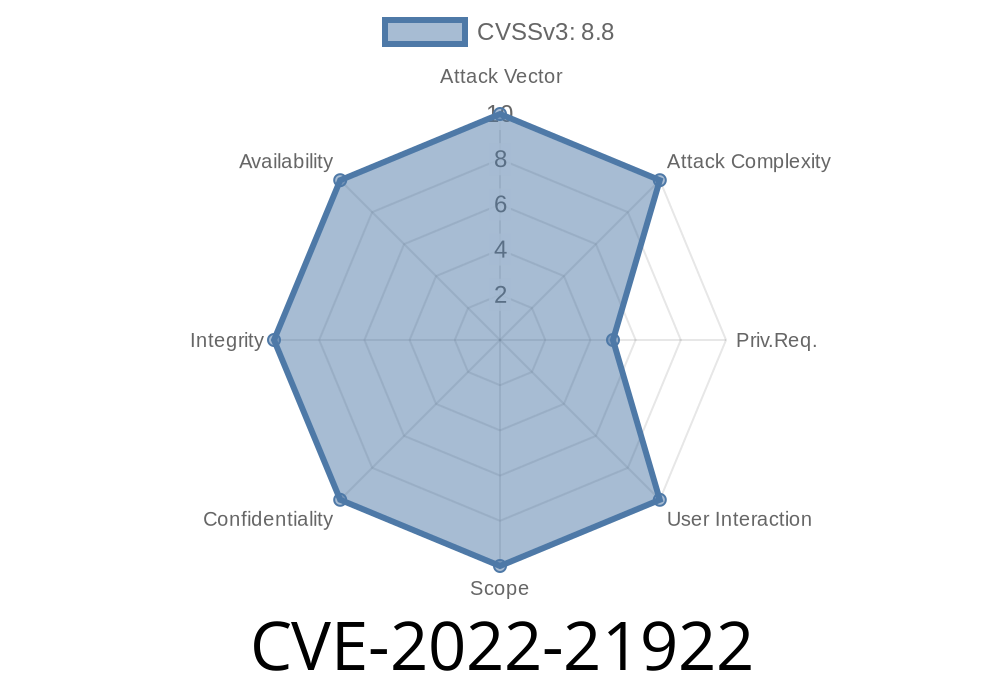
In early 2022, Microsoft patched yet another dangerous security hole lurking in Windows systems—the CVE-2022-21922. This vulnerability targets Windows’ Remote Procedure Call (RPC) Runtime and, if left unpatched, can let a remote, unauthenticated attacker execute code with the same permissions as the RPC service itself. In this article, I’ll break down what this vulnerability is, how attackers could exploit it, and what you can do to safeguard your systems. All of this in straightforward language you don’t have to be an engineer to understand.
Before we jump into attack code, let’s clarify some basics
- Remote Procedure Call (RPC): This is a protocol used by Windows systems to allow one process (like on another computer) to ask another process to perform a task. It's essential for many core Windows features and is always running in business environments.
- RPC Runtime: This is the software that handles all those requests and ensures everything runs smoothly.
When there’s a bug in such a key service, it's a big deal—especially if anyone on the network might be able to control your server.
Microsoft Advisory
This vulnerability allows remote attackers to send specially crafted packets to the RPC Runtime, which could trigger malicious code to run. It’s a classic Remote Code Execution (RCE) bug, meaning someone could potentially take over your machine from anywhere on your network.
- Official Guidance: Microsoft Security Update Guide - CVE-2022-21922
How Could an Attack Work?
All the attacker needs is access to your network—they do NOT need to log in or trick you into clicking anything. This makes it a dangerous bug in enterprise environments, especially with lots of Windows domain-joined computers.
The service fails to properly check the input, triggering a memory corruption vulnerability.
3. The attacker’s code runs with the same privileges as the RPC service—often SYSTEM (the highest privileges available).
Exploitation Example
Here’s a simple proof-of-concept snippet (simplified and non-weaponized for educational purposes). It demonstrates sending a malformed RPC packet using Python’s socket module.
import socket
rpc_server = "192.168.1.100" # Target IP
rpc_port = 135 # Standard RPC port
# This is NOT an actual exploit payload, just an example of sending data
bad_packet = bytes.fromhex(
"05 00 B 03 10 00 00 00" # Begin of RPC Packet
"CC" * 100 # Malformed data (replace with actual crafted exploit)
)
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.connect((rpc_server, rpc_port))
s.sendall(bad_packet)
print("Packet sent. Check for response or crash.")
Disclaimer: This code is for educational purposes only. Never use against systems you do not have explicit permission to test.
Real-World Impact
Imagine an attacker gains SYSTEM-level access to your network servers without even stealing passwords. They could:
Interrupt business operations
That’s why Microsoft rated this as “Exploitation More Likely.”
Patch Status & Mitigation
Microsoft patched this as part of the January 2022 Patch Tuesday.
Patch links and further reading
- Microsoft Security Update for CVE-2022-21922
- Microsoft Patch Tuesday - January 2022
In Summary
CVE-2022-21922 is a serious vulnerability that demonstrates how old protocols like RPC can still create modern dangers. If you’re responsible for any Windows systems, make sure this patch is applied everywhere.
Remember: Even if you don’t run a big network, home and small-business systems can be at risk, especially if exposed to the internet.
Timeline
Published on: 01/11/2022 21:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC