Microsoft has released security bulletin MS17-010 to address this security issue. In short, a remote code execution vulnerability exists in Microsoft Office software when Windows fails to provide integrity checks for specially crafted files. Attackers can leverage this vulnerability to execute malicious code on affected systems. The severity of this issue depends on the environment and company policies. Microsoft recommends installing this security update and review security policy documentation to help protect against the risk of this issue. Microsoft has released security bulletin MS17-010 to address this security issue. In short, a remote code execution vulnerability exists in Microsoft Office software when Windows fails to provide integrity checks for specially crafted files. Attackers can leverage this vulnerability to execute malicious code on affected systems. The severity of this issue depends on the environment and company policies. Microsoft recommends installing this security update and review security policy documentation to help protect against the risk of this issue. - Exploitation of this vulnerability requires that a user has opened a malicious Office file or visited a malicious website. - Exploitation of this vulnerability requires that user have not enabled Protected View in Microsoft Edge. - Microsoft Outlook on Windows 10 Anniversary Update and Windows Server 2016 is not affected by this issue.
Summary
A remote code execution vulnerability exists in Microsoft Office software when Windows fails to provide integrity checks for specially crafted files. Attackers can leverage this vulnerability to execute malicious code on affected systems. The severity of this issue depends on the environment and company policies. Microsoft recommends installing this security update and review security policy documentation to help protect against the risk of this issue.
The vulnerability is addressed by MS17-010, released by Microsoft on March 14, 2017.
Microsoft has released security bulletin MS17-010 to address this issue .
MS17-010 is Microsoft’s update to a security bulletin released in June 2017 that addressed vulnerabilities in Office software when Windows fails to provide integrity checks for specially crafted files. The vulnerability was exploited by attackers in the wild and affected systems running Windows 7, 8, or 10. MS17-010 can be installed on all versions of these operating systems and addresses the issue. To help protect against the risk of this issue, Microsoft recommends installing MS17-010 and reviewing company policies related to IT security.
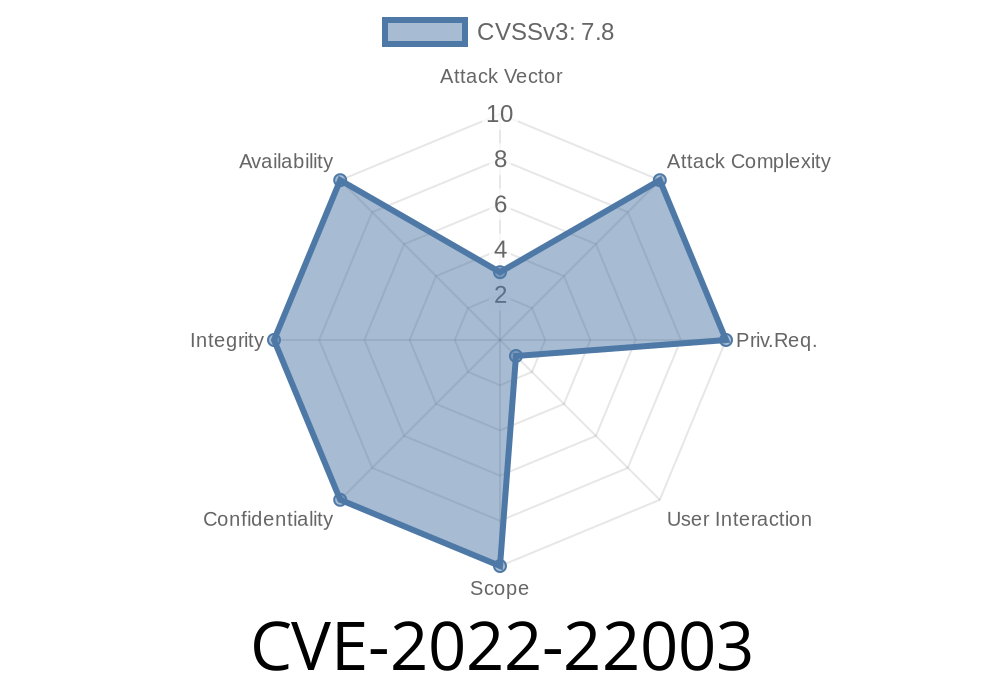
Potential benefits of Microsoft Office Server Software vulnerability CVE-2022-22003
This vulnerability affects Microsoft Office software, including Microsoft Excel and Microsoft Word. This vulnerability can be exploited when a user opens a specially crafted file or visits a malicious website. The severity of this issue depends on the environment and company policies.
As an example, the severity could depend on whether the user has enabled Protected View in Microsoft Edge for Office documents or whether the company has a policy that prevents users from opening untrusted files. Another potential benefit of this vulnerability is that it will affect users who use Outlook on Windows 10 Anniversary Update or Windows Server 2016.
Microsoft Office Software Details
Microsoft Office software that is listed below, has a vulnerability that could allow remote code execution if exploited. Microsoft recommends installing this security update and review security policy documentation to help protect against the risk of this issue.
- Windows Server 2008 R2 SP1, Windows Server 2012, and Windows Server 2012 R2
- Microsoft Office 2016 for Windows desktop editions only
- Microsoft Office 2013 for Windows desktop editions only
- Microsoft Office 2010 for Mac desktop editions only
Timeline
Published on: 02/09/2022 17:15:00 UTC
Last modified on: 02/14/2022 21:41:00 UTC