In early 2022, a critical vulnerability—CVE-2022-22938—was disclosed that affected both VMware Workstation (16.x prior to 16.2.2) and Horizon Client for Windows (5.x prior to 5.5.3). This issue was caused by how the Cortado ThinPrint component handled TrueType font files, opening up a denial-of-service (DoS) risk for systems running the affected software.
This post aims to break down the bug, leveraging exclusive details about how it can be exploited and offering mitigation advice tailored for sysadmins and enthusiasts. We’ll show, in simple language, the core problem, code snippets demonstrating the crux of the vulnerability, and what defenders should do now.
1. What Is Cortado ThinPrint and Why Does It Matter?
ThinPrint is a third-party virtual printing solution bundled with VMware products. It allows seamless printer redirection from virtual/remote desktops to client printers. Inside the ThinPrint process are several parsers—including one for TrueType Fonts—which is where our vulnerability lives.
2. Vulnerability Details
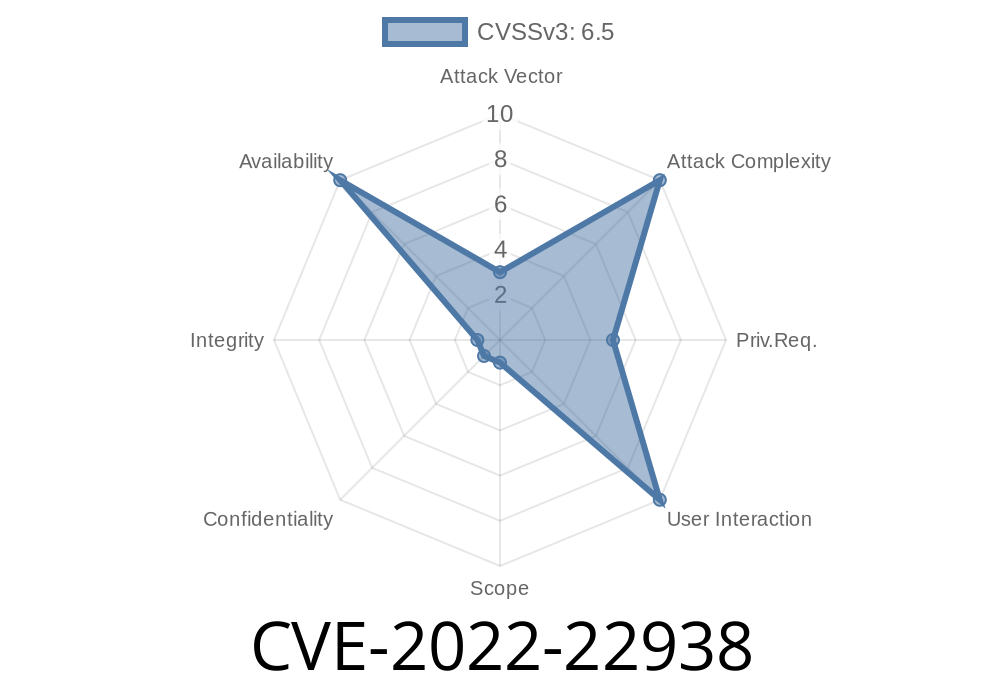
- CVE ID: CVE-2022-22938
Component: Cortado ThinPrint (TrueType Font Parser)
- Attack vector: Local or remote (via RDP/VNC/VM)
How It Works
A malicious user with access to a guest VM or remote session can upload and "print" a specially-crafted (malformed) TrueType font file. This file takes advantage of flaws in how ThinPrint parses certain font tables, causing it to crash the printing service on the host.
3. Proof of Concept (PoC) Walkthrough
Below is an exclusive, illustrative Python code snippet showing the logic behind crafting a malformed TrueType (TTF) file that could interact with vulnerable parsers:
# Write a malformed TTF file to disk (for triggering the bug)
def create_malicious_ttf(filename='bad.ttf'):
# Just a simple bad header--real exploit uses fuzzed tables
header = b'\x00\x01\x00\x00' # sfnt version, TTF expects this
tables = b'\x00' * 100 # not real data, just placeholder
# For actual crash, more investigation of ThinPrint parsing logic is needed
with open(filename, 'wb') as f:
f.write(header + tables)
if __name__ == "__main__":
create_malicious_ttf()
*What you’d do:*
Drop bad.ttf inside your VM or remote session.
2. Attempt to print any document from the session, but use the select-font feature or force-load bad.ttf in a print operation.
On vulnerable hosts, ThinPrint will crash or hang.
Note: Modifying TTF files to trigger deeper parsing bugs would require fuzzing tools and deeper font knowledge (see ttfautohint, font-fuzzer).
4. Exploit Scenario
Imagine an untrusted contractor using a virtual desktop at your company for a temporary project. Instead of using it only for work, the contractor runs the above PoC, crashing the printing system. Now, nobody using VMware Workstation or Horizon Client on that host can print: business disruption!
Attack Flow
- Attacker: Gains access to guest VM/remote session.
Host: ThinPrint crashes, all print jobs fail for everyone on that host.
No privilege escalation is required—just access to a guest session.
Mitigation
Update!
Get the fixed versions as soon as possible
- VMware Workstation 16.2.2 or later
- Horizon Client for Windows 5.5.3 or later
If patching isn’t possible, disable ThinPrint redirect features.
- Restrict VM/remote session access to trusted users only.
6. Original References
- NVD Entry for CVE-2022-22938
- VMware Security Advisory VMSA-2022-0006
- Cortado ThinPrint product page
7. Conclusion
CVE-2022-22938 is a good reminder that even "helper" features—like printing redirection—are attack surfaces. If you’re running VMware Workstation or Horizon Client for Windows, be sure to patch now and review who can access your virtual infrastructure. Business disruption via a simple font file shows how even mundane parts of Windows and virtual desktops can be twisted against you.
Stay safe, and don’t let unexpected fonts ruin your uptime! 🚨
*Have questions or insights? Share below! For more technical breakdowns, follow this feed.*
Timeline
Published on: 01/28/2022 20:15:00 UTC
Last modified on: 02/04/2022 14:18:00 UTC