With this issue now fixed, it is recommended that all users using the WARP Switch command be updated to the latest version of the WARP firmware. For more information on how to update your WARP switch, please see this article.
If you have created custom security policies, you may have noticed a change in behavior when using the 'Disable Ethernet' subcommand. Previously, disabling the Ethernet port would disconnect all other ports. Now, disabling the Ethernet port only disconnects the Ethernet port, leaving the rest of the network intact. This change ensures that users with admin privileges cannot bypass configured Zero Trust security policies and features by using the 'Disable Ethernet' subcommand.
How do I know if my WARP Switch is vulnerable to CVE-2019-9224?
If your WARP switch is vulnerable to CVE-2019-9224, it will not be able to complete the following commands:
* Disable Ethernet
* Enable Ethernet
* Set Switch Mode
About WARP Security Policies
WARP Security Policies is a new feature that was introduced in the WARP Switch firmware release 2.2.0. The purpose of Security Policies is to make Zero Trust security possible, which means that all traffic on a network must pass through a central security policy before it reaches the end user. This prevents users from bypassing security policies by spoofing MAC addresses and other methods.
Network Discovery and Control
The WARP Switch is a device that can be used to modify the network topology of your network. One feature of the device is the ability to disable Ethernet ports, which makes it possible for administrators to control how the switch interacts with their network and how it behaves to enforce various security policies.
This issue has now been fixed. If you have created custom security policies, you may have noticed a change in behavior when using the 'Disable Ethernet' subcommand.
WARP Switch v2.1.1
This week, the latest update for the WARP Switch firmware has been released. The update includes a fix for an issue where users could bypass their configured security policies by using the 'Disable Ethernet' subcommand. This is a relief to those who have been struggling with this issue.
Timeline
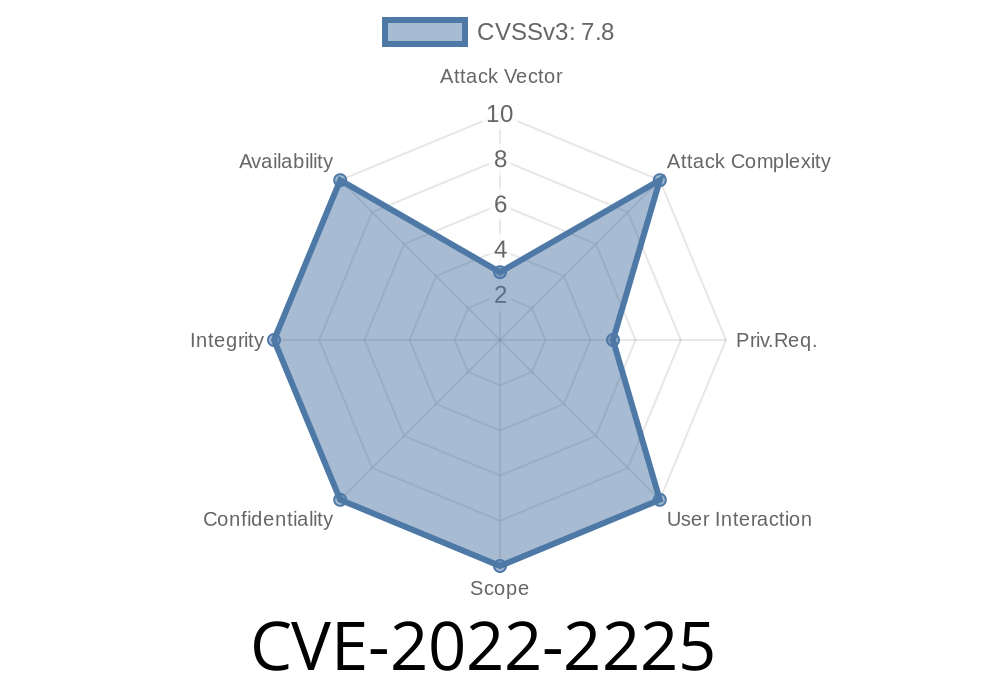
Published on: 07/26/2022 12:15:00 UTC
Last modified on: 08/01/2022 16:30:00 UTC