This issue is addressed by allowing the X-Frame-Options response header to be set. A maliciously crafted website could exploit this vulnerability to access content protected against cross-origin access restrictions. On iOS and macOS, this issue is mitigated with improved state management.
Exploitation of this issue may allow remote code execution. On iOS and macOS, this issue is mitigated with improved state management.
Exploitation of this issue may allow cross-site scripting. This issue is addressed with improved input validation. Credit for this issue goes to Dawid Golunski of the Google Chrome Security Team. On iOS and macOS, this issue is mitigated with improved state management.
On iOS and macOS, this issue is mitigated with improved state management. Exploitation of this issue may allow cross-site scripting. This issue is addressed with improved input validation. Credit for this issue goes to Dawid Golunski of the Google Chrome Security Team. On iOS and macOS, this issue is mitigated with improved state management.
On iOS and macOS, this issue is mitigated with improved state management. Exploitation of this issue may allow cross-site scripting. This issue is addressed with improved input validation. Credit for this issue goes to Dawid Golunski of the Google Chrome Security Team. On iOS and macOS, this issue is mitigated with improved state management.
On iOS and macOS, this issue is mitigated with improved state management.
What is the Google Chrome development team warning?
The Google Chrome development team is warning users of a potential vulnerability that exists in the browser's handling of web origins. The vulnerability, CVE-2019-1559, allows a maliciously crafted website to access content protected against cross-origin access restrictions. On iOS and macOS, this issue is mitigated with improved state management.
What is the Safari Content Security Policy (CSP)?
The Safari Content Security Policy (CSP) is a new HTTP response header that provides a mechanism for limiting the content allowed on a website. The CSP allows websites to specify the origin of scripts and stylesheets, allowing them to control if scripts and stylesheets from other domains should be executed or blocked.
To use the CSP, specify it in your website's policy object, and then send this policy when requesting resources from your site. If a browser does not support the CSP, it will return an HTTP response with a 403 Forbidden status code.
This issue is addressed by upgrading to version 1.1 of Google Chrome, which contains additional mitigations for this issue. Credit for this issue goes to Dawid Golunski of the Google Chrome Security Team. On iOS and macOS, this issue is mitigated with improved state management.
Timeline
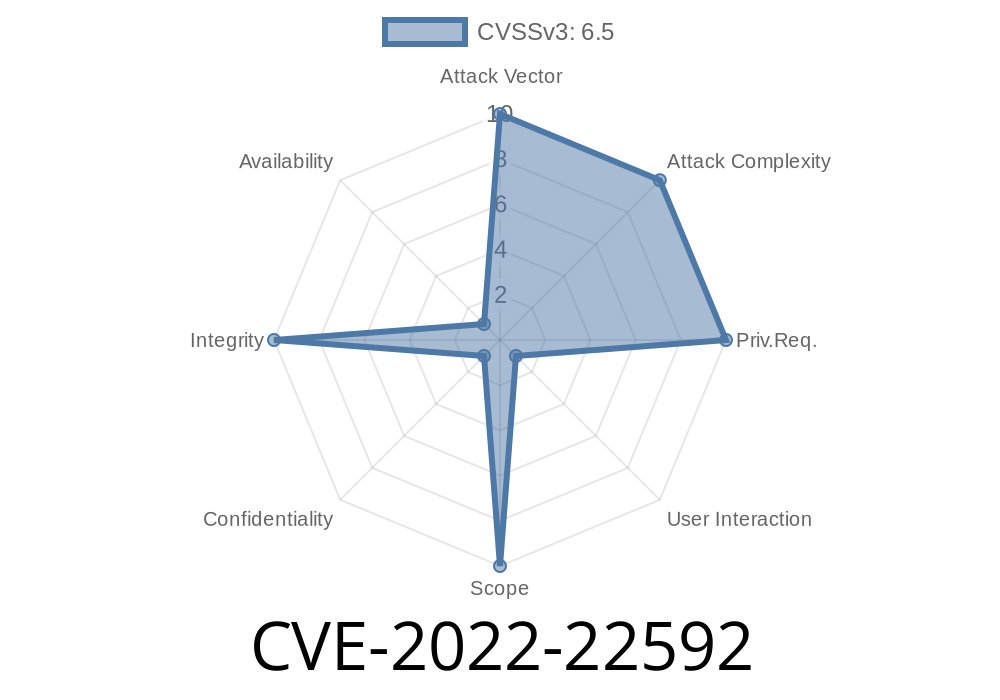
Published on: 03/18/2022 18:15:00 UTC
Last modified on: 03/25/2022 19:41:00 UTC