In version 1.2.6 and later, this issue has been fixed. This issue has been confirmed on versions 1.6.0 through 1.8.6, but may occur on other versions as well. The issue is confirmed to occur in the ‘Copy to clipboard’ functionality. A malicious javascript payload can be injected into the ‘Name’ parameter and will then be executed when pasted into other websites. --------------- In version 1.0.5 through 1.2.5, a XSS issue exists in the ‘Copy to clipboard’ functionality. When a victim accesses the recipes page, then adds a new recipe with a malicious javascript payload in the ‘Name’ parameter and clicks on the clipboard icon, an XSS payload will trigger. A low privileged attacker will have the victim's API key and can lead to admin's account takeover. --------------- In any of the affected versions, copy to clipboard functionality does not have any security restrictions on the ‘Name’ parameter. A low privileged attacker can inject malicious javascript into this parameter, leading to XSS vulnerabilities. --------------- Food information is stored in the browser's localStorage. An attacker can inject malicious javascript into this parameter and steal the victim's API key and other information. --------------- In versions 1.0.5 through 1.2.5, a XSS issue exists in the ‘Cook’ functionality. When a victim accesses the recipes page, then
The root cause
The root cause of the issue was a lack of input validation. If an attacker can inject malicious javascript into the ‘Name’ parameter and trigger an XSS vulnerability, they could steal the victim's API key and other information.
Fixing this vulnerability requires updating to versions 1.2.6 and later.
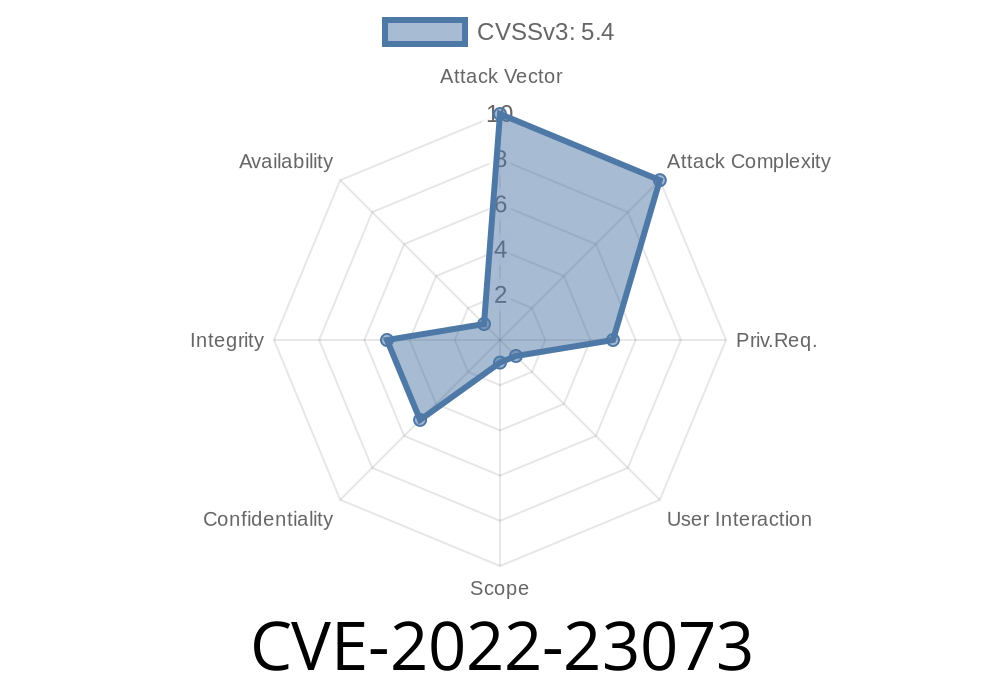
#1: CVE-2022-23073 In version 1.2.6 and later, this issue has been fixed. This issue has been confirmed on versions 1.6.0 through 1.8.6, but may occur on other versions as well. The issue is confirmed to occur in the ‘Copy to clipboard’ functionality. A malicious javascript payload can be injected into the ‘Name’ parameter and will then be executed when pasted into other websites.
How to detect if your site is affected by XSS?
There are a few different ways to detect if your site is affected by XSS.
Timeline
Published on: 06/21/2022 09:15:00 UTC
Last modified on: 06/28/2022 18:04:00 UTC