQL decided to introduce the possibility to run remote queries (one-to-one or many-to-many) on the server. This option is intended for use in development and test environments such as those used by a testing team in a company or an open source project.
Ubuntu 16.04 LTS ships with MySQL version 8.0.30 which includes this vulnerability, but it is not used in production environments since for most companies there are other databases that are more suitable for their needs.
Timeline
Published on: 10/18/2022 21:15:00 UTC
Last modified on: 10/18/2022 21:18:00 UTC