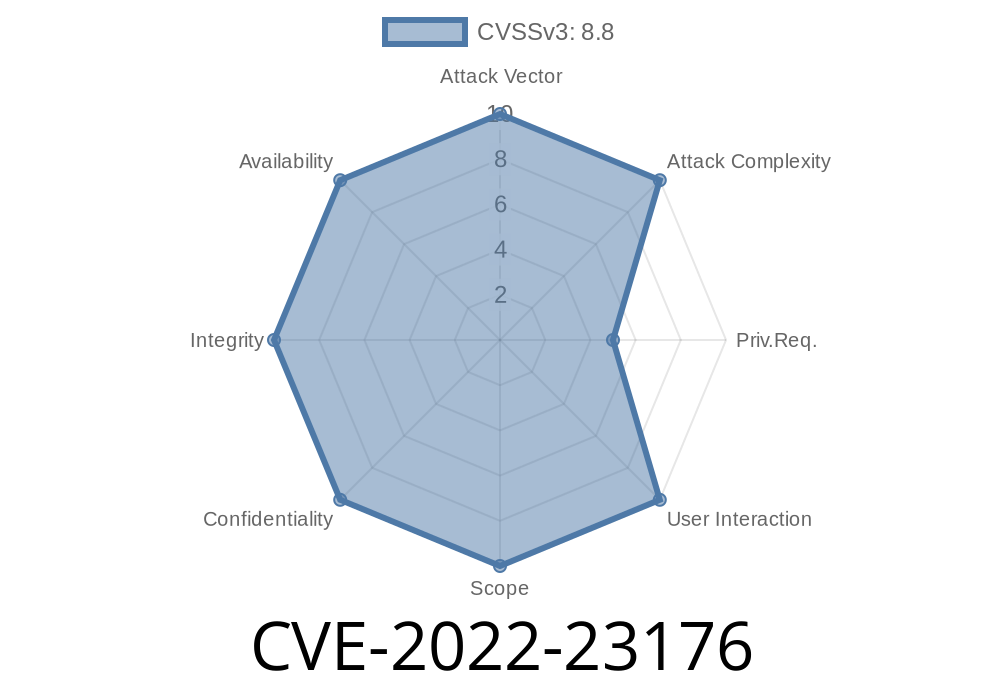
XTM before 5.4.1 allows a remote attacker to access the system with a privileged management session via insecure network access. XTM versions prior to 5.4.1 have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. A remote attacker may access the system with a privileged management session via insecure network access. XTM versions prior to 5X.X have a hardcoded root account password. This impacts XTM versions prior to 5X.X. XTM versions prior to 5.4.1 have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. A remote attacker may access the system with a privileged management session via insecure network access. XTM versions prior to 5X.X have a hardcoded root account password. This impacts XTM versions prior to 5X.X. XTM versions prior to 5.4.1 have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. A remote attacker may access the system with a privileged management session via insecure network access. XTM versions prior to 5X.X have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. XTM versions prior to 5.4.1 have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. A remote attacker may access the system with a privileged management
Security Requirements for XTM
For XTM versions prior to 5.4.1 and 5X.X:
- Use a password that is at least 8 characters in length and contains at least one lowercase letter, one uppercase letter, one digit, and one special character.
- Ensure the password does not have "root" as part of the password.
Operation Scenario
A remote attacker may access the system with a privileged management session via insecure network access. XTM versions prior to 5X.X have a hardcoded root account password. This impacts XTM versions prior to 5.4.1. A remote attacker may access the system with a privileged management session via insecure network access. XTM versions prior to 5X.X have a hardcoded root account password. This impacts XTM versions prior to 5X.X
What is XTM?
XTM is a web server and proxy. XTM is installed on a machine as an Apache module, written in PHP with MySQL support. XTM is used for load balancing, proxying traffic between servers, filtering, caching and caching reverse proxying.
New Features
The new features in the latest version of XTM include a revamped interface, enhanced scalability, and configuration options.
1. Updated Interface
The redesigned interface is an intuitive step forward. It’s easy to find and understand everything you need on the new interface when it comes to setting up your XTM product and making configuration changes. The layout is more intuitive, which makes it easier to use than before. There are also handy shortcuts that let you jump straight into a specific function, like logging in or configuring your product settings with the click of a button.
2. Enhanced Scalability
XTM now has the ability to scale quickly and easily with its enhanced scalability features and configurations. In once instance, we were able to set up three different tiers of pricing for our product as well as configure them so that each tier would have a different marketing budget allocation for their respective campaigns without any extra effort from us! This was fantastic to avoid any confusion going forward about how much we had allocated for each tier of pricing!
3. Configuration Options
We were able to make some minor adjustments by changing the price thresholds for certain products and services within the system without having to change anything major about our settings! This was especially helpful because if there was ever a time that we needed some extra marketing budget for one particular campaign, this was an easy fix because we could add it right away without any major work or reconfiguration needed!
Timeline
Published on: 02/24/2022 15:15:00 UTC
Last modified on: 04/18/2022 19:37:00 UTC
References
- https://www.watchguard.com/support/release-notes/fireware/12/en-US/EN_ReleaseNotes_Fireware_12_7/index.html#Fireware/en-US/resolved_issues.html
- https://securityportal.watchguard.com
- https://www.watchguard.com/support/release-notes/fireware/12/en-US/EN_ReleaseNotes_Fireware_12_1_3_U7/index.html#Fireware/en-US/resolved_issues.html
- https://www.watchguard.com/support/release-notes/fireware/12/en-US/EN_ReleaseNotes_Fireware_12_7_2/index.html#Fireware/en-US/resolved_issues.html
- https://arstechnica.com/information-technology/2022/04/watchguard-failed-to-disclose-critical-flaw-exploited-by-russian-hackers/
- https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2022-23176