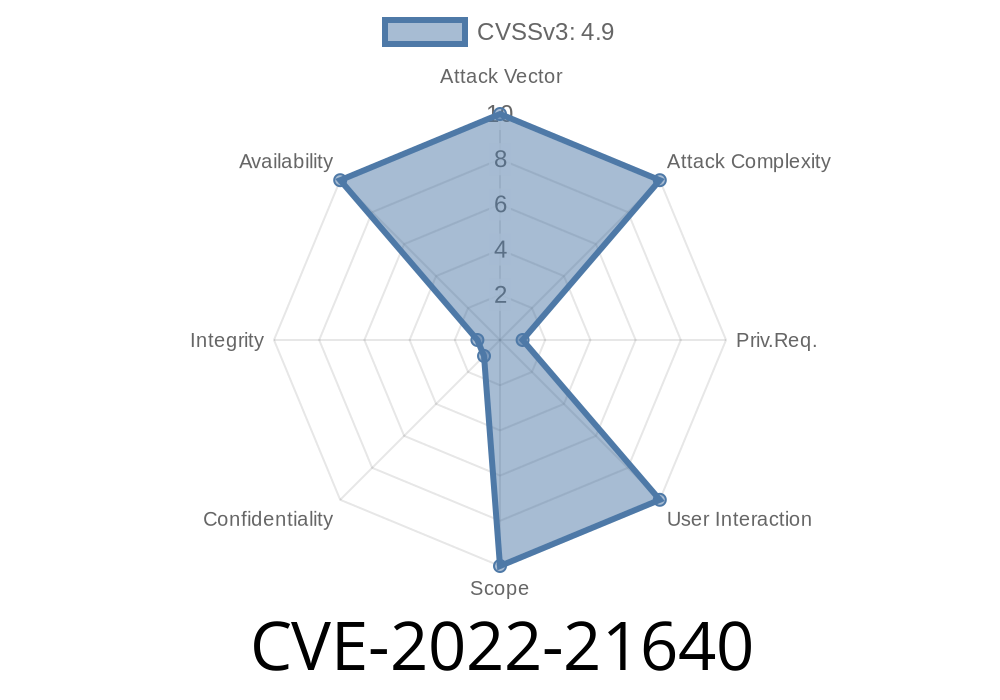
Vulnerable versions can be exploited through InnoDB privilege user account, which allows high privileged user account to exploit these vulnerabilities. Bugtraq ID: 9361 Exploiting the vulnerability requires remote user to have SQL privilege, otherwise cannot be exploited. CVSS 3.1 Base Score 5.6 (Privilege escalation). Vulnerable Software Versions If you are using MySQL 8.0 or below, you are vulnerable. CVSS 3.0 Severity Score and Metrics If you are using MySQL 8.0 or below, you are vulnerable. Confidentiality Impact NONE Confidentiality Impact NONE Integrity Impact NONE Integrity Impact NONE Availability Impact HIGH (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) Availability Impact HIGH (CVSS:3.0/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) Remote Exploitable Vulnerability N/A Local Exploitable Vulnerability HIGH (CVSS:3.0/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) Known Vulnerabilities CVE-2017-10267 CVE-2017-10268 CVE-2017-10269 CVE-2017-10
MySQL Product Information
MySQL is a relational database management system. It consists of client software, the mysqld server daemon, and libraries. The modern version of MySQL is developed by Oracle Corporation, which offers support and services for MySQL.
MySQL Database Exposes the Admin Backend Panel
InnoDB privilege user account, which allows high privileged user account to exploit these vulnerabilities.
MySQL Database Vulnerabilities
Mysql is an open-source, cross-platform relational database management system. It is the most popular database server in use today. MySQL is a very powerful tool for all types of users, from small business owners to senior enterprise IT managers.
Mysql has multiple vulnerabilities that have been discovered and patched over the past few months. These vulnerabilities are perfect for hackers and cyber criminals who want to exploit the security holes in order to steal data or mount a distributed denial of service (DDoS) attack.
Most of these recent vulnerabilities have been found in MySQL 8.0, which was released on October 15th 2016 as part of 5.5 series update. If you are using versions below 8.0, you are vulnerable to attack by hackers and cybercriminals looking for easy prey.
Timeline
Published on: 10/18/2022 21:15:00 UTC
Last modified on: 10/18/2022 21:18:00 UTC