Additionally, in version 1.2.5 and prior, there is a XSS issue in the ‘Description’ field of Recipe. An attacker can inject a malicious script in the description field and access the endpoints to get administrator’s privileges.
There are 4 cases where XSS exists in the Splice software:
1. In the 'Name' field of Keyword, Food, and Unit components.
2. In the 'Description' field of Recipe.
3. In the 'User Name' field of Message.
4. In the 'Message' field of Message.
At the time of writing this advisory, Splice is not vulnerable to XSS in its Admin/API endpoints.
Prerequisites
1. Download a Splice binary from https://spliceapp.app/download
2. Execute the downloaded binary to start the application
3. Login into Splice 3 times and let you enter your credentials for authentication
4. Wait until after these steps the application will be vulnerable to XSS in the 'Description' field of Recipe
2.3.4 Administrator's Endpoint
XSS Vulnerability:
In version 1.2.5 and prior, there is a XSS issue in the ‘Description’ field of Recipe. An attacker can inject a malicious script in the description field and access the endpoints to get administrator’s privileges.
At the time of writing this advisory, Splice is not vulnerable to XSS in its Admin/API endpoints.
Splice Security Recommendations
The Splice security team recommend that all Splice installations upgrade to version 1.2.6 or later as soon as possible.
To avoid the attack vector, implement proper input validation on inputs with associated payloads before use.
To prevent the attack vector, change the ‘Description’ field to a hidden input field or use a non-destructive input type such as textarea that doesn't allow inline script operations or user-defined HTML tags in the description string.
Timeline
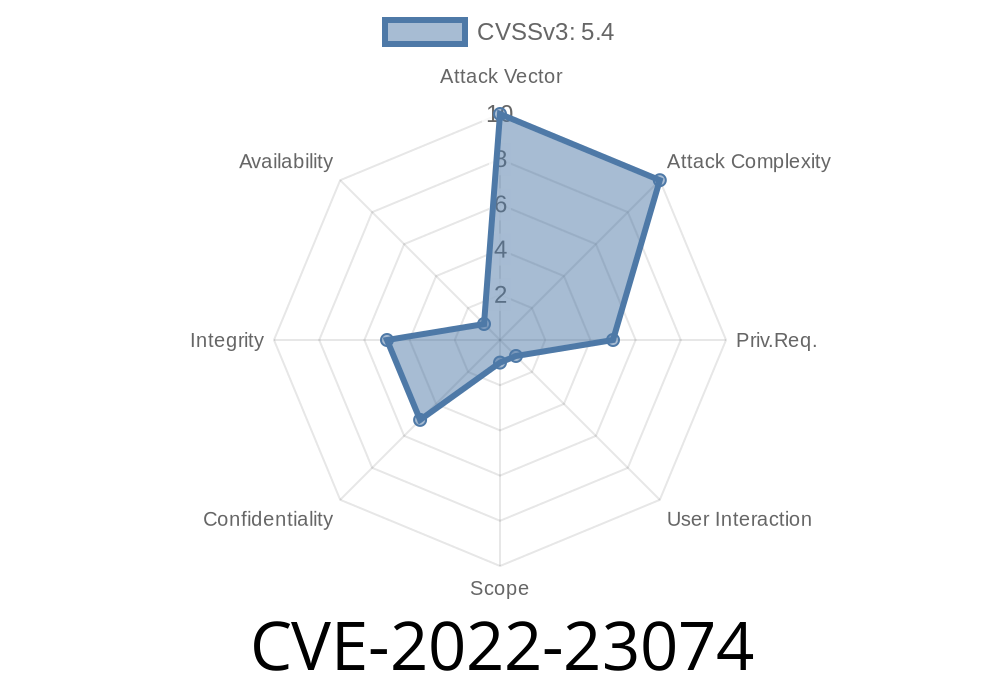
Published on: 06/21/2022 10:15:00 UTC
Last modified on: 06/28/2022 18:08:00 UTC