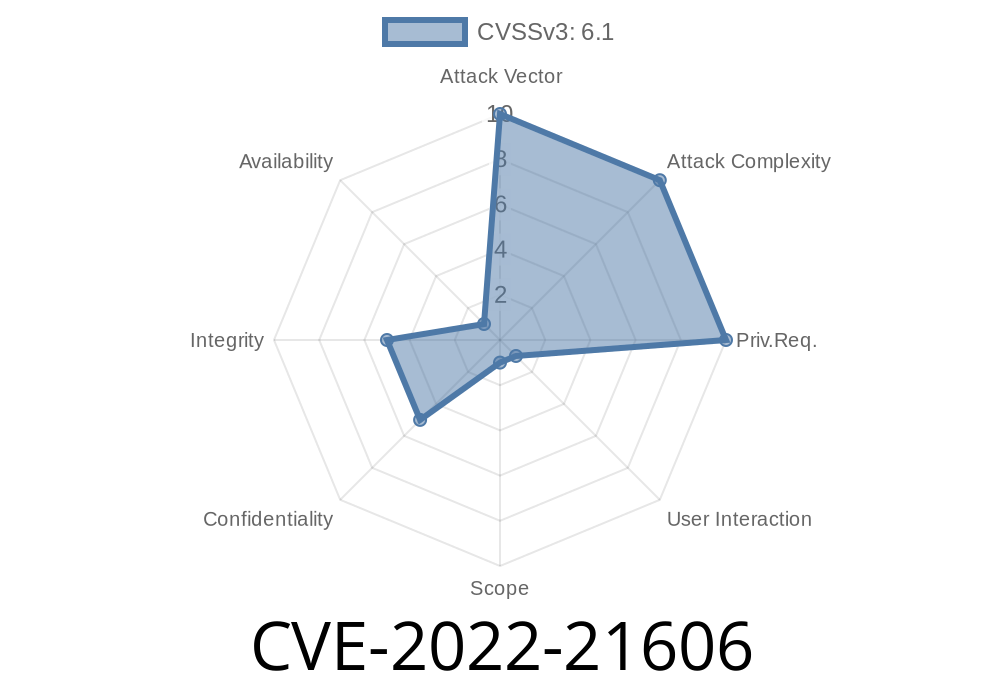
Exploitation You can exploit this vulnerability by sending a malicious request to the server via HTTP. Successful exploits may allow an attacker to access to data or create a Denial of Service condition. Fix Information There is no known fix for this at this time. However, in 18c, a new feature was introduced to prevent this type of attack. To prevent this vulnerability from being exploited, change the default trusted hosts setting for your oracle instance to only allow trusted hosts to connect. For more information, see the Recommended best practices for securing Oracle Database Server article. End users can also limit access to the HTTP protocol by unchecking the HTTP/HTTPS proxy setting in their system properties. CVSS 3.0 Base Score 6.9. CVSS Vector: Access Vector Access Complexity Authentication Remote Confirmation Access Vector Unrestricted Remote Exploit Remote Confirmation Access Complexity Low Authentication None Remote Sensitive Data When this vulnerability is exploited, data may be accessed by unauthorized persons.
Oracle Database Server
Oracle Database Server is a database software product developed by Oracle Corporation. Oracle Database Server is available in two editions: Standard Edition and Enterprise Edition. The Standard Edition of the Oracle Database Server is intended to be used in small, medium-sized, and large business organizations where the database server is the primary computer on which Oracle software runs. In contrast, the Enterprise Edition of the Oracle Database Server is intended to be used by large enterprises that require additional computing resources or storage capacity.
Timeline
Published on: 10/18/2022 21:15:00 UTC
Last modified on: 10/18/2022 21:18:00 UTC