The flaw exists due to the improper handling of memory allocation during the process of loading user-mode code into the kernel. An attacker can leverage this vulnerability to execute code with elevated privileges on the targeted system.
The security update addresses the vulnerability by validating whether user-mode code is loaded into the kernel.
Microsoft released security bulletin MS16-064 to address the issue in Windows.
* Update Windows 7 or Windows Server 2008 to the latest version.
Can you install VMWare Workstation to test the security update in Windows?
An attacker can exploit this vulnerability to execute code with elevated privileges on the targeted system.
End users should ensure they have installed the latest update to reduce the risk of exploitation.
SOL64374 - Windows NT OS Kernel Elevation of Privilege Vulnerability - end user.
CVE-2016-0034 - Windows NT OS Kernel Elevation of Privilege Vulnerability - vendor.
To exploit this vulnerability, an attacker must force the user to open a malicious file.
An attacker can exploit this vulnerability to execute code with elevated privileges on the targeted system.
End users should ensure they have installed the latest update to reduce the risk of exploitation.
MISC - Vulnerability in Windows Data Access Components Could Allow Elevation of Privilege Vulnerability - vendor.
To exploit this vulnerability, an attacker must force the user to open a malicious file.
An attacker can exploit this vulnerability to
Windows 10 (Build 14393 and Up)
The security update addresses the vulnerability by validating whether user-mode code is loaded into the kernel.
Microsoft released security bulletin MS16-064 to address the issue in Windows.
* Update Windows 7 or Windows Server 2008 to the latest version.
Can you install VMWare Workstation to test the security update in Windows?
An attacker can exploit this vulnerability to execute code with elevated privileges on the targeted system.
End users should ensure they have installed the latest update to reduce the risk of exploitation.
Timeline
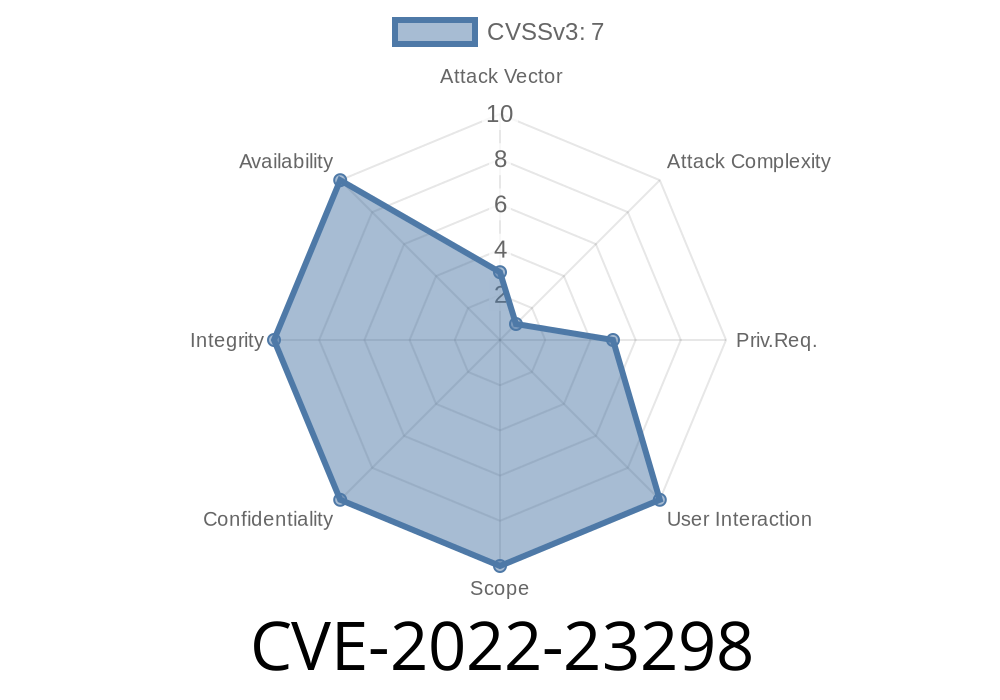
Published on: 03/09/2022 17:15:00 UTC
Last modified on: 05/23/2022 17:29:00 UTC