This was discovered by researchers at Cisco Talos. The vulnerability affects Microsoft Windows and Office software. It exists in Active Directory authentication protocol and allows attackers to impersonate any domain user or domain computer with a low-privilege account when initiating a connection to a target network. Microsoft has released an update to close this vulnerability. You can install it by following the instructions provided in this FAQ. Microsoft also recommends applying this security update to all devices running Windows 7 and Windows 8.1. In case the update doesn’t work or you can’t apply it for some reason, you can protect your system with antivirus or by using a different remote access solution.
What is Active Directory Authentication?
Active Directory is Microsoft's directory service and Active Directory authentication is a protocol that controls access to a domain. It allows a user or computer to authenticate against the domain controller. This protects the domain from unauthorized users.
The vulnerability affects how Active Directory authentication works when initiating a connection to a target network. It exists in Active Directory authentication protocol and allows attackers to impersonate any domain user or domain computer with a low-privilege account when initiating a connection to a target network.
So, what does this mean? When someone attempts to connect on Windows or Office software that is vulnerable to this issue, they may be able to impersonate another user with any low-privilege account on the system they are attempting to access.
This means that an attacker could use this exploit to gain access and bypass security measures such as two-factor authorization or single sign-on (SSO).
How does the Active Directory Authentication Protocol Vulnerability work?
The vulnerability exists in the way that Active Directory authentication protocol initiates connections to a target network. When an attacker initiates a connection, they impersonate any domain user or domain computer with a low-privilege account when connecting to the target network. The vulnerability allows attackers to bypass authentication checks that are normally performed on incoming connections.
What is the Microsoft Windows Active Directory spoofing vulnerability?
"Microsoft has released an update to close this vulnerability."
In the Active Directory spoofing vulnerability, a low-privilege account can impersonate any user or computer in the domain. This means that attackers with access to a low-privilege account are able to impersonate any user or computer on the network they're connecting to. For example, if an attacker has access to a low-privilege account on your network, it could allow them to impersonate your administrative account on other networks they're connected to. The security update fixes this vulnerability by addressing how passwords are validated during authentication attempts.
How to Detect If You Are Vulnerable?
If your system has the latest update installed, you don't need to worry about this vulnerability. If your system is still vulnerable, you can use these instructions to detect if it is present and close it:
1. Open a command prompt in administrator mode.
2. Type "winver" and press enter.
3. Look for the line that reads either "Windows 10" or "Version 1803"
4. If the version number is 3 or greater, congratulations, you're safe! If not, you'll need to apply Microsoft's security update as soon as possible before attackers can take control of your computer.
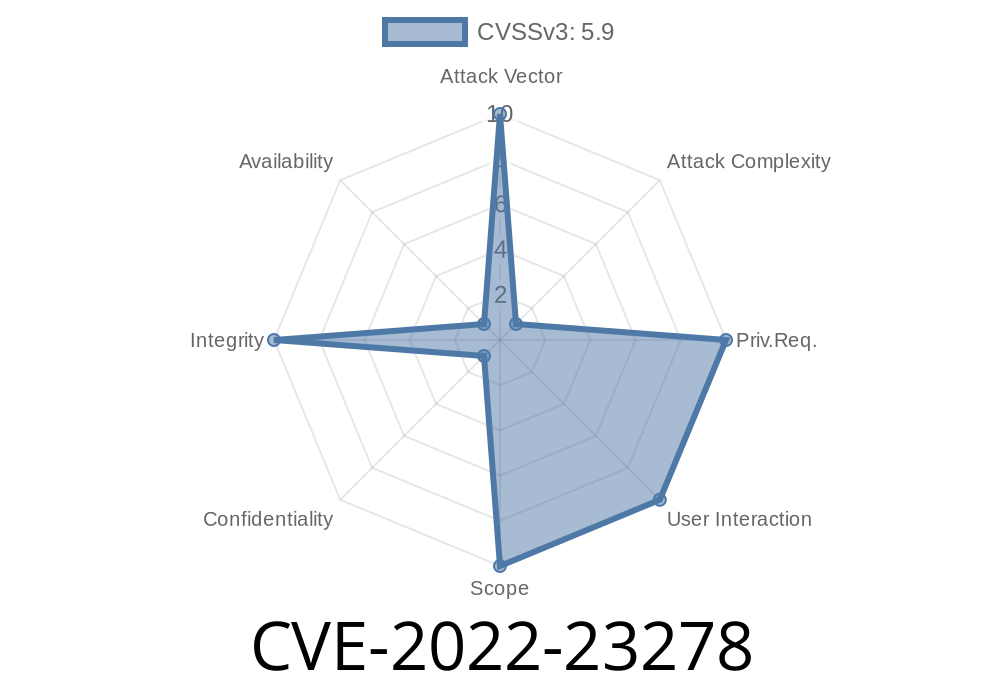
What is CVE-2022?
CVE-2022 is a vulnerability in Active Directory authentication protocol that was discovered by researchers at Cisco Talos. This vulnerability affects Microsoft Windows and Office software.
The vulnerability exists in Active Directory authentication protocol and allows attackers to impersonate any domain user or domain computer with a low-privilege account when initiating a connection to a target network.
Microsoft has released an update to close this vulnerability; you can install it by following the instructions provided in this FAQ. It also recommends applying this security update to all devices running Windows 7 and Windows 8.1. In case the update doesn’t work or you can’t apply it for some reason, you can protect your system with antivirus or by using a different remote access solution.
Timeline
Published on: 03/09/2022 17:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC