CVE-2025-43529 - Inside Apple’s Latest Use-After-Free Safari Flaw and Its High-Profile Exploitation
In June 2025, Apple patched a highly impactful use-after-free (UAF) vulnerability, tracked as CVE-2025-43529, across nearly its entire ecosystem. The bug was creepy, technical, and—
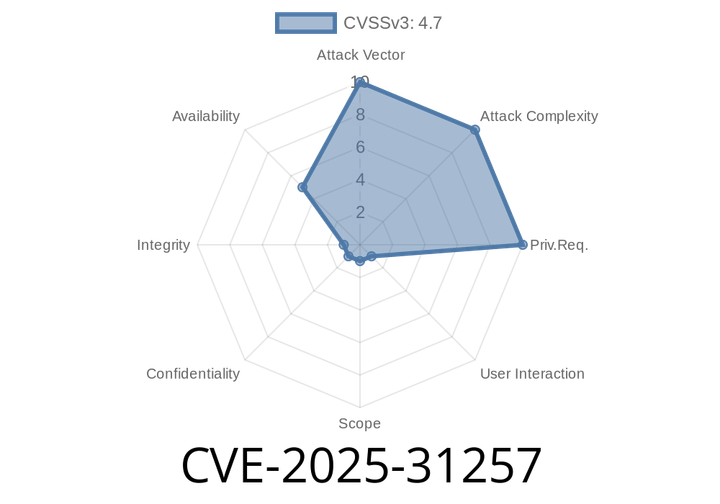
CVE-2025-31257 - Critical Safari Crash Bug Explained, Code Samples, Exploitation, and Fixes
CVE-2025-31257 is a recently disclosed security vulnerability affecting Apple's web browser, Safari, on multiple Apple platforms—iPhone, iPad, Mac, Apple TV, Apple Watch,
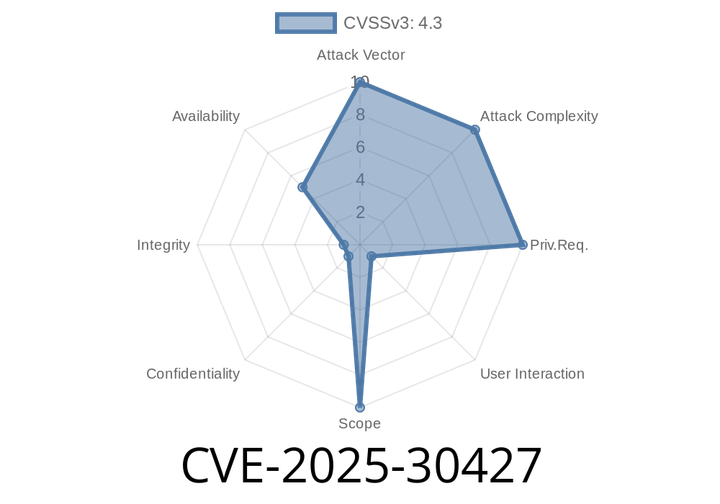
CVE-2025-30427 - Use-After-Free Vulnerability in Apple Safari - Exploit Details & Patch Guidance
Apple recently patched a critical vulnerability, CVE-2025-30427, in their Safari browser and related operating systems. Here, we break down what this vulnerability is, how it
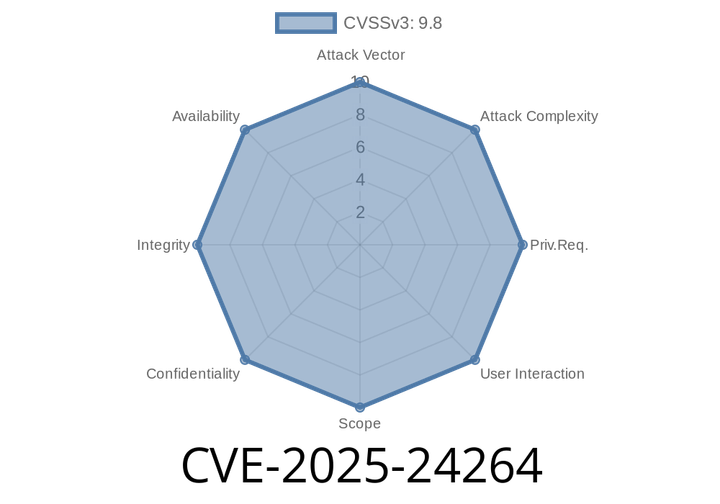
CVE-2025-24264 - How This Apple Safari Memory Bug Could Crash Your Device — Technical Deep Dive
Apple recently patched a critical vulnerability, listed as CVE-2025-24264, that could let attackers crash your Safari browser just by sending you a specially crafted web
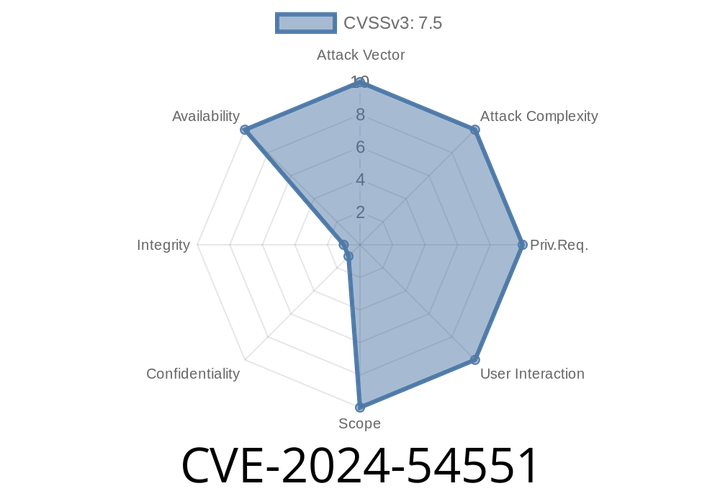
CVE-2024-54551 - Understanding the Apple WebKit Denial-of-Service Vulnerability
In June 2024, Apple patched a new security flaw labeled CVE-2024-54551. This vulnerability affected several major Apple operating systems, including iOS, macOS, watchOS, tvOS, visionOS,
Episode
00:00:00
00:00:00